Development Trends of Smart Cities in the Future – Potential Security Risks and Responsive Solutions
Volume 5, Issue 4, Page No 548–556, 2020
Adv. Sci. Technol. Eng. Syst. J. 5(4), 548–556 (2020);
 DOI: 10.25046/aj050465
DOI: 10.25046/aj050465
Keywords: Security, Risks, Smart cities, Development Trends
Smart cities are an indispensable development of the ongoing urbanization process world- wide. Currently, smart cities are being built and deployed by countries in the first steps. Based on research on the current state of developing smart cities in the world, the author forecasts the future development trends of such cities, pointing to one of the major challenges for cities. It is a problem that responds to potential security risks. Identifying potential risks for coping solutions is essential for the future of smart sustainable cities. Main solutions include policy and law solutions, technology solutions and raising the peoples standard were given in the article.
1. Introduction
Before the industrial revolution, most of people in the world lived in rural areas. In 1800, only 3% of the world’s population lived in cities. By 1900, there were 12 cities with a population of over
1 million but most people lived far away from urban centers [1]. Wellington Eweb – the former mayor of Denver city, Colorado, emphasized: “The 19th century belonged to empires; the 20th century belongs to nations. The 21st century will belong to cities”. Nowadays, in developed countries, 70% of the population lives in cities, meaning more than 50% of the world’s population lives in urban areas. By 2050, 70% of the worlds population will have lived in urban centers [2]. The unprecedented urbanization is taking place globally that creates tremendous pressure on infrastructure, houses, environmental services, health care, energy … to meet the living needs of current and future generations. In the context of the 4th industrial revolution that has been taking place, the construction and development of smart cities is the indispensable result towards valuable, livable, resilient, environmentally friendly and sustainable cities.
Smart cities are places where information technology is combined with infrastructure, architecture, daily appliances and even the human body to solve economic, social and environmental issues [3, 4]. Smart cities mean the maintaining continuity of security, privacy, system robustness and the availability of services. The problem is that most of the smart cities are created by the use of real and virtual connectivity technologies, so smart cities will become the potential target of cyberattacks. Ensuring the safety of resources and privacy of citizen data is the top concern in all smart city projects. In addition, smart cities also face many other security threats such as terrorism, population growth rate, monetary and financial security, increase of social inequality, human security due to the development of artificial intelligence.
Currently, experts and scientists have been paying much attention to research on smart cities even though the construction and development of new smart cities is at the very first stage of formation. However, such studies mainly focus on building and designing smart city models, foundations, principles, applications in economic development, social balance, environmental protection. Studies on the security of smart cities are mainly mentioned in general. The issue of ensuring smart city security is mostly studied in terms of cyber security ensuring, meanwhile in fact, although information technology is the basic foundation for building a successful city, operating a city safely requires abilities to cope with many other risks that may threaten the life and safety of people in the context of globalization.
The writers aim at providing an overview of smart cities, the development trend of smart cities in the future, pointing out the risks that threaten security of smart cities. On that basis, the authors recommend a number of solutions. To obtain research results, the authors have consulted with many experts in the field of security science and information technology experts. In fact, the study of building smart cities based on the approach and thinking of information technology experts is different from that of experts in the field of security. Therefore, combining different opinions of such experts together with the process of researching, analyzing, synthesizing related documents and data as well as participating in some international conferences, the writers have summarized and presented the results of the research.
The subject of the study is the building and development of smart cities all over the world. From studying this process, the authors point out future development trends of smart cities, and assess the potential risks related to national security in the construction of smart cities. The goal of the study is to provide appropriate solutions to deal with potential security risks to smart cities in the future. To achieve the results of the research, the authors focus on using the expert method along with the consultation and research on documents of many experts in the field of security science and information technology. In fact, the study of building smart cities based on the approach and thinking of information technology experts is different from that of experts in the field of security. Therefore, combining different opinions of experts together with researching, analyzing, synthesizing many related documents and data, participating in some international conferences and conferences, the author has summarized and presented the results of the research. At the same time, the authors use a case study method based on the survey of the implementation and construction of some smart cities in the world. Specific examples of building and implementing smart cities around the world will clarify the research problem.
2. Awareness of Smart Cities
Mankind is entering the early stages of the 4th industrial revolution with an unprecedented speed of development and outstanding achievements such as artificial intelligence, IOT, big data, sensors anywhere and anytime, robots, real – virtual connections. Making a qualitative change in all fields. Today, more than half of the worlds population lives in cities, and this number will continue to grow as cities have always been a motivation of economic growth. The speed and extent in which cities deploy technology with flexible policies will be highly competitive. Therefore, towards building and developing smart cities is an inevitable trend of the 4.0 revolution era.
The concept of smart cities has been known since 2009 originated from the proposal of IBM Corporation (USA), but until now most countries in the world have still been in the early stages of developing smart cities because of many technological factors, modifying the model according to development needs and depending on financial resources to comprehensively develop this model. Every year, there are still charts of smart cities in the world and the ranking position changes annually depending on the development of each region, continent as well as each city. However, “what is a smart city?” is the question that does not have a common answer [5]. Bruno Pete, IBI Group Smart City Task Force Lead in the “Top 10 Smart city success factor”, defines: “In general, a smart city is a city or region that can increase its competitiveness and quality of life, efficiently use resources, and support economic sustainability by using technology and creativity to raise the IQ of the built environment. Further, it is a city that uses innovation to address the needs and desires of the community, puts the citizens first and ultimately breaks down the barriers between agencies and departments, and between people and government” [5]. Researcher Nguyen Van Thanh – Deputy Minister of Public Security of Vietnam said that in order to have a full concept of a smart city in our minds, we need to recognize the city as an ecosystem, so he gives a definition: Smart cities are cities that use integrated system control tools to connect the real world and the virtual world, mainly systematic thinking. Their means are information technology and the media; their objective is to build a valuable, energetic, resilient, and competitive city; their measure is the satisfaction of community; their criteria are security, welfare and safety indicators of social, economic and environmental factor of high standards [6]. Many other authors give different definitions due to different approaches, while also determining the factors that identify what the standards of a so-called smart city are [7, 8]. Common factors include accessibility to public transport, smart buildings, energy efficiency, environmental friendliness, policy effectiveness and governance, and high-tech presence [9, 10]. In this regard, the authors agree with Brettking in “Augmented: Life in the Smart Lane” (one of the two books that Chinese President Xi Jinping read to get ideas for the national AI strategy of China). He did not give a definition of a smart city, but he thought that the comprehensive definitions should include the following factors:
- Urban areas are using information and communication technologies to improve urban service efficiency, reduce costs and resource consumption, encourage citizens to participate in such efforts.
- Specific industries are being transformed by technologies including public services, transport management, energy, healthcare and air and water pollution reduction.
Smart cities are judged not only by their services to citizens, but also by their ability to respond to serious problems like natural disasters and the ability to make use of daily resources. A truly smart city will have to be redesigned from scratch, in an urban environment which makes use of technology to improve people’s lives, create jobs, transport systems and smart lives, in order to create a positive impact on the environment.
3. Development Trends of Smart Cities
IESE Business School, Navarra University, Spain conducted a survey on 165 cities in 80 countries and analyzed, evaluated based on 9 aspects: human resources, social cohesion, economy, environment, management, urban planning, international access, technology, mobility and transportation. As a result, the smartest cities have been selected, including: New York, London, Paris, Reykjavik, Singapore, Seoul, Toronto, Hong Kong, Amsterdam [11]. Although the development of new smart cities is in the early stage, many cities have implemented effective new services on data platforms. Klaus Schawab – the founder and executive chairman of the World Economic Forum, emphasizes that this is the 10th out of the 21 major shifts of the world under the impact of the 4th industrial revolution [12]. The development trend of smart cities in the near future can be generalized as follows:
Firstly, building and developing smart cities will become more and more popular and will be the goal of many countries in the world.

Figure 1: Illustration of services of a typical smart city [13]
Urbanization has been boosting economic growth, but it has also exposed many cities to housing, infrastructure and service challenges to meet the demand of a growing population. With more and more challenges, the application of new technologies to solve the problems is becoming more and more popular. To solve such problems, cities are required to be smarter. Therefore, smart cities will be a popular trend of many countries around the world. They will bring high quality living standards for everyone with a focus on several key aspects such as smarter environment, smarter mobility, smarter connectivity and smarter management.
Secondly, typical smart services will be provided by smart cities in the future.
The goal of smart cities is to create a sustainable urban environment by taking advantage of solutions based on information and communication technology, thereby providing better services to the people. The concept of smart services in smart cities remains abstract [14]. The article focuses on the trend of using typical smart services of smart cities in the future as follows:
- Smart management
New AI tools for future smart cities will soon improve the transparency and efficiency of city government as well as urban planning and design processes. Citizens’ participation through social media and personal smart devices is indispensable for smart cities. Smart cities will set up dynamic communication channels. Planning will be changed from a linear process directed by the government to a process of collaboration, cooperation with citizens, leading to more open design, able to meet the participation of the general public.
- Smart traffic system
It is impossible to have a smart city without developing a
smart transportation system. Smart transport is the cornerstone of a smart city. With advances in sensors, optics and integrated processors, improvements in pedestrian safety and rudimentary vehicles will promote the use of public transport, reduce congestion and pollution, improve health, make travelling faster, more predictable, and less expensive.
In terms of public transport: Trolleys and small self-operated cabins will go around school campus and shopping areas to take people to trip-sharing locations or public transit stations. Public transport will be optimized based on demands, events, weather and other factors, all of which will be reacted in real time and controlled by AI. Parking lots and garages will gradually disappear as they become obsolete and operating internal combustion engines become more expensive. Buses and trains will become automated because of AI as well as integrated dynamic scheduling and routing capabilities. When AI starts driving buses and trains, they can work longer without getting tired or asking for overtime. Electric transport systems and automated electric vehicles will also save maintenance and operation costs. Public transport systems will use solar energy, reducing carbon emissions for the city. Costs paid to drivers are eliminated and electric motors will require less maintenance than internal combustion engines and associated steering systems. Intelligent transportation in the future will not only meet the needs of transportation and travelling of people but also greatly reduce the costs compared to the present [1, p. 313]. Traffic management system will be smart to manage traffic lights, roundabouts and traffic density. Sensors will be used in the parking lot, garage and roadside to report vacancies in real time via websites. This technology has now been applied very effectively in the Netherlands and some other countries. Street ecosystems will change to facilitate self-driving electric cars.
In terms of personal transport: The design of cities for selfdriving cars will be a popular trend in the near future. Cities will need less parking lots when people start to share car ownership. Even some cities will restrict manned vehicles or charge people because they will not be as safe as AI drivers, and cities will be in charge of injuries related to transportation.
- Smart Electricity and Water System
The future smart grid system deploys networked sensors and measuring devices to collect real-time system data from power generation, transmission and distribution systems. A central analysis tool receives this data through the communication network and sends control commands to smart electronic devices on the scene [15]. New generation LED street lights can serve as the basis for many sensor technologies to collect data on weather, pollution levels, seismic activities, movement of vehicles and people. By connecting such smart street light system into a network, we will know what is happening to the whole city in real time and provide lighting solutions in the areas of public safety [16].
The intelligent water management system integrates sensors, controllers and analytical elements to ensure that water is circulated only when and where it is needed. It also carries out real-time monitoring of water quality [15]. Applying Internet to water pipes, using sensors in water systems to monitor the flow thereby managing the entire cycle, providing sustainable water supply for the needs of people and ecosystems.
- Smart Energy
Renewable energy plays an important role in reducing air pollution, reducing costs, and increasing the ability to restore reserve energy. Potential alternative energy systems for future smart cities include: distribution networks that can withstand terrorist attacks and natural disasters; fuel cell storage production system; modular small thorium reactors; renovating high-rise buildings with transparent solar batteries; coastal cities with living embankments which are able to produce energy from tidal forces [1, p. 315].
- Smart Healthcare System for Citizens
Smart healthcare systems are becoming more and more popular in urban areas, especially when obesity is on the rise in rich countries such as the United States and the United Arab Emirates, which leads to an outbreak of diabetes and expensive health care costs. An intelligent healthcare system will provide health services by taking advantage of sensor infrastructure in smart cities. Instead of promoting the treatment of various diseases and symptoms, the smart health care system will focus on the use of technologies such as genotypes, biometric monitoring, microcirculation and testing based on chips in laboratories, assessing risk for each individual to help prevent diseases or stimulate behavior changes.
The smartest cities of the future will build a healthcare system in parallel with sensor-based factories and AI-based private health databases to reduce the burden of long-term healthcare. Technologies such as gene therapy, personal drugs and smart drugs will undoubtedly become part of the treatment.
- Smart Pollution Reduction
Water and air pollution is a major challenge for modern cities. New smart sensor technologies can be designed to be compact, connected to mobile devices, helping municipalities monitor pollution levels and reduce costs related to health and well-being by pollution. Smart cities will monitor pollution levels and take action to achieve a safe state. When connected to a smartphone, air pollution sensors create an environmental map from crowdsourced data and provide it to citizens for free. In addition, new types of water purifiers for households or the community can eliminate most dangerous chemicals and parasites. Smart cities can also equip necessary equipment in case of water pollution due to natural and man-made disasters. Smart materials and nanotechnology will allow us to create an efficient filtration system that cleans air and water with a much lower investment than that of today.
- Smart emergency response system
Cities often cope with many emergency situations or natural disasters. Therefore, smart cities can address emergencies by requiring relevant agencies to have smart devices with high resilience to deal with risks. Future smart cities will use a predictive model to alert city leaders about imminent problems instead of just reacting after the incident has taken place. The system can be pre-programmed to send notifications, enable tasks, automatically send orders and task lists to relevant organizations, as well as check the reception, processing and completion of these tasks. Moreover, the system will receive messages and other input from citizens about the state of emergency, which allows any citizen to actively contribute to the safety and functioning of the city.
Thirdly, typical future smart city models
Each country, each city chooses a different smart city model based on geographical conditions, history and related factors. Some typical smart city models in the future can be summarized in the Table 1.
| Future smart city models | Cities successfully apply the models |
| City Development Strategy | Amsterdam, London |
| Green City | Reykjavik |
| Eco – City | Toronto |
| Garden City | Dubai |
| Ecological as Economic City | Singapore |
| Sustainably developed city | Paris |
| Livable City | New York |
| Resilience City | Tokyo |
| Digitalized urban | Hong Kong, Seoul |
Table 1: Classification of smart cities
4. Potential Security Risks of Smart Cities
Smart cities are the totality of integration, collection, and information sharing through smart devices and sensors. The city’s smart information system is a combination of wireless and wired infrastructure. On the basis of data collected, smart cities use smart software tools to improve management efficiency and provide intelligent services. However, smart infrastructure of the smart cities opens up a huge attack surface, which is a collection of all known and unknown vulnerabilities, including the existing security controls on all subsystems and networks [14, 17]. The overall connectivity of a smart city helps criminals conditionally launch large-scale attacks that violate the security and privacy of individuals, organizations and city governments. The risks of insecurity first come from the fact that many application products are not capable of security (for example, automation control software vulnerable to hacker attacks). Meanwhile, managers do not or are not able to test security features of products and systems, resulting in a gap that still exists for hackers to exploit and attack on a large scale when solutions are connected on the Internet. Typically, there are security threats with some key smart city services.
Smart traffic with the development of self-driving cars could make these cars vulnerable to theft and attack from afar. Attackers may control one or more self-propelled vehicles to cause them to collide. Unlike general-purpose computing devices, installing security software for self-driving cars is often more expensive and complicated. Features such as Internet access while on the move significantly increase the vehicle’s attack surface. The use of mobile technology and bluetooth in modern vehicles increases the risk of remote attacks. Devices in self-driving cars that can receive signals from outside are susceptible to signal interference, attackers can intercept and modify security-related data because it is connected via a network. Actions such as sudden braking, speeding, changing lanes, or changing direction when being attacked may result in a collision with another vehicle.
Intelligent water and electricity systems will be dependent on smart infrastructure. The entire city’s electricity system, if attacked, could have serious consequences. At that time, the traffic lights will not work, self-driving vehicles will lose control and endanger human life. These infrastructures have holes which are once exploited can make the operation of the whole system affected. Automaticallymeasured parameter readers which are widely used in smart water and electricity systems without basic security measures can directly affect the confidentiality, integrity and authenticity of data. Moreover, some of them periodically transmit its data about energy use via inherently insecure wireless links. Attackers can capture such data by using simple techniques to identify uninhabited neighborhoods or identify citizen habits. Monitoring and data collection control systems are widely used in water distribution and sewage treatment plants are primarily designed to maximize functionality, thus security issues are often taken into account. Attackers can use simple techniques to capture or modify traffic between central control units and field units. Besides, but another threat to the smart water and electricity system is the issue of sensitive information related to the sitemap, details of chemical processes, web security plans, etc. for water and electricity control networks that are prone to service disruption, leading to public safety problems.
Smart management systems and many other smart services can lead to a great deal of citizens’ information being collected, jeopardizing their privacy. Typically, smart healthcare services can make it possible to collect an unprecedented amount of information. Moreover, based on the data collected, one can guess the habits of citizens, their social status, basic information, a lot of sensitive information. And when they combine with medical information, the issue of security and personal safety will become even more serious [18, 19].
It can be said that the issue of ensuring security and safety of smart cities is a difficult challenge and a difficult problem that governments need to solve when building these cities. All are tied together on the Internet. If there is no effective security strategy, cities will be quickly paralyzed due to vulnerabilities hacked by hackers.
5. Proposed Solutions
The process of urbanization will make existing cities uninhabitable in the coming time, therefore, despite the challenges, the development and construction of smart cities should not be delayed any more. All of these security challenges have put pressure on urbanization to adjust to form a number of more livable and more sustainable cities. These challenges make urbanization addressed by smart solutions [20, 21]. Basic issues related to future smart cities’ security which need to be ensured are generalized in the figure 2.
A city which can carry out these solutions is becoming smarter. From the studies, the authors propose some following solutions:
Firstly, solutions for policy and law making in the field of security and safety for smart cities.
The number of cyberattacks increasing every day create favorable conditions for criminals to launch large-scale attacks to violate security of resources and data. Therefore, policy making, planning and implementation of security measures are extremely important for a smart city. Smart city governance in general and policy and law making, implementation of management measures to ensure security and safety for smart cities are different from traditional governance. Policies, laws on governing and security measures of smart cities require stability, transparency and high predictability to adapt to drastic changes of technology.
These policies and measures require a reasonable balance between the costs and benefits of each technology, and socio-economic development and security of city. It is very important to study and analyze the requirements of the security of smart cities based on their common infrastructure with the interdependence among different branches exist in that city, hence, identify security risks as a basis for designing intelligent security measures to help detect and prevent risks. Smart cities can handle risks by avoiding them, applying control measures or transferring these risks to third parties such as insurance, software creation, etc. [14].

Figure 2: Basic Issues Related to Future Smart Cities’ Security which need to be Ensured
Security policies and measures need to be constantly changed in accordance with infrastructure changes. New holes and new threats need to be promptly detected. Vulnerabilities may be technical and technological flaws that exist due to loopholes of softwares and hardwares as well as management flaws due to the inconsistency of security policies and procedures. Identifying the vulnerabilities and their severity allows people to prevent them. Such vulnerabilities often lead to security incidents. Therefore, it is important to detect, report and activate appropriate control measures to minimize and recover the impact of the incident caused by the vulnerabilities. Citizens should be encouraged to report incidents that need to be handled. It is necessary to have a complete form of relevant information to create detailed and convenient records for remediation. Attention should be paid to the development of cybersecurity policies and procedures, and the selection of appropriate hardware and software tools for security ensuring. The procedures should be guided in detail with documented forms.
It is essential to create specific cybersecurity parameters, suitable to the conditions of each smart city. This issue was mentioned by Nguyen Van Thanh – Deputy Minister of Vietnam Ministry of Public Security and Do Quang Hung in Building and developing smart cities to ensure security, safety and safety indicator in the context of the 4th industrial revolution. The security indicators the author pointed out include: human security, business security, financial and monetary security, block chain, food security, national security (including cities), cybersecurity, big data analysis, ethnic, religious, and social security. The two authors also pointed out the indicators related to security assurance: The social security index includes sustainable economic development, improvement of resilience, life quality and social equality ensuring, application of digital technology, health care, education, culture, friendly environment, access to urban services, and public transport; safety indicators include crime reduction, medical safety, food safety, traffic safety, environmental safety, water safety, air safety, personal property safety, personal information safety, production safety, business, competition and safety against fire, explosion, and rescue
[6].
In addition, it is necessary to build and manage a flexible and certain legal framework to receive new technologies and business models, and protect the rights of relevant parties. Due to the transnational nature of non-traditional security threats, when building a smart city, nations and ethnic groups need to accept the common rules or have to adjust their legal systems towards internationalization. Cities need legislative policies that facilitate innovation, promote smart technologies and services, but at the same time minimize risks. It is necessary to strengthen cybersecurity management and strictly and promptly handle violations on the cities’ security.
Secondly, technology solutions for security ensuring of smart cities. Smart city technologies are not only related to people who settle in cities but also have a very important impact on the prosperity of an area since smart cities are the driving force for economic development. As the global population grows and more and more people migrate to cities, the security forces and the police cannot be sufficient to ensure security effectively. Therefore, to help them, law enforcement agencies around the world need to use increasingly advanced applications of modern technology to keep confidentiality.
Smart cities which desire to succeed and develop sustainably need to apply technology such as artificial intelligence in public security and safety. This is a great lever in ensuring the safety of public assets, and more importantly the safety of people in the city. It is necessary to improve interoperability of network infrastructure, thereby improving connectivity among government departments; between governments and businesses and citizens. Here are some ways that smart cities can apply to ensure security and safety for the city:
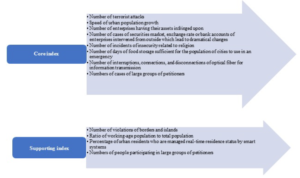
Figure 3: Smart cities’ security indexes [6]
Pay attention to expanding smart camera system, data management, and intelligent video surveillance. The use of surveillance cameras is a solution that brings tremendous economic and social benefits by preventing the daily occurrence of events or scheduled or extraordinary events. They will help the cities react quickly to any situations, ensure smooth traffic and many other issues. The priority locations for installing cameras in smart cities should include: Central areas; hot spots and important events; public parking lots; parks, squares. One problem is how to have enough people to monitor the entire surveillance cameras throughout the city to promptly handle and act against arose situations. The limitations can be easily overcome with the help of video analysis, in which real-time footage is analyzed with deep learning AI. Any irregularities can be identified by this system and reported to nearby staff immediately. This can help to respond quickly to crimes or even prevent many offenses.
Use different types of IoT sensors to monitor the crowd, especially in shopping areas, busy intersections, to detect potential security incidents. For example, scanning devices can detect objects made of certain materials and distinguish their shape, even if they are hidden from view. AI algorithms can analyze this scanned footage in real time to determine if these objects are harmful. If any potentially lethal object is identified, security personnel can have further inspection. In addition, crowd monitoring systems powered by IoT and AI can also track in important places, such as footsteps. These systems can ensure that bridges are always optimized and safe to those who use them. IoT-enabled systems can alert those present as well as the governments when such places have a tonnage beyond the allowed threshold and begin to take appropriate action.
Restrict access to high security areas such as airports, banks, power plants, government data centers and military bases by using technologies such as IoT and AI. Security systems, security gateways provided by IoT can ensure that only authorized persons can access the main government facilities. Multi-factor authentication, which may include biometric scanning, can be used to add even more security layers to the most sensitive parts of those facilities.
Make transportation more secure through the use of IoT in safe ticketing by embedding RFID technology. In fact, RFID activation tickets have been used for the 2018 FIFA World Cup, which helps speed up the ticket inspection process despite a large number of fans without compromising security. In addition, tickets can be stored digitally in everyone’s smartphones, which are able to automatically connect with security systems and automatic turnstiles at airports to allow only the right people to enter without security guards. This allows more effective use of security personnel and keep them wait for more serious situations.
Increase use of patrol robots and drones. Use robots as security guards which can patrol the streets of smart cities and identify potential threats with the help of advanced sensors and cameras. They can prevent crimes with their mere presence and can perform basic security tasks such as crowd control and search, sometimes more effectively than humans. Security personnel can stand still and participate only when situations escalate. Similarly, drones can be deployed to monitor public places and report to nearby security personnel in case of a potential public safety risk. This has been effectively applied by a number of countries in checking people wearing masks and other violations to prevent the spread of the Covid-19 epidemic, such as the use of drones in China and the use of robots in Thailand [22, 23].
Thirdly, solutions to improve people’s intellectual and technological levels to build and operate smart cities well. Building a smart city requires not only the application of smart technology products, but more importantly building a civilized community so that smart governance measures and services can be used effectively. The people are the ones who are served. At the same time, it is also one of the most important actors when building a smart city.
Indispensable condition is peoples ability to receive “smart” factors of the city. People must ensure enough financial sources to invest in technology and equipment to absorb the intelligence of the city. The regional people’s awareness must be at a high level to use the system of technology and equipment invested, along with voluntary cooperation, action and sharing. The second condition is to have experts loyal to the common interests to operate the systems of the smart city. Besides, the city needs to have “intelligent government” and “smart leadership”, hence, having the right and appropriate investment and mobilizing all investing sources as well as operate smart cities, creating a connection in the implementation of the set goals [24].
6. Conclusion
The world has been speeding up the development towards smart cities. Smart cities bring many benefits to the community, environment and society. People’s life quality in smart cities will be enhanced thanks to the benefits when cities eliminate greenhouse gas emissions; find out solutions to crime prevention, intelligent and time-saving transport, housing and energy-saving options; deploying intelligent medical solutions to improve life expectancy; create jobs; to save costs and facilitate the implementation of sustainable development targets. The author’s research points out that smart cities development will become more and more popular and be the goal of many countries in the world. Simultaneously, the authors also emphasize some typical smart services provided by smart cities in the future including smart management, smart traffic systems, smart water and electricity systems, smart energy, smart healthcare systems for urban residents, smart emergency response systems. The research also synthesizes some typical future smart city models including: City Development State; Green City; Eco City; Garden City; Ecological as Economic City; Sustainably Developed City; Livable City; Resilience City; Digitalized Urban.
It is indispensable for the process of changing to a smart city to have security measures and solutions built to adapt and support its operation. In the entire process, information technology is only a tool to help a city solve one or more specific problems rather than the development goals of the city. The authors have suggested a number of basic solutions to cope with the security threats of smart cities including: Solutions on policy and law making in ensuring security and safety of smart cities; technology solutions to ensure security for smart cities; solutions to improve people’s intellectual and technological levels to effectively build and operate smart cities. Therefore, the development and construction of a smart city with security ensuring is not only based on technological solutions, but also in a synchronous and unified manner for immediate and long-term solutions to ensure sustainable development of the city, meeting the inevitable future demands of the drastic urbanization process that has been taking place all over the world.
Conflict of Interest
The authors declare no conflict of interest.
Acknowledgment
This work is supported by scientists of People’s Security Academy and Ministry of Public Security of Vietnam.
- B. King, “Augmented: Life in the Smart Lane”, Marshall Cavendish Interna- tional (Asia) Pte Ltd, June 7th 2016.
- UNICEF/Periscope Study, 2020.
- A. Toffle, “The Third Wave”, (page 17), Bantam, 1984.
- A.M. Townsend, “Smart Cities; Big Data, Civic, Hackers, and the Quest for the New Utopia New York”, New York, W.W.Norton and Company, Inc., 2013.
- D.L. Chang, J. Sabatine-Marques, E.M. da Costa, P.M. Selig, and T. Yigit- canlar, “Knowledge-based, Smart and Sustainable Cities: A Provocation for a Conceptual Framework,” Journal of Open Innovation: Technology, Market, and Complexity 4(5), 117, 2018. DOI: https://doi.org/10.1186/s40852-018-0087-2
- NguyonV ̈anThˇanh, D.Q. Hung, “Building and developing smart cities to en- sure security, safety and safety indicator in the context of the 4th industrial revolution”, National Political Publishing House, 2018.
- D. Washburn, U. Sindhu, S. Balaouras, R.A. Dines, N.M. Hayes, L.E. Nelson, “Helping CIOs understand “smart city” initiatives: defining the smart city, its drivers, and the role of the CIO”. Forrester Research. Inc., Cambridge, 2010.
- H. Partridge, “Developing a human perspective to the digital divide in the smart city”, In Proceedings of the Biennial Conference of Australian Library and information Association, Queensland, Australia, Sep 21-24, 2004.
- V. Albino, U. Beradi, R.M. Dangelico, “Smart cities: Definitions, dimen- sions, performance, and initiatives”, Journal of urban Technology, 2015. DOI: https://doi.org/10.1080/10630732.2014.942092
- K. Kourtit, P. Nijkamp, “Smart cities in the innovation age. Innova- tion”, The European journal of social science research, 2012. DOI: https://doi.org/10.1080/13511610.2012.660331
- B. Cohen, “The Smartest Cities in The World”, Fast Company (November 20, 2014), https://www.fastcompany.com/3038765/the-smartest-cities-in-the- world [Accessed November 29, 2018].
- K. Schwab, “The Fourth Industrial Revolution”, World Economic Forum, Currency pp. 11 (January 3, 2017).
- Data, Energy, And The Smart City: A Conflicting Relationship, 2019, Online Avaliable: https://www.smartdatacollective.com/data-energy-and-the-smart- city-a-conflicting-relationship/
- A. Bartoli, J. Hernandez-Serrano, M. Soriano, M. Dohler, A. Kountouris, D. Barthel, “Security and privacy in your smart city”, Proceedings of the Barcelona smart cities congress 292, 2011.
- H. Song, R. Srinivana,T. Sookoor, S. Jeschke, “Smart Cities: Foundation, Principles and Applications”, John Wiley and Sons, Inc, 2017.
- World Economic Forum, global conference on cities future, 10 best initiatives in urban renovation of October, 2015.
- A. S. Elmaghraby, M. M. Losavio, “Cyber security challenges in smart cities: Safety, security and privacy”, Journal of advanced research, 5(4):491497, 2014. DOI: https://doi.org/10.1016/j.jare.2014.02.006
- D. Rebollo-Monedero, A. Bartoli, J. Herna`ndez-Serrano, J. Forne`, M. Soriano, “Reconciling privacy and efficient utility management in smart cities”, Trans- actions on Emerging Telecommunications Technologies, 25(1) 94-108, 2014.
DOI: https://doi.org/10.1016/j.jare.2014.02.006 - Z. Khan, Z. Pervez, A. Ghafoor, “Towards cloud based smart cities data secu- rity and privacy management”, In Proceedings of IEEE/ACM 7th International Conference on Utility and Cloud Computing (UCC), pages 806811. IEEE, 2014. DOI: 10.1109 .131
- W. Lum, “Cybersecurity challenges: A view from the public sector”, April 2016.
- S. Ijaz, M. A. Shah, A. Khan, M. Ahmed, “Smart cities: A survey on se- curity concerns”, International Journal of Advanced Computer Science and Applications 7(2), 612625, 2016.
- B.C.M. Fung, T. Trojer, P. C. K. Hung, L. Xiong, K. Al-Hussaeni, R. Dssouli, “Service-oriented architecture for high-dimensional private data mashup”, IEEE Transactions on Services Computing (TSC), 5(3):373386, 2012. DOI: 10.1109/TSC.2011.13
- F. Bosco, “Critical infrastructure threat landscape: Understanding and react- ing”, April 2016.
- A. Mart´inez-Balleste´, T. A. Pe´rez-Mart´inez, A. Solanas, “The pursuit of citi- zens privacy: a privacy-aware smart city is po sible”, IEEE Communications Magazine, 51(6):136141, 2013. DOI: 10.1109 25606
- Kazuki Iehira, Hiroyuki Inooue, "Detection Method and Mitigation of Server-Spoofing Attacks on SOME/IP at the Service Discovery Phase", Advances in Science, Technology and Engineering Systems Journal, vol. 11, no. 1, pp. 25–32, 2026. doi: 10.25046/aj110103
- Shaista Ashraf Farooqi, Aedah Abd Rahman, Amna Saad, "Federated Learning with Differential Privacy and Blockchain for Security and Privacy in IoMT A Theoretical Comparison and Review", Advances in Science, Technology and Engineering Systems Journal, vol. 10, no. 6, pp. 65–76, 2025. doi: 10.25046/aj100606
- Mahdi Madani, El-Bay Bourennane, Safwan El Assad, "Hardware and Secure Implementation of Enhanced ZUC Steam Cipher Based on Chaotic Dynamic S-Box", Advances in Science, Technology and Engineering Systems Journal, vol. 10, no. 1, pp. 37–47, 2025. doi: 10.25046/aj100105
- Viktor Denkovski, Irena Stojmenovska, Goce Gavrilov, Vladimir Radevski, Vladimir Trajkovik, "Exploring Current Challenges on Security and Privacy in an Operational eHealth Information System", Advances in Science, Technology and Engineering Systems Journal, vol. 9, no. 2, pp. 45–54, 2024. doi: 10.25046/aj090206
- Daisuke Hirahara, Itaru Kaneko, Junji Nishino, Junichiro Hayano, Oscar Martinez Mozos, Emi Yuda, "Investigating Heart Rate Variability Index Classification in Macaca fascicularis and Humans: Exploring Applications for Personal Identification and Anonymization Studies", Advances in Science, Technology and Engineering Systems Journal, vol. 9, no. 1, pp. 143–148, 2024. doi: 10.25046/aj090114
- Fazalur Rehman, Safwan Hashmi, "Enhancing Cloud Security: A Comprehensive Framework for Real-Time Detection, Analysis and Cyber Threat Intelligence Sharing", Advances in Science, Technology and Engineering Systems Journal, vol. 8, no. 6, pp. 107–119, 2023. doi: 10.25046/aj080612
- Hiroki Iwanaga, "Photoluminescence Properties of Eu(III) Complexes with Two Different Phosphine Oxide Structures and Their Potential uses in Micro-LEDs, Security, and Sensing Devices: A Review", Advances in Science, Technology and Engineering Systems Journal, vol. 8, no. 3, pp. 154–160, 2023. doi: 10.25046/aj080317
- Mario Cuomo, Federica Massimi, Francesco Benedetto, "Detecting CTC Attack in IoMT Communications using Deep Learning Approach", Advances in Science, Technology and Engineering Systems Journal, vol. 8, no. 2, pp. 130–138, 2023. doi: 10.25046/aj080215
- Richard Romero Izurieta, Segundo Moisés Toapanta Toapanta, Luis Jhony Caucha Morales, María Mercedes Baño Hifóng, Eriannys Zharayth Gómez Díaz, Oscar Marcelo Zambrano Vizuete, Luis Enrique Mafla Gallegos, José Antonio Orizaga Trejo, "Prototype to Identify the Capacity in Cybersecurity Management for a Public Organization", Advances in Science, Technology and Engineering Systems Journal, vol. 8, no. 1, pp. 108–115, 2023. doi: 10.25046/aj080113
- Ali Nashwan, Khalil Al-Joburi, "Integrated GIS-SUE Map Cost Estimation System Prototype for Designing a Decision Support System", Advances in Science, Technology and Engineering Systems Journal, vol. 8, no. 1, pp. 95–100, 2023. doi: 10.25046/aj080111
- Segundo Moisés Toapanta Toapanta, Rodrigo Humberto Del Pozo Durango, Luis Enrique Mafla Gallegos, Eriannys Zharayth Gómez Díaz, Yngrid Josefina Melo Quintana, Joan Noheli Miranda Jimenez, Ma. Roció Maciel Arellano, José Antonio Orizaga Trejo, "Prototype to Mitigate the Risks, Vulnerabilities and Threats of Information to Ensure Data Integrity", Advances in Science, Technology and Engineering Systems Journal, vol. 7, no. 6, pp. 139–150, 2022. doi: 10.25046/aj070614
- Tarek Nouioua, Ahmed Hafid Belbachir, "The Security of Information Systems and Image Processing Supported by the Quantum Computer: A review", Advances in Science, Technology and Engineering Systems Journal, vol. 7, no. 6, pp. 77–86, 2022. doi: 10.25046/aj070609
- Muhammad Musleh Uddin, Kazi Rafiqul Islam, Md. Monirul Kabir, "An Improved Model to Analyze the Impact of Cyber-Attacks on Power Systems", Advances in Science, Technology and Engineering Systems Journal, vol. 7, no. 5, pp. 27–34, 2022. doi: 10.25046/aj070504
- Kamil Halouzka, Ladislav Burita, Aneta Coufalikova, Pavel Kozak, Petr Františ, "A Comparison of Cyber Security Reports for 2020 of Central European Countries", Advances in Science, Technology and Engineering Systems Journal, vol. 7, no. 4, pp. 105–113, 2022. doi: 10.25046/aj070414
- Tiny du Toit, Hennie Kruger, Lynette Drevin, Nicolaas Maree, "Deep Learning Affective Computing to Elicit Sentiment Towards Information Security Policies", Advances in Science, Technology and Engineering Systems Journal, vol. 7, no. 3, pp. 152–160, 2022. doi: 10.25046/aj070317
- Afsah Sharmin, Farhat Anwar, S M A Motakabber, Aisha Hassan Abdalla Hashim, "A Secure Trust Aware ACO-Based WSN Routing Protocol for IoT", Advances in Science, Technology and Engineering Systems Journal, vol. 7, no. 3, pp. 95–105, 2022. doi: 10.25046/aj070311
- Khosro Salmani, Ken Barker, "Leakage-abuse Attacks Against Forward Private Searchable Symmetric Encryption", Advances in Science, Technology and Engineering Systems Journal, vol. 7, no. 2, pp. 156–170, 2022. doi: 10.25046/aj070216
- Kartit Zaid, Diouri Ouafaa, "Taxonomy of Security Techniques for Routing Protocols in Mobile Ad-hoc Networks", Advances in Science, Technology and Engineering Systems Journal, vol. 7, no. 2, pp. 25–31, 2022. doi: 10.25046/aj070203
- Janusz Gurzynski, Lukasz Kajda, Marcin Tarasiuk, Tomasz Samotyjak, Zbigniew Stachowicz, Slawomir Kownacki, "Control and Monitoring Systems in Medium Voltage Distribution Networks in Poland – Current Status and Directions of Development", Advances in Science, Technology and Engineering Systems Journal, vol. 6, no. 6, pp. 112–118, 2021. doi: 10.25046/aj060615
- Boris Kontsevoi, Sergei Terekhov, "TETRA™ Techniques to Assess and Manage the Software Technical Debt", Advances in Science, Technology and Engineering Systems Journal, vol. 6, no. 5, pp. 303–309, 2021. doi: 10.25046/aj060534
- Osaretin Eboya, Julia Binti Juremi, "iDRP Framework: An Intelligent Malware Exploration Framework for Big Data and Internet of Things (IoT) Ecosystem", Advances in Science, Technology and Engineering Systems Journal, vol. 6, no. 5, pp. 185–202, 2021. doi: 10.25046/aj060521
- Jianhua Yang, Lixin Wang, Yien Wang, "Enhance Student Learning Experience in Cybersecurity Education by Designing Hands-on Labs on Stepping-stone Intrusion Detection", Advances in Science, Technology and Engineering Systems Journal, vol. 6, no. 4, pp. 355–367, 2021. doi: 10.25046/aj060440
- Anh Nguyen-Duc, Manh-Viet Do, Quan Luong-Hong, Kiem Nguyen-Khac, Hoang Truong-Anh, "On the Combination of Static Analysis for Software Security Assessment – A Case Study of an Open-Source e-Government Project", Advances in Science, Technology and Engineering Systems Journal, vol. 6, no. 2, pp. 921–932, 2021. doi: 10.25046/aj0602105
- Bismark Tei Asare, Kester Quist-Aphetsi, Laurent Nana, "Node-Node Data Exchange in IoT Devices Using Twofish and DHE", Advances in Science, Technology and Engineering Systems Journal, vol. 6, no. 2, pp. 622–628, 2021. doi: 10.25046/aj060271
- Zarina Din, Dian Indrayani Jambari, Maryati Mohd Yusof, Jamaiah Yahaya, "Challenges in IoT Technology Adoption into Information System Security Management of Smart Cities: A Review", Advances in Science, Technology and Engineering Systems Journal, vol. 6, no. 2, pp. 99–112, 2021. doi: 10.25046/aj060213
- Saliha Assoul, Anass Rabii, Ounsa Roudiès, "An Operational Responsibility and Task Monitoring Method: A Data Breach Case Study", Advances in Science, Technology and Engineering Systems Journal, vol. 6, no. 1, pp. 1157–1163, 2021. doi: 10.25046/aj0601130
- Devika K N, Ramesh Bhakthavatchalu, "Modified Blockchain based Hardware Paradigm for Data Provenance in Academia", Advances in Science, Technology and Engineering Systems Journal, vol. 6, no. 1, pp. 66–77, 2021. doi: 10.25046/aj060108
- Pranay Bhardwaj, Carla Purdy, Nawar Obeidat, "A Novel Way to Design ADS-B using UML and TLA+ with Security as a Focus", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 6, pp. 1657–1665, 2020. doi: 10.25046/aj0506197
- Hesham Aly El Zouka, Mustafa Mohamed Hosni, "Time Granularity-based Privacy Protection for Cloud Metering Systems", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 6, pp. 1278–1285, 2020. doi: 10.25046/aj0506152
- Boughanja Manale, Tomader Mazri, "5G, Vehicle to Everything Communication: Opportunities, Constraints and Future Directions", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 6, pp. 1089–1095, 2020. doi: 10.25046/aj0506132
- Abdulla Obaid Al Zaabi, Chan Yeob Yeun, Ernesto Damiani, Gaemyoung, "An Enhanced Conceptual Security Model for Autonomous Vehicles", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 6, pp. 853–864, 2020. doi: 10.25046/aj0506102
- Mohammed Hadwan, Rehan Uallah Khan, Khalil Ibrahim Mohammad Abuzanouneh, "Towards a Smart Campus for Qassim University: An Investigation of Indoor Navigation System", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 6, pp. 831–837, 2020. doi: 10.25046/aj050699
- Jim Scheibmeir, Yashwant Malaiya, "Multi-Model Security and Social Media Analytics of the Digital Twin", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 6, pp. 323–330, 2020. doi: 10.25046/aj050639
- Klyagin Viktor Anatolievich, Laushin Dmitry Andreevich, "The Impact Assessment of the Errors in Determining the Mass and Zero Lift-Drag Coefficient on the Aircraft’s Performance Data", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 6, pp. 118–126, 2020. doi: 10.25046/aj050613
- Gautama Wijaya, Nico Surantha, "Multi-layered Security Design and Evaluation for Cloud-based Web Application: Case Study of Human Resource Management System", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 5, pp. 674–679, 2020. doi: 10.25046/aj050583
- Mika Karjalainen, Tero Kokkonen, "Review of Pedagogical Principles of Cyber Security Exercises", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 5, pp. 592–600, 2020. doi: 10.25046/aj050572
- Liana Khamis Qabajeh, Mohammad Moustafa Qabajeh, "Detailed Security Evaluation of ARANz, ARAN and AODV Protocols", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 5, pp. 176–192, 2020. doi: 10.25046/aj050523
- Pham Minh Nam, Phu Tran Tin, "Analysis of Security-Reliability Trade-off for Multi-hop Cognitive Relaying Protocol with TAS/SC Technique", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 5, pp. 54–62, 2020. doi: 10.25046/aj050508
- Marianna Tomašková, Darina Matisková, Michaela Balážiková, "Case Study to Determine the Causes of Fire in Agriculture", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 5, pp. 11–15, 2020. doi: 10.25046/aj050502
- Adamu Abdullahi Garba, Maheyzah Muhamad Siraj, Siti Hajar Othman, "An Explanatory Review on Cybersecurity Capability Maturity Models", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 4, pp. 762–769, 2020. doi: 10.25046/aj050490
- Maximo Giovani Tanzado Espinoza, Joseline Roxana Neira Melendrez, Luis Antonio Neira Clemente, "A Survey and an IoT Cybersecurity Recommendation for Public and Private Hospitals in Ecuador", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 3, pp. 518–528, 2020. doi: 10.25046/aj050364
- Mainar Swari Mahardika, Achmad Nizar Hidayanto, Putu Agya Paramartha, Louis Dwysevrey Ompusunggu, Rahmatul Mahdalina, Farid Affan, "Measurement of Employee Awareness Levels for Information Security at the Center of Analysis and Information Services Judicial Commission Republic of Indonesia", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 3, pp. 501–509, 2020. doi: 10.25046/aj050362
- Suchitra Abel, Yenchih Tang, Jake Singh, Ethan Paek, "Applications of Causal Modeling in Cybersecurity: An Exploratory Approach", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 3, pp. 380–387, 2020. doi: 10.25046/aj050349
- Gillala Rekha, Shaveta Malik, Amit Kumar Tyagi, Meghna Manoj Nair, "Intrusion Detection in Cyber Security: Role of Machine Learning and Data Mining in Cyber Security", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 3, pp. 72–81, 2020. doi: 10.25046/aj050310
- Segundo Moisés Toapanta Toapanta, Daniela Monserrate Moreira Gamboa, Luis Enrique Mafla Gallegos, "Analysis of the Blockchain for Adoption in Electronic Commerce Management in Ecuador", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 2, pp. 762–768, 2020. doi: 10.25046/aj050295
- Segundo Moisés Toapanta Toapanta, Andrés Aurelio García Henriquez, Luis Enrique Mafla Gallegos, "Analysis of Vulnerabilities, Risks and Threats in the Process of Quota Allocation for the State University of Ecuador", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 2, pp. 673–682, 2020. doi: 10.25046/aj050283
- Lylia Alouache, Mohamed Maachaoui, Rachid Chelouah, "Securing Hybrid SDN-based Geographic Routing Protocol using a Distributed Trust Model", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 2, pp. 567–577, 2020. doi: 10.25046/aj050271
- Segundo Moisés Toapanta Toapanta, José David López Cobeña, Luis Enrique Mafla Gallegos, "Analysis of Cyberattacks in Public Organizations in Latin America", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 2, pp. 116–125, 2020. doi: 10.25046/aj050215
- Karim El bouchti, Soumia Ziti, Fouzia Omary, Nassim Kharmoum, "New Solution Implementation to Protect Encryption Keys Inside the Database Management System", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 2, pp. 87–94, 2020. doi: 10.25046/aj050211
- José Alomía-Lucero, Jorge Castro-Bedriñana, Doris Chirinos-Peinado, "Rooftop Urban Agriculture Model with Two Tomato Varieties (Lycopersicum esculentum Mill) and Toppings in the High Jungle – Peru", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 1, pp. 446–450, 2020. doi: 10.25046/aj050157
- Amit Kumar Tyagi, A. Mohan Krishna, Shaveta Malik, Meghna Manoj Nair, Sreenath Niladhuri, "Trust and Reputation Mechanisms in Vehicular Ad-Hoc Networks: A Systematic Review", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 1, pp. 387–402, 2020. doi: 10.25046/aj050150
- Falmata Modu, Adam Adam, Farouq Aliyu, Audu Mabu, Mahdi Musa, "A Survey of Smart Hydroponic Systems", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 1, pp. 233–248, 2020. doi: 10.25046/aj050130
- Saleh Albahli, Rehan Ullah Khan, Ali Mustafa Qamar, "A Blockchain-Based Architecture for Smart Healthcare System: A Case Study of Saudi Arabia", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 1, pp. 40–47, 2020. doi: 10.25046/aj050106
- Amine Kardi, Rachid Zagrouba, "Attacks classification and security mechanisms in Wireless Sensor Networks", Advances in Science, Technology and Engineering Systems Journal, vol. 4, no. 6, pp. 229–243, 2019. doi: 10.25046/aj040630
- Evan Hurwitz, Chigozie Orji, "Multi Biometric Thermal Face Recognition Using FWT and LDA Feature Extraction Methods with RBM DBN and FFNN Classifier Algorithms", Advances in Science, Technology and Engineering Systems Journal, vol. 4, no. 6, pp. 67–90, 2019. doi: 10.25046/aj040609
- Allae Erraissi, Abdessamad Belangour, "A Big Data Security Layer Meta-Model Proposition", Advances in Science, Technology and Engineering Systems Journal, vol. 4, no. 5, pp. 409–418, 2019. doi: 10.25046/aj040553
- Segundo Moisés Toapanta Toapanta, Steven Xavier Romo Sañicela, Danny Wilfrido Barona Valencia, Luis Enrique Mafla Gallegos, "Analysis of Information Security for a Voting Process for Sectional Governments in Ecuador", Advances in Science, Technology and Engineering Systems Journal, vol. 4, no. 5, pp. 352–359, 2019. doi: 10.25046/aj040546
- Alghamdi Abdullah, Mohammed Thanoon, Anwar Alsulami, "Toward a Smart Campus Using IoT: Framework for Safety and Security System on a University Campus", Advances in Science, Technology and Engineering Systems Journal, vol. 4, no. 5, pp. 97–103, 2019. doi: 10.25046/aj040512
- Segundo Moisés Toapanta Toapanta, Allan Fabricio German Diaz, Darío Fernando Huilcapi Subia, Luis Enrique Mafla Gallegos, "Proposal for a Security Model for a Popular Voting System Process in Latin America", Advances in Science, Technology and Engineering Systems Journal, vol. 4, no. 5, pp. 53–60, 2019. doi: 10.25046/aj040507
- Segundo Moisés Toapanta Toapanta, Gabriel Enrique Valenzuela Ramos, Félix Gustavo Mendoza Quimi, Luis Enrique Mafla Gallegos, "Prototype of a Security Architecture for a System of Electronic Voting for the Ecuador", Advances in Science, Technology and Engineering Systems Journal, vol. 4, no. 4, pp. 292–299, 2019. doi: 10.25046/aj040437
- Segundo Moisés Toapanta Toapanta, Andrés Javier Bravo Jácome, Maximo Giovanny Tandazo Espinoza, Luis Enrique Mafla Gallegos, "An Immutable Algorithm Approach to Improve the Information Security of a Process for a Public Organization of Ecuador", Advances in Science, Technology and Engineering Systems Journal, vol. 4, no. 3, pp. 25–30, 2019. doi: 10.25046/aj040304
- Robert M. Beswick, "Computer Security as an Engineering Practice: A System Engineering Discussion", Advances in Science, Technology and Engineering Systems Journal, vol. 4, no. 2, pp. 357–369, 2019. doi: 10.25046/aj040245
- Shruthi Narayanaswamy, Anitha Vijaya Kumar, "Application Layer Security Authentication Protocols for the Internet of Things: A Survey", Advances in Science, Technology and Engineering Systems Journal, vol. 4, no. 1, pp. 317–328, 2019. doi: 10.25046/aj040131
- Lin Dong, Akira Rinoshika, "Analysis and Methods on The Framework and Security Issues for Connected Vehicle Cloud", Advances in Science, Technology and Engineering Systems Journal, vol. 3, no. 6, pp. 105–110, 2018. doi: 10.25046/aj030611
- Ola Surakhi, Mohammad Khanafseh, Yasser Jaffal, "An enhanced Biometric-based Face Recognition System using Genetic and CRO Algorithms", Advances in Science, Technology and Engineering Systems Journal, vol. 3, no. 3, pp. 116–124, 2018. doi: 10.25046/aj030316
- Abul Kalam Azad, Md. Yamin Mollah, "EAES: Extended Advanced Encryption Standard with Extended Security", Advances in Science, Technology and Engineering Systems Journal, vol. 3, no. 3, pp. 51–56, 2018. doi: 10.25046/aj030307
- Dhiman Chowdhury, Mrinmoy Sarkar, Mohammad Zakaria Haider, "A Cyber-Vigilance System for Anti-Terrorist Drives Based on an Unmanned Aerial Vehicular Networking Signal Jammer for Specific Territorial Security", Advances in Science, Technology and Engineering Systems Journal, vol. 3, no. 3, pp. 43–50, 2018. doi: 10.25046/aj030306
- Nicola Fabiano, "The Internet of Things ecosystem: the blockchain and data protection issues", Advances in Science, Technology and Engineering Systems Journal, vol. 3, no. 2, pp. 1–7, 2018. doi: 10.25046/aj030201
- Asma Meddeb, Hajer Jmii, Souad Chebbi, "Security Analysis and the Contribution of UPFC for Improving Voltage Stability", Advances in Science, Technology and Engineering Systems Journal, vol. 3, no. 1, pp. 404–411, 2018. doi: 10.25046/aj030149
- Luca Dariz, Gianpiero Costantino, Massimiliano Ruggeri, Fabio Martinelli, "A Joint Safety and Security Analysis of message protection for CAN bus protocol", Advances in Science, Technology and Engineering Systems Journal, vol. 3, no. 1, pp. 384–393, 2018. doi: 10.25046/aj030147
- Anass Sedrati, Abdellatif Mezrioui, "A Survey of Security Challenges in Internet of Things", Advances in Science, Technology and Engineering Systems Journal, vol. 3, no. 1, pp. 274–280, 2018. doi: 10.25046/aj030133
- Hiroaki Anada, Seiko Arita, "Short CCA-Secure Attribute-Based Encryption", Advances in Science, Technology and Engineering Systems Journal, vol. 3, no. 1, pp. 261–273, 2018. doi: 10.25046/aj030132
- Zeineb Zhioua, Rabea Ameur-Boulifa, Yves Roudier, "Framework for the Formal Specification and Verification of Security Guidelines", Advances in Science, Technology and Engineering Systems Journal, vol. 3, no. 1, pp. 38–48, 2018. doi: 10.25046/aj030106
- Himanshu Upadhyay, Hardik Gohel, Alexander Pons, Leo Lagos, "Virtual Memory Introspection Framework for Cyber Threat Detection in Virtual Environment", Advances in Science, Technology and Engineering Systems Journal, vol. 3, no. 1, pp. 25–29, 2018. doi: 10.25046/aj030104
- Susan Gottschlich, "A Taxonomy for Enhancing Usability, Flexibility, and Security of User Authentication", Advances in Science, Technology and Engineering Systems Journal, vol. 2, no. 6, pp. 225–235, 2017. doi: 10.25046/aj020627
- Mohamed El Beqqal, Mostafa Azizi, "Review on security issues in RFID systems", Advances in Science, Technology and Engineering Systems Journal, vol. 2, no. 6, pp. 194–202, 2017. doi: 10.25046/aj020624
- Mbunwe Muncho Josephine, "Design and Construction of a remote control switching device for household appliances application", Advances in Science, Technology and Engineering Systems Journal, vol. 2, no. 4, pp. 154–164, 2017. doi: 10.25046/aj020421
- Saleh Mohamed Alnaeli, Melissa Sarnowski, Md Sayedul Aman, Ahmed Abdelgawad, Kumar Yelamarthi, "Source Code Vulnerabilities in IoT Software Systems", Advances in Science, Technology and Engineering Systems Journal, vol. 2, no. 3, pp. 1502–1507, 2017. doi: 10.25046/aj0203188
- Ali Shuja Siddiqui, Yutian Gui, Jim Plusquellic, Fareena Saqib, "A Secure Communication Framework for ECUs", Advances in Science, Technology and Engineering Systems Journal, vol. 2, no. 3, pp. 1307–1313, 2017. doi: 10.25046/aj0203165
- Daniel Fraunholz, Marc Zimmermann, Hans Dieter Schotten, "Towards Deployment Strategies for Deception Systems", Advances in Science, Technology and Engineering Systems Journal, vol. 2, no. 3, pp. 1272–1279, 2017. doi: 10.25046/aj0203161
- Davar Pishva, "IoT: Their Conveniences, Security Challenges and Possible Solutions", Advances in Science, Technology and Engineering Systems Journal, vol. 2, no. 3, pp. 1211–1217, 2017. doi: 10.25046/aj0203153
- Stefania Nanni, Elisa Benetti, Gianluca Mazzini, "Indoor monitoring in Public Buildings: workplace wellbeing and energy consumptions. An example of IoT for smart cities application", Advances in Science, Technology and Engineering Systems Journal, vol. 2, no. 3, pp. 884–890, 2017. doi: 10.25046/aj0203110
- Sarra Alqahtani, Rose Gamble, "Verifying the Detection Results of Impersonation Attacks in Service Clouds", Advances in Science, Technology and Engineering Systems Journal, vol. 2, no. 3, pp. 449–459, 2017. doi: 10.25046/aj020358
- Shaddrack Yaw Nusenu, "Directional Antenna Modulation Technique using A Two-Element Frequency Diverse Array", Advances in Science, Technology and Engineering Systems Journal, vol. 2, no. 3, pp. 227–232, 2017. doi: 10.25046/aj020331
- Raid Khalid Hussein, Ahmed Alenezi, Hany F. Atlam, Mohammed Q Mohammed, Robert J. Walters, Gary B. Wills, "Toward Confirming a Framework for Securing the Virtual Machine Image in Cloud Computing", Advances in Science, Technology and Engineering Systems Journal, vol. 2, no. 4, pp. 44–50, 2017. doi: 10.25046/aj020406
- Fatna Elmendili, Nisrine Maqran, Younes El Bouzekri El Idrissi, Habiba Chaoui, "A security approach based on honeypots: Protecting Online Social network from malicious profiles", Advances in Science, Technology and Engineering Systems Journal, vol. 2, no. 3, pp. 198–204, 2017. doi: 10.25046/aj020326
- Fabian Bustamante, Walter Fuertes, Paul Diaz, Theofilos Toulqueridis, "Methodology for Management of Information Security in Industrial Control Systems: A Proof of Concept aligned with Enterprise Objectives.", Advances in Science, Technology and Engineering Systems Journal, vol. 2, no. 3, pp. 88–99, 2017. doi: 10.25046/aj020313
- Selina Kolokytha, Alexander Flisch, Thomas Lüthi, Mathieu Plamondon, Adrian Schwaninger, Wicher Vasser, Diana Hardmeier, Marius Costin, Caroline Vienne, Frank Sukowski, Ulf Hassler, Irène Dorion, Najib Gadi, Serge Maitrejean, Abraham Marciano, Andrea Canonica, Eric Rochat, Ger Koomen, Micha Slegt, "Improving customs’ border control by creating a reference database of cargo inspection X-ray images", Advances in Science, Technology and Engineering Systems Journal, vol. 2, no. 3, pp. 60–66, 2017. doi: 10.25046/aj020309
- Casimer DeCusatis, Piradon Liengtiraphan, Anthony Sager, "Zero Trust Cloud Networks using Transport Access Control and High Availability Optical Bypass Switching", Advances in Science, Technology and Engineering Systems Journal, vol. 2, no. 3, pp. 30–35, 2017. doi: 10.25046/aj020305
- Chien Hua Wu, Ruey Kei Chiu, "Implementation a Secure Electronic Medical Records Exchange System Based on S/MIME", Advances in Science, Technology and Engineering Systems Journal, vol. 2, no. 1, pp. 172–176, 2017. doi: 10.25046/aj020120
- Samantha Mathara Arachchi, Siong Choy Chong, Alik Kathabi, "System Testing Evaluation for Enterprise Resource Planning to Reduce Failure Rate", Advances in Science, Technology and Engineering Systems Journal, vol. 2, no. 1, pp. 6–15, 2016. doi: 10.25046/aj020102
- Majid Mumtaz, Sead Muftic, Nazri bin Abdullah, "Strong Authentication Protocol based on Java Crypto Chip as a Secure Element", Advances in Science, Technology and Engineering Systems Journal, vol. 1, no. 5, pp. 21–26, 2016. doi: 10.25046/aj010505
