Time Granularity-based Privacy Protection for Cloud Metering Systems
Volume 5, Issue 6, Page No 1278–1285, 2020
Adv. Sci. Technol. Eng. Syst. J. 5(6), 1278–1285 (2020);
 DOI: 10.25046/aj0506152
DOI: 10.25046/aj0506152
Keywords: Smart Meter, Zero Knowledge Proof, Authentication, Security, Privacy, Cloud
Due to the advent of cloud computing and Internet of Things, smart meters have become a crucial part of smart cities. Smart meters generate vast amounts of fine-grained data that can immediately provide useful information to electricity consumers, such as automatic billing, load monitoring, and dynamic time pricing. This will make the electricity consumers more energy-efficient and self-organized in IoT and cloud computing technology. Smart meters also enable two-direction flow of energy and balance the measurement of inflows and outflows of energy between the meter and electric utility’s central system through remote reporting. Besides, they help designers integrate renewable energy generation, such as solar rooftops to cover remaining energy needs. However, smart meters entail some severe security challenges. From a security point of view, these meter readings have a potential threat on personal privacy and the collected meter data. They may also reveal some details about consumer’s lives. Thus, the data acquisition from those meter readings is expected to incorporate privacy requirements and application demands. In addition, the collected raw data from various meter readings needs to be collected from IoT smart metering sensors and stored in the cloud to be accessed and analyzed by electricity consumers. Subsequently, this considerable information Is prone to privacy threats and security vulnerabilities as the transmission of data to the cloud is most likely to cause a data breaching. In this paper the privacy and confidentiality of meter readings is protected through trusted platform module, which will allow the electricity provider to get the energy consumption at a periodic time granularity.
1. Introduction
The future smart meters are expected to provide details on individual appliance consumption and enable customers to access electricity safely and economically [1]. These technologies lead the trend to shift from conventional power grid to smart grid that uses sensors, smart meters, advanced communication systems and information technologies to create monitoring and visualizing real-time electricity information. But these technologies pose threats to individual’s privacy as they can simply reveal one’s daily activities [2]. Fine-grained electricity consumption aggregation scheme for smart meters can be used to reveal some information about consumers’ lives and their activities. It can be also used to detect the presence or absence of occupants [3], [4]. In addition, transmitting the smart meter data to private or public cloud storage will allow the household consumers to monitor their usage, change their energy habits, adjust their electric power consumption, and give them better management to their energy costs. Real-time monitoring, then, can be accessed via the cloud using mobile browser, or any PC/Mac browser in the world. Subsequently, these meter readings and information are prone to privacy and security threats as the transmission of data to the cloud is most likely to cause a data breaching. In this paper, a storage outsourcing in the cloud is considered secure where the external storage is often untrusted or only semi-trusted. In addition, privacy-preserving analytics for IoT and cloud-based smart metering system is ensured by using a trusted hardware module which is used in conjunction with generated random number generator. The proposed framework guarantees an improved secure data storage of IoT smart meter reading and provides real-time measures of electricity consumption and the estimations of the consumption during operations.
In this system, the consumer grants the service company a meter reading request service at a time of charging and the granted utility company is only allowed to get the power readings during that granted time. This system also provides practical security measures and protects the privacy of consumers who have smart meters at their homes. Also, a privacy model is provided here to achieve the privacy requirement and experience that the proposed system may have a significant effect on privacy-preserving systems if the system is built under the assumption that the utility provider is semi-honest.
In addition, strong access configuration and authentication management protocols should be constructed in IoT -cloud outsourcing process, and any unauthorized access should be utilized and reported. Moreover, due to the lack of privacy and security issues, sensitive personal data can be revealed to third parties such as utility companies and cloud service providers. Today, energy might be collected and stored for future use as per demand. Additionally, data analysis programs can be used to improve the efficiency of power consumption of a particular meter.
It is true, of course, that adding memory or a processor to the smart meter will enhance its security services capabilities, but contradictorily, the cost of implementing these smart meters will be increased dramatically. The proposed security system in this paper is designed to support multiple time segment granularities and let the meter readings to be stored securely on the cloud. It also comprises the design, construction, and operation of proposed two-way communication scheme, which ensures secure and reliable connections between the smart meters and getaways.
The rest of this paper is structured as follows. Section II discusses the architecture and characteristics of smart metering system with the cloud computing. The related work is given in Section III. The system design and modeling are presented in Section IV. Results in terms of system implementation, authentication, security and privacy are presented and discussed in Section. V. The performance analysis of the proposed system is discussed in Section VI. In the final section, the conclusion and future work are presented.
2. Cloud Metering Infrastructure
Smart technologies like the IoT, artificial intelligence (AI), and other digital technologies are providing new opportunities to smart grid network, and can be used to control, monitor, maintain production, transmission, and consumption of electricity in smart metering systems. Many benefits could be obtained through the deployment of the smart grid services in cloud computing, in order to achieve energy savings. Cloud computing is also used to speed up communication with telemetry devices [5]. Moreover, power grid technology can be combined with smart meters to reduce the energy consumption in the peak demand and, hence, improve cost savings.
However, fine-grained technical approaches can cause security and privacy concerns for smart meter users. Current smart/interval meters can record electricity consumption in 30-minute intervals; however, the new generation of smart meters use more advanced technology and could convert all time units to seconds. Mechanisms for large-scale distributed sensor networks and other complex issues are likely to be addressed in order to prevent personal privacy from being breached and prevent revealing detailed information of one’s daily activities. It should be made clear that smart meters record the energy usage exactly in the same way as the standard meters, and send this data to the consumers and the utility provider, on a required time interval, which allows consumers to monitor their power consumption at very fine time granularities. As opposed to the conventional method of electricity billing [6], the proposed approach does not require a person from the electric companies to read the number of units of energy consumed in the meter. The proposed system can play an important role in minimizing overall energy consumption and, hence, making significant contribution to energy efficiency and power saving.
One of the most important aspects of the proposed privacy-preserving energy scheme is its capability of providing a fine-grained smart meter access, while preserving the privacy of consumers based on an encryption scheme.
Therefore, the proposed fine-grained anonymous metering system will encourage consumers to use limited electricity during peak hours, especially when energy demand is high and inform them with their consumption patterns, and challenge them to fully utilize potential while saving costs. Finally, a Load Monitoring Center (LMC) will be introduced in attempt to access the sum of meter readings from various smart meter-time resolutions (e.g. half-minute, one minute, five minute, etc.).
Some previous studies have focused on privacy, security, and accuracy issues of plug load monitoring system in smart grid environment [6]. Other related studies have focused on payment predication and automatic bill generation. Various privacy-preserving models were proposed to protect the individual’s privacy and minimize the energy consumption [7]. However, most of the corrupted meters will disclose the activities of users by measuring their usage frequency. Furthermore, cyber security can be utilized to characterize the surrounding magnetic field of smart meter, which in turn will expose some vulnerabilities with the data being transmitted from smart meters. To solve such problems, many researchers have developed and investigated a wide variety of approaches over the years in order to prevent disclosing the consumer living activities and invade their privacy. In this paper, cloud computing offers an alternative storage model to the traditional in-house smart meter model. This is a quite effective way, so that the data stored in the cloud will be secured by using multiple levels of encryption and, hence, only authenticated consumers would be getting access to it. All meter readings will be read at specified time intervals and readings will be stored in a secure cloud-based server which will be accessible from anywhere through a web browser or any mobile device. The meter reading privacy will, then, be protected within the cloud environment, and, as a result, only authorized household consumers will get permission to access the sensitive content in the cloud.
The Cloud metering system (CMS) proposed here consists of three main parts: trusted identity module, cloud storage unit, and the utility service provider. The trusted identity module is embedded on a smart meter for the purpose of securing the metering services. The external cloud storage allows consumers to do their reading remotely, with no need to buy expensive equipment or hire large IT staffs. The energy service provider pools consumers’ services, and demand different time granularities [9]. The proposed model has a mechanism to manage and grant meter readings to the utility company at specific time and date.
The utility company, then, can get energy readings at specific time intervals by analyzing meter data stored in the cloud. Meter readings are securely sent over the mobile network to be stored in the cloud for monitoring and analysis purposes. The meter construction and two-way communications capability will enable the system to process remote connections and disconnections of power service [10], [11]. The smart meters have the ability to measure, store, and report both energy inflows and outflows [12], [13]. The utility provider then, aggregates the consumption data from the storage system on the granted date in order to balance between the privacy requirements and the functionality of the system. Also, a privacy model is considered, as the meter readings should not be exposed to unauthorized persons or processes during transmission, storage and retrieving [14], [15]. Figure 1 illustrates the construction of the proposed CMS model.
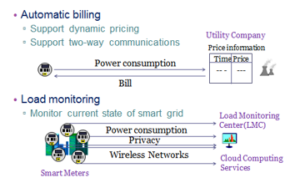
Figure 1: CMS Architecture
Clearly, the privacy is preserved by hiding smart meter’s individual readings. Thus, sensitive data should be inaccessible to eavesdroppers. For example, data utilization, visualization, detection of emerging failures, centralized and decentralized operations and controls, all need to be considered when designing a secure network. There are complex security requirements to be deployed either on the cloud or on the smart meter with potentially limited resources like authentication and ID management. Thus, strong authentication protocols should be implemented in the cloud network to provide protection against privacy violations. Meanwhile, unauthorized users are rejected through the use of access control or privacy features. Without cloud, smart meters cannot preserve consumer privacy and confidentiality. On the other hand, sensitive data or meter readings should be encrypted before being outsourced to the cloud. [16], [17].
3. Related Work
Different secure architectures and data aggregations have been proposed to reduce the cost of digital signatures in smart meters. All these schemes aim to protect the transferred readings of energy data. There are different types of smart metering architectures, some are of a meter and others are of many meters. The former contribute to the billing applications and the later contribute to applications such as load monitoring.
Aggregation and the role of Trusted Third Parties (TTP} has been discussed in [18]. The role of a trusted third party is to validate and safeguard protected meter readings on the basis of privacy policies of third party services. Others have used cryptographic primitives. [19]-[21], for example, smart meters can greatly benefit from accessing cloud processing and storage services if security measures, like homomorphic encryption, are applied. This can be achieved by encrypting smart meter data before storage takes place in the cloud.
This model is quite unique when it comes to the aggregation of meters’ readings using zero knowledge protocol and tamper proof signature.
As for [22] and [23], they replaced tamper proof signature by TPM. Mc Laughlinet al [24] propose an approach to privacy-preserving data aggregation being transmitted using a random noise. This random noise must be chosen in a manner that is transparent and does not affect the validity of aggregated data from smart meters. They also presented a privacy-preserving technique that is based on inserting the result of three aggregation functions for any given neighborhood in a short time period ψt. Based on these functions, the aggregation technique is implemented in such a way that the aggregator can produce an accurate aggregate number while maintaining the confidentiality of individual meter reading.
Moreover, [25] have proposed an approach that can utilize privacy settings on smart meters by using secret sharing scheme combined with symmetric encryption. The paper [26] has proposed a hybrid approach that uses random noise and pseudorandom sequences to preserve the privacy of readings collected from smart meters. Their proposed system supports load monitoring and billing applications as they claimed in their paper. However, most of the privacy preserving approaches in smart metering systems concentrate on the sensitivity of meter readings in attempt to protect time-series in general and not designed for very fine time granularities. Also, it is not clear which reading is considered sensitive and how it should be handled. While privacy-preserving solutions have been studied, users’ privacy concerns have been not fully defined and the privacy of smart meter readings has not been formally addressed. Currently, many gaps exist between linking the meter readings to the status of specific applications. Appropriate regulatory protections vary from one application to other.
In this paper, the privacy of smart meter users is preserved by providing a flexible platform that supports multiple time granularities. In addition, the provided storage services of these smart metering systems are highly dependent on the cloud infrastructure. To ensure authenticity and integrity, a trusted platform module will be employed in this paper. The suggested module will be used to create signatures over the data to be signed.
4. System Design and Modeling
In this section, time scale notation, metering system and the proposed security model are described along with a brief introduction to the proposed privacy requirement.
4.1. Time Scale Notations
At the lowest level of time granularity S1, time is divided into several time units T1, T2, ….,Tn of 1 ms. Each time interval unit Ti is allocated to weight wi. At the startup routine, all the weights are equal, and the system entity structures extension to integrate weight hierarchies and time granularities into real time workflow. Automatically, a time granularity S is defined to support different applications. An example of three different time granularities, S1 , S2 and S3is shown in Figure2.
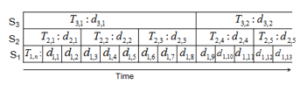
Figure 2: Time Granularities System
4.2. Smart Metering Process
The proposed metering system consists of a meter, an external cloud storage platform and the cloud service provider SPi which has a key pair: a public key (PK1) and a private key (SK1).
Figure3 shows an example of the proposed platform with a cloud computing architecture. Supposedly, a meter is fully trusted and the storage platform as well as the cloud service provider are honest, as they follow specific procedures in extracting individual meter readings from storage devices and communication links. If a consumer has a meter SM that records energy consumption d1 at time unit T1, H agrees time granularities Si with different service providers SPi, and constructs SM by storing S1.
Meter M, then, encrypts the meter reading d1 as C1 and stores C1 into the cloud storage system. By getting the access right at a given time granularity Si, an energy consumption di at time interval Ti is a sum of meter readings:

The proposed model consists of 3 layers, hardware layer, application layer and Kernel layer. The hardware layer consists of all hardware modules including the precision measurement unit, the platform module and a communication and processing module. As for the kernel layer, it has a set of modules that interacts with hardware layer. Then comes the application layer that is constructed upon the kernel layer to offer facilities such as cloud network management service, transaction service and web edge for monitoring current meter readings which can be stored on the cloud. This allows easy access to such readings from anywhere through any web-based interface application.
5. Trust Assumptions and Security Requirements
The meter readings can be transferred directly to the cloud using a Trusted Third Party (TTP) encryption, which is responsible for the registration of consumers and servers. TTP can manage meter data using standard Internet connections and has the capability to provide data confidentiality, data integrity and fraud prevention. Due to these capabilities, the consumers can utilize the best authentication and registration features. Hence, home residents can easily monitor and control home electricity facilities through computer and smart phones over the TTP. The whole registration, authentication method is illustrated in Figure 3.
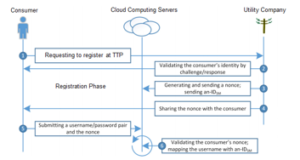
Figure 3: Consumer Authentication Process
The residential home has local renewable resources, energy storage and electrical appliances that are able to adjust power consumption behavior and predict demand-capacity. It then works with a set of service providers as each service provider primarily delivers access of meter readings at a time periodically. In addition, each network/service provider SPi with a key pair (private and public) has a demanded time granularity Si, and the startup time at the initial time granularity Ti,j can be approximated by the following equation :

Therefore, a network provider can compute the energy consumption di at time Ti by editing the encrypted meter readings as long as it knows a random value ri of sometime unit Ti . Then, the energy consumption di can be easily calculated by the following equation:

The consumer appliances, local renewable energy generators, smart grid utility will all be connected by the cloud and controlled by smart home meter which has the skill of getting consumption information from cloud services.
This smart-home meter is also capable of static scheduling and runtime scheduling to reduce the total cost of electricity energy while sustaining power requirements [27].
From security point of view, the consumer appliances should give the corresponding random numbers rito SPi in order to permit the right access of meter reading at a specific time Si to a network provider SPi. In order to reduce the communication cost of random number ri derives the next one ri,j+1 by using a shared PRNG where a random number is generated so that the equation would be:
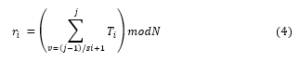
Where the time granularity Si is derived from r1 using the pseudorandom number generator g1. The consumer, then, will securely give ri, Si to the service provider SPi in order to grant the right access. SPi can consequently, derive other random numbers.
5.1. Trust Model
Let h be a crypto system and has h function where the encryption and decryption procedures used by the network provider SPi to authenticate the communication parties and to create a secure connection. The consumer will, then, share random number generator g: with SPi, correspondingly. Then, the consumer will configure a meter SM by setting initial state number of a specific time Si.
The TPM and SM will generate a master key K by the using a seed θ, the sequence number SN and the hash algorithm h. The session key k is securely saved in the TPM of SM which creates a seed key Ki by using the session key K and description Di. M, then, computes ri , and encrypts it by using public key PKi as ri and stores ni to the external data storage system.
5.2. Usability Goal
Permanent data storage mechanisms are urgently needed for the development of smart-meter system which aims at reducing the electricity cost at a residential home by scheduling the power demands according to a rich set of power – related data that can describe the dynamic status of smart grid, local power generation, energy consumption of consumer appliances, sensor data, weather data and occupants’ activity data.
All this data will be stored in the cloud by a data base that is implemented by MYSQL which will also support queries over data and metadata from the smart home systems.
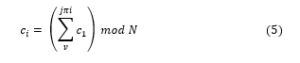
where = ( )
Meaning that the service provider SPi gets the encrypted power assumption di of every time unit Ti , for j ≥ 1 since di< N. In the next part, the privacy requirement that is proposed here is defined and it is proven that the proposed system meets it. Moreover, it is shown that managing meter data collections and billing are secure.
5.3. Privacy-Preserving Requirement
Privacy here requires that a network provider SPi cannot get energy consumption di at specific time intervals Sv, where j ≥ 1 and v < I. Paying into consideration that if SPi cannot get energy consumption at specific time intervals Si -1, it wouldn’t get energy consumption at any time intervals Sv for v < i – 1. The privacy preserving requirement here is to keep the time granularity adapted to a prior time constraints when determining the maximum time boundary. For example, a demand phase continues first when A adoptively gets meter readings di at time intervals T1, j as j = 1 and C returns back to A the encrypted meter readings C1. A, then, specifies to enter the experiment phase at (j* – 1) + 1. A then chooses two challenge sets meter readings for a time {0 , 1}. The intersection of the two sets is that the consequential di , j* are the same as illustrated in the following equation:
After reading the encrypted meter data, A passes to the second phase. For a second time, A adaptively indicates a meter reading dj for subjective time interval Ti and C automatically returns the encrypted meter reading C1 back to A. Hence, a smart metering scheme satisfies the privacy preserving requirement against a network provider SPi for any probabilistic polynomial time function T bounded adversary A attacking the real process.
Table 1: Implementation analysis of the proposed system
| Initialization phase | Computation cost (ms) | Storage cost |
| Registration phases | < 10 ms | 1592 B |
| Generating a nonce number | 1.2 ms | 2 B |
| Encrypting a meter reading | < 12 ms | 19 |
| Session key exchange | 4.3 ms | 17 B |
| Data transmission phase | 2.8 ms | 68 B |
5.4. Storage System Security
The meter readings are shown to be securely stored in the cloud storage devices, bearing in mind that each network provider has more information than the storage devices and that the proposed metering algorithm is securely integrated with privacy-preserving scheme.
The security requirement of cloud storage is the collective processes, technologies and controls that ensure that only authorized and legitimate users can store, access and use storage resources. The attacker A has the same role of the storage system, but without the knowledge of the stored pseudorandom number r. Hence, the metering systems satisfy the secure storage constraints by considering any probabilistic parameterized polynomial time algorithms which are employed by the users during the initialization and the security phases, assuming that all encryption algorithms used by network provider SPi are completely secure.
6. Performance Analysis and Results
The performance of the offered smart metering system is examined in terms of benefit-to-cost ratio and storage cost. Moreover, a specific scenario is considered where four time measures; years, months, hours, and seconds are used in the smart meter. The utilization of the system shows that the time of the generated key is the highest among the transmitted and authentication time.
In addition, the proposed system minimizes the overhead of the authentication process as compared to the other know authentication algorithms in smart metering networks because the key used in transfer time as well as the key used in the verification time produce a lower amount of overhead. As shown in Table 1, it is obvious that the encryption time is the highest among the authentication and transfer time.
It is also obvious, from the table, that the time complexity for key generation is in the order of O(log n) and it takes nearly less than 20 seconds on average to be accomplished. Despite the long generation time and relatively low encryption time, the total key transfer time range is 0.6 to 3 seconds, whereas the total key authentication time range is 0.8 to 5 seconds.
Noticing that the scheduling scheme produces a total of N sub-keys of the size of 32 bits and that the encryption system used by network providers is standard RSA encryption. The proposed system showed that the generated 2048-bit key of RSA algorithm takes significantly longer than the 1042-bit key. A commercial Information on Trusted Platform Module (TPM) chip is used to enhance the performance of cryptographic system in terms of space and speed, which is capable of supporting a 1024-bit signature in 50 ms and 2048-bit RSA signature in 250 ms.
The TPM can be initiated to cope with multiple security services, including the protection and secure storage of the keys. TMP can be used also to cope with RSA algorithm for key signing and encrypting data.
It is also assumed that calculating Si optimal additions is not slower than the estimated time complexity to factor 1024-bit RSA modulus, and the fastest known factorization algorithm requires around 265 times complexity to factor a 1024-bit signature. The task of generating a 1024-bit RSA signature, would take less than 100 ms to be generated.
Thus, the complexity of encrypting a meter reading takes less than 35 ms. Additionally, the storage cost of a meter is considered to be constant and the cost of storing data in the cloud system is analyzed as follows: for each reading, the cloud system stores an encrypted data reading of (log2 n) bits. In order to grant the access right to a network provider SPi, a cipher text is stored in the cloud storage system at the first time interval T1.
Consequently, for every Ti time unit at time granularity S1, an encryption of a nonce digits is stored. In the proposed model, the cloud storage efficiency of encrypted data reading of a month is around 325 MB, and as for the storage cost of encrypted data for a month is about 3.4 MB, which make the overall storage cost of the cloud storage system for a meter system per month is fewer than 126.3 MB.
Level of trust operations of cloud network providers includes encryption, modular arithmetic and the computation of nonce numbers are all within efficient range and work under all standard reference conditions required by secure service providers. The computation efficiency of meter system is analyzed as follows: large keys are converted into small keys by using MD5 hash algorithm and the data encryption takes place during the initialization process.
The calculation in the initialization process is subject to the computation of generated RSA keys. As the encrypting of a nonce takes 2 ms, the initialization itself takes 2 seconds. At T1, the meter reading is encrypted by using the nonce r1 that on average, takes between 10 – 15 ms to be completed.
On the other hand, the efficiency analysis and the security analysis show that the proposed protocol is secure and efficient ; the efficiency is verified by ns2 simulation results, which show a high authentication rate. The average time for the authentication phase is between 1 and 2 ms, and the average time of key exchange protocol is also utilized and was in the range of 1 to 7 ms.

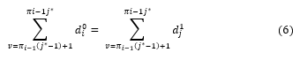
Figure 4: End-to-End Delay
The verification time has been calculated for various security measures in accordance with the key generation time and the key computation time to prevent intruders from decrypting the keys. The simulation results showed that the elapsed time to complete the verification process including the key exchange protocol and the hash function is approximately equal to the total time required for exchanging of all smart meter readings within the communication channel.
The performance analysis of this system for varying number of meters is presented in Figure 4 and Figure 5, respectively. In the former figure, the measured end-to-end delay between the creation and aggregation of the meter readings at the cloud server and the readings response time at the utility company is illustrated by implementing the authentication protocols.
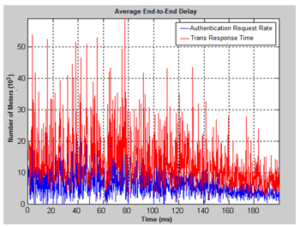
Figure 5: Throughput Rate
Cleary, the delay is affected by the time slot where the meter is assigned in the schedule of time granularity created by the users. Another reason for the increase in the message delay is the computational overheads taking place at the communication layers of the network. Furthermore, the suggested authentication scheme reduced the response time and the communication overhead in the proposed smart metering system because the verification time and the key transfer time produce minimum amount of data overhead. It is noted from Figure 5 that the generation time of the key pair is the lowest among the computation time and verification time. It is clear also from the figure that the generation time of the key-pair was performed in less than 9 ms. When considering the key exchange time over different network bandwidth, the key transfer time was quite high compared with key verification time. The average transfer time was less than one second and the verification time was the 6.2 ms on average. To avoid the risk of key-guessing attack and code replication attack, a strong crypto system together with a secure digital signature were used interchangeably to encode smart meter readings during transmission between the cloud server and the smart meters. As for the results, the proposed security and meter privacy preservation scheme in this paper have offered alternative ways for preserving the cloud storage and time granularity while still providing privacy in smart meters.
7. Conclusion and Future Work
In this paper a data processing and storage system that is applicable to smart meters with many modules that is connected as an internet of things via the public network and uses the full strength of cloud computing and secures users’ privacy and the confidentiality of data exchanged on the grid by encrypting smart meter data before sending to the cloud for the sake of processing and storage with the help of a homomorphic asymmetric key cryptosystem. Each smart meter includes a set of public and private keys to which the grid operator can access and the household owner, on the other hand, can only access the decryption key corresponding to their own smart meter. With the help of the homomorphic feature of the cryptographic technique, several methods are created to enable most of the computing works to be done directly on the data encrypted by the cloud which is the main focus of this model. The smart reading system which is proposed in this paper considers an external storage cloud server and supports multiple time granularities in a privacy preserving manner against host-but-curious providers. The consumer gives different time granularities to different service providers. It is shown in this paper that a service provider gets power consumption of the consumer at only the granted time granularity. The security analysis in this paper confirms that the proposed security protocol preserves the overall privacy of the smart meter readings by allowing an efficient authentication and key management protocol for cloud-based smart metering systems. The performance of the proposed system is analyzed in terms of computation cost and storage cost of a meter. The results confirm also that the key generation time is the highest among the transfer and the verification time. Furthermore, the suggested scheme reduced the overhead of the authentication time as compared to the other existing authentication schemes in smart metering systems. The analysis also provides a solid step towards the practical construction of privacy in cloud-based smart grid technologies.
- G. Lobaccaro, S. Carlucci, and E. Lofstrom,”A review of systems and technologies for smart homes and smart grids,” Energies, 9(5), 1–33, 2016.
- Dark Reading. Smart meter hack shuts off the lights. Available at: http://www.darkreading.com/perimeter/smart-meter-hack-shuts-off-the-lights/d/d-id/1316242. Accessed June 2018.
- B. J. Murrill, E. C. Liu, and R. M. Thompson,”Smart Meter Data:Privacy and Cybersecurity,” CRS Report for Congress [Online]. Available:
http://www.fas.org/sgp/crs/misc/R42338.pdf.(accessed on April 2018). - M. Weiss, A. Helfenstein, F. Mattern, T. Staake, Leveraging smart meter data to recognize home appliances, in: 2012 IEEE International Conference on Pervasive Computing and Communications (PerCom), IEEE, 190–197, 2012.
- S. Bera, S. Misra, and J. J. Rodrigues, “Cloud computing applications for smart grid: A survey,” IEEE Transactions on Parallel and Distributed Systems, 26(5), 1477-1494, 2015.
- J. Zhou, R. Q. Hu, and Y. Qian, “Scalable distributed communication architectures to support advanced metering infrastructure in smart grid,” IEEE Transactions on Parallel and Distributed Systems, 23(7), 1632-1642, 2012.
- L. Ji, W. Lifang, and Y. Li, “Cloud Service based intelligent power monitoring and early-warning system,” in Innovative Smart Grid Technologies-Asia (ISGT Asia 2012 ), IEEE, 1-4, 2012.
- M. Akbar, D.Z.A. Khan, “Modified nonintrusive appliance load monitoring for nonlinear devices,” in: Multitopic Conference, 2007. INMIC 2007. IEEE International, IEEE, , 1–5, 2007.
- X. Fang, D. Yang, and G. Xue, “Evolving smart grid information management cloudward: A cloud optimization perspective,” IEEE Transactions on Smart Grid, 4(3), 111-119, 2013.
- N. Lu, P. Du, P. Paulson, F. Greitzer, X. Guo, and M. Hadley, “A multi-layer, hierarchical information management system for the grid,” in Proc. of IEEE Conf. on Power and Energy Society General Meeting, 632 – 642, Sept. 2012.
- Fournet, C., Kohlweiss, M., Danezis, G., Luo, Z.: Zql: A compiler for privacy-preserving data processing. In: Proceedings of the 22Nd USENIX Conference on Security. 163–178. SEC’13, USENIX Association, Berkeley, CA, USA, 2013.
- P. Deng, L. Yang, A secure and privacy-preserving communication scheme for advanced metering infrastructure, in: Innovative Smart Grid Technologies (ISGT), 2012 IEEE PES, IEEE, 1–5, 2012.
- A. Rial, G. Danezis, Privacy-preserving smart metering, in: Proceedings of the 10th Annual ACM Workshop on Privacy in the Electronic Society, ACM, 49–60, 2011.
- Jo, H.J.; Kim, I.S.; Lee, D.H. Efficient and privacy-preserving metering protocols for smart grid system. IEEE Trans. Smart Grid, 7, 1732–1742, 2016.
- Kursawe, K.; Danezis, G.; Kohlweiss, M. Privacy-Friendly Aggregation for the Smart-Grid. In Proceedings of the 11th International Conference on Privacy Enhancing Technologies (PETS’11), Waterloo, ON, Canada, 27–29, July 2011.
- J.L. Hennessy, D.A. Patterson, Computer Architecture: A Quantitative Approach, Elsevier, 2012.
- G.E. Blelloch, B.M. Maggs, Parallel algorithms, in: Algorithms and Theory of Computation Handbook, Chapman & Hall/CRC, 25–27, 2010.
- Le Métayer, D.: Privacy by design: A formal framework for the analysis of architectural choices. In: Proc. of the Third ACM Conference on Data and Application Security and Privacy. 95–104. CODASPY ’13, ACM, New York, NY, USA, 2013.
- Garcia, F., Jacobs, B.: Privacy-friendly energy-metering via homomorphic encryption. In: Cuellar, J., Lopez, J., Barthe, G., Pretschner, A. (eds.) Security and Trust Management, Lecture Notes in Computer Science, vol. 6710, 226–238. Springer Berlin / Heidelberg , 2011.
- N.P. Smart, F. Vercauteren, Fully homomorphic encryption with relatively small key and ciphertext sizes, in: Public Key Cryptography–PKC 2010, Springer, 420–443, 2010.
- F.D. Garcia, B. Jacobs, Privacy-friendly energy-metering via homomorphic encryption, in: Security and Trust Management, Springer, 2011, 226–238.
- Zhao, J.; Liu, J.; Qin, Z.; Ren, K. Privacy Protection Scheme Based on Remote Anonymous Attestation for Trusted Smart Meters. IEEE Trans. Smart Grid. 2016.
- Gong, Y.; Cai, Y.; Guo, Y.; Fang, Y. A privacy-preserving scheme for incentive-based demand response in the smart grid. IEEE Trans. Smart Grid, 7, 1304–1313, 2016.
- McLaughlin, S.; McDaniel, P.; Aiello, W. Protecting consumer privacy from electric load monitoring. In Proceedings of the 18th ACM Conference on Computer and Communications Security, Chicago, IL, USA, 17–21 October 2011.
- S. Fahl, M. Harbach, T. Muders, and M. Smith. Confidentiality as a service– usable security for the cloud. In TrustCom, 153–162, 2012.
- M. Backes, Meiser, S. Differentially private smart metering with battery recharging. In Data Privacy Management and Autonomous Spontaneous Security; Springer Science + Business Media: New York, NY, USA, 2014; 194–212. Available online: https://eprint.iacr.org/2012/183.pdf. (accessed on 26 August 2018).
- D.P. Rodgers, Improvements in multiprocessor system design, in: ACM SIGARCH Computer Architecture News, 13, IEEE Computer Society Press, . 225–231, 1985.
- Imane Lotfi, Meriem Mandar, "TL-SOC: A Hybrid Decision-Centric Intrusion Detection Framework for Security Operations Centers", Advances in Science, Technology and Engineering Systems Journal, vol. 11, no. 2, pp. 30–42, 2026. doi: 10.25046/aj110204
- Mya Soe Soe Moe, Win Mar Oo, "Hybrid Feature Selection for Anomaly Detection in IoT Network Intrusion Detection Systems", Advances in Science, Technology and Engineering Systems Journal, vol. 11, no. 2, pp. 17–29, 2026. doi: 10.25046/aj110203
- Vikas Thammanna Gowda, Landis Humphrey, Aiden Kadoch, YinBo Chen, Olivia Roberts, "Multi Attribute Stratified Sampling: An Automated Framework for Privacy-Preserving Healthcare Data Publishing with Multiple Sensitive Attributes", Advances in Science, Technology and Engineering Systems Journal, vol. 11, no. 1, pp. 51–68, 2026. doi: 10.25046/aj110106
- Kazuki Iehira, Hiroyuki Inooue, "Detection Method and Mitigation of Server-Spoofing Attacks on SOME/IP at the Service Discovery Phase", Advances in Science, Technology and Engineering Systems Journal, vol. 11, no. 1, pp. 25–32, 2026. doi: 10.25046/aj110103
- Shaista Ashraf Farooqi, Aedah Abd Rahman, Amna Saad, "Federated Learning with Differential Privacy and Blockchain for Security and Privacy in IoMT A Theoretical Comparison and Review", Advances in Science, Technology and Engineering Systems Journal, vol. 10, no. 6, pp. 65–76, 2025. doi: 10.25046/aj100606
- Vinton Morris, Kevin Kornegay, Joy Falaye, Sean Richardson, Marcial Tienteu, Loic Jephson Djomo Tchuenkou, "TIMeFoRCE: An Identity and Access Management Framework for IoT Devices in A Zero Trust Architecture", Advances in Science, Technology and Engineering Systems Journal, vol. 10, no. 6, pp. 1–22, 2025. doi: 10.25046/aj100601
- Mahdi Madani, El-Bay Bourennane, Safwan El Assad, "Hardware and Secure Implementation of Enhanced ZUC Steam Cipher Based on Chaotic Dynamic S-Box", Advances in Science, Technology and Engineering Systems Journal, vol. 10, no. 1, pp. 37–47, 2025. doi: 10.25046/aj100105
- Viktor Denkovski, Irena Stojmenovska, Goce Gavrilov, Vladimir Radevski, Vladimir Trajkovik, "Exploring Current Challenges on Security and Privacy in an Operational eHealth Information System", Advances in Science, Technology and Engineering Systems Journal, vol. 9, no. 2, pp. 45–54, 2024. doi: 10.25046/aj090206
- Daisuke Hirahara, Itaru Kaneko, Junji Nishino, Junichiro Hayano, Oscar Martinez Mozos, Emi Yuda, "Investigating Heart Rate Variability Index Classification in Macaca fascicularis and Humans: Exploring Applications for Personal Identification and Anonymization Studies", Advances in Science, Technology and Engineering Systems Journal, vol. 9, no. 1, pp. 143–148, 2024. doi: 10.25046/aj090114
- Fazalur Rehman, Safwan Hashmi, "Enhancing Cloud Security: A Comprehensive Framework for Real-Time Detection, Analysis and Cyber Threat Intelligence Sharing", Advances in Science, Technology and Engineering Systems Journal, vol. 8, no. 6, pp. 107–119, 2023. doi: 10.25046/aj080612
- Thepparit Banditwattanawong, Masawee Masdisornchote, "Infrastructure-as-a-Service Ontology for Consumer-Centric Assessment", Advances in Science, Technology and Engineering Systems Journal, vol. 8, no. 6, pp. 37–45, 2023. doi: 10.25046/aj080605
- Hiroki Iwanaga, "Photoluminescence Properties of Eu(III) Complexes with Two Different Phosphine Oxide Structures and Their Potential uses in Micro-LEDs, Security, and Sensing Devices: A Review", Advances in Science, Technology and Engineering Systems Journal, vol. 8, no. 3, pp. 154–160, 2023. doi: 10.25046/aj080317
- Mario Cuomo, Federica Massimi, Francesco Benedetto, "Detecting CTC Attack in IoMT Communications using Deep Learning Approach", Advances in Science, Technology and Engineering Systems Journal, vol. 8, no. 2, pp. 130–138, 2023. doi: 10.25046/aj080215
- Richard Romero Izurieta, Segundo Moisés Toapanta Toapanta, Luis Jhony Caucha Morales, María Mercedes Baño Hifóng, Eriannys Zharayth Gómez Díaz, Oscar Marcelo Zambrano Vizuete, Luis Enrique Mafla Gallegos, José Antonio Orizaga Trejo, "Prototype to Identify the Capacity in Cybersecurity Management for a Public Organization", Advances in Science, Technology and Engineering Systems Journal, vol. 8, no. 1, pp. 108–115, 2023. doi: 10.25046/aj080113
- Segundo Moisés Toapanta Toapanta, Rodrigo Humberto Del Pozo Durango, Luis Enrique Mafla Gallegos, Eriannys Zharayth Gómez Díaz, Yngrid Josefina Melo Quintana, Joan Noheli Miranda Jimenez, Ma. Roció Maciel Arellano, José Antonio Orizaga Trejo, "Prototype to Mitigate the Risks, Vulnerabilities and Threats of Information to Ensure Data Integrity", Advances in Science, Technology and Engineering Systems Journal, vol. 7, no. 6, pp. 139–150, 2022. doi: 10.25046/aj070614
- Tarek Nouioua, Ahmed Hafid Belbachir, "The Security of Information Systems and Image Processing Supported by the Quantum Computer: A review", Advances in Science, Technology and Engineering Systems Journal, vol. 7, no. 6, pp. 77–86, 2022. doi: 10.25046/aj070609
- Ibrahim Alwhbi Alharbi, Ali Jaber Almalki, Mnassar Alyami, Cliff Zou, Yan Solihin, "Profiling Attack on WiFi-based IoT Devices using an Eavesdropping of an Encrypted Data Frames", Advances in Science, Technology and Engineering Systems Journal, vol. 7, no. 6, pp. 49–57, 2022. doi: 10.25046/aj070606
- Muhammad Musleh Uddin, Kazi Rafiqul Islam, Md. Monirul Kabir, "An Improved Model to Analyze the Impact of Cyber-Attacks on Power Systems", Advances in Science, Technology and Engineering Systems Journal, vol. 7, no. 5, pp. 27–34, 2022. doi: 10.25046/aj070504
- Kamil Halouzka, Ladislav Burita, Aneta Coufalikova, Pavel Kozak, Petr Františ, "A Comparison of Cyber Security Reports for 2020 of Central European Countries", Advances in Science, Technology and Engineering Systems Journal, vol. 7, no. 4, pp. 105–113, 2022. doi: 10.25046/aj070414
- Tiny du Toit, Hennie Kruger, Lynette Drevin, Nicolaas Maree, "Deep Learning Affective Computing to Elicit Sentiment Towards Information Security Policies", Advances in Science, Technology and Engineering Systems Journal, vol. 7, no. 3, pp. 152–160, 2022. doi: 10.25046/aj070317
- Afsah Sharmin, Farhat Anwar, S M A Motakabber, Aisha Hassan Abdalla Hashim, "A Secure Trust Aware ACO-Based WSN Routing Protocol for IoT", Advances in Science, Technology and Engineering Systems Journal, vol. 7, no. 3, pp. 95–105, 2022. doi: 10.25046/aj070311
- Alvin Thamrin, Haiping Xu, Rui Ming, "Cloud-Based Hierarchical Consortium Blockchain Networks for Timely Publication and Efficient Retrieval of Electronic Health Records", Advances in Science, Technology and Engineering Systems Journal, vol. 7, no. 2, pp. 179–190, 2022. doi: 10.25046/aj070218
- Khosro Salmani, Ken Barker, "Leakage-abuse Attacks Against Forward Private Searchable Symmetric Encryption", Advances in Science, Technology and Engineering Systems Journal, vol. 7, no. 2, pp. 156–170, 2022. doi: 10.25046/aj070216
- Clémentine Gritti, Hao Li, "Efficient Publicly Verifiable Proofs of Data Replication and Retrievability Applicable for Cloud Storage", Advances in Science, Technology and Engineering Systems Journal, vol. 7, no. 1, pp. 107–124, 2022. doi: 10.25046/aj070111
- Kartit Zaid, Diouri Ouafaa, "Taxonomy of Security Techniques for Routing Protocols in Mobile Ad-hoc Networks", Advances in Science, Technology and Engineering Systems Journal, vol. 7, no. 2, pp. 25–31, 2022. doi: 10.25046/aj070203
- Mohammad M. Qabajeh, "Ethical Implications and Challenges in using Social Media: A Comprehensive Study", Advances in Science, Technology and Engineering Systems Journal, vol. 7, no. 1, pp. 47–52, 2022. doi: 10.25046/aj070105
- Janusz Gurzynski, Lukasz Kajda, Marcin Tarasiuk, Tomasz Samotyjak, Zbigniew Stachowicz, Slawomir Kownacki, "Control and Monitoring Systems in Medium Voltage Distribution Networks in Poland – Current Status and Directions of Development", Advances in Science, Technology and Engineering Systems Journal, vol. 6, no. 6, pp. 112–118, 2021. doi: 10.25046/aj060615
- Boris Kontsevoi, Sergei Terekhov, "TETRA™ Techniques to Assess and Manage the Software Technical Debt", Advances in Science, Technology and Engineering Systems Journal, vol. 6, no. 5, pp. 303–309, 2021. doi: 10.25046/aj060534
- Osaretin Eboya, Julia Binti Juremi, "iDRP Framework: An Intelligent Malware Exploration Framework for Big Data and Internet of Things (IoT) Ecosystem", Advances in Science, Technology and Engineering Systems Journal, vol. 6, no. 5, pp. 185–202, 2021. doi: 10.25046/aj060521
- Jianhua Yang, Lixin Wang, Yien Wang, "Enhance Student Learning Experience in Cybersecurity Education by Designing Hands-on Labs on Stepping-stone Intrusion Detection", Advances in Science, Technology and Engineering Systems Journal, vol. 6, no. 4, pp. 355–367, 2021. doi: 10.25046/aj060440
- Juhi Singh, Shalini Agarwal, "Plummeting Makespan by Proficient Workflow Scheduling in Cloud Environment", Advances in Science, Technology and Engineering Systems Journal, vol. 6, no. 3, pp. 40–44, 2021. doi: 10.25046/aj060306
- Niranjan Ravi, Mohamed El-Sharkawy, "Enhanced Data Transportation in Remote Locations Using UAV Aided Edge Computing", Advances in Science, Technology and Engineering Systems Journal, vol. 6, no. 2, pp. 1091–1100, 2021. doi: 10.25046/aj0602124
- Showkat Ahmad Dar, S Palanivel, "Performance Evaluation of Convolutional Neural Networks (CNNs) And VGG on Real Time Face Recognition System", Advances in Science, Technology and Engineering Systems Journal, vol. 6, no. 2, pp. 956–964, 2021. doi: 10.25046/aj0602109
- Anh Nguyen-Duc, Manh-Viet Do, Quan Luong-Hong, Kiem Nguyen-Khac, Hoang Truong-Anh, "On the Combination of Static Analysis for Software Security Assessment – A Case Study of an Open-Source e-Government Project", Advances in Science, Technology and Engineering Systems Journal, vol. 6, no. 2, pp. 921–932, 2021. doi: 10.25046/aj0602105
- Ahmad AA Alkhatib, Abeer Alsabbagh, Randa Maraqa, Shadi Alzubi, "Load Balancing Techniques in Cloud Computing: Extensive Review", Advances in Science, Technology and Engineering Systems Journal, vol. 6, no. 2, pp. 860–870, 2021. doi: 10.25046/aj060299
- Bismark Tei Asare, Kester Quist-Aphetsi, Laurent Nana, "Node-Node Data Exchange in IoT Devices Using Twofish and DHE", Advances in Science, Technology and Engineering Systems Journal, vol. 6, no. 2, pp. 622–628, 2021. doi: 10.25046/aj060271
- Rubin Thottupurathu Jose, Sojan Lal Poulose, "Ontology Based Privacy Preservation over Encrypted Data using Attribute-Based Encryption Technique", Advances in Science, Technology and Engineering Systems Journal, vol. 6, no. 2, pp. 378–386, 2021. doi: 10.25046/aj060244
- Khadija Alaoui, Mohamed Bahaj, "Categorization of RDF Data Management Systems", Advances in Science, Technology and Engineering Systems Journal, vol. 6, no. 2, pp. 221–233, 2021. doi: 10.25046/aj060225
- Zarina Din, Dian Indrayani Jambari, Maryati Mohd Yusof, Jamaiah Yahaya, "Challenges in IoT Technology Adoption into Information System Security Management of Smart Cities: A Review", Advances in Science, Technology and Engineering Systems Journal, vol. 6, no. 2, pp. 99–112, 2021. doi: 10.25046/aj060213
- Saliha Assoul, Anass Rabii, Ounsa Roudiès, "An Operational Responsibility and Task Monitoring Method: A Data Breach Case Study", Advances in Science, Technology and Engineering Systems Journal, vol. 6, no. 1, pp. 1157–1163, 2021. doi: 10.25046/aj0601130
- Devika K N, Ramesh Bhakthavatchalu, "Modified Blockchain based Hardware Paradigm for Data Provenance in Academia", Advances in Science, Technology and Engineering Systems Journal, vol. 6, no. 1, pp. 66–77, 2021. doi: 10.25046/aj060108
- Sinh-Huy Nguyen, Van-Hung Le, "Standardized UCI-EGO Dataset for Evaluating 3D Hand Pose Estimation on the Point Cloud", Advances in Science, Technology and Engineering Systems Journal, vol. 6, no. 1, pp. 1–9, 2021. doi: 10.25046/aj060101
- Pranay Bhardwaj, Carla Purdy, Nawar Obeidat, "A Novel Way to Design ADS-B using UML and TLA+ with Security as a Focus", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 6, pp. 1657–1665, 2020. doi: 10.25046/aj0506197
- Karamath Ateeq, Manas Ranjan Pradhan, Beenu Mago, "Elasticity Based Med-Cloud Recommendation System for Diabetic Prediction in Cloud Computing Environment", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 6, pp. 1618–1633, 2020. doi: 10.25046/aj0506193
- Le Duc Hanh, Huynh Buu Tu, "Computer Vision for Industrial Robot in Planar Bin Picking Application", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 6, pp. 1244–1249, 2020. doi: 10.25046/aj0506148
- Boughanja Manale, Tomader Mazri, "5G, Vehicle to Everything Communication: Opportunities, Constraints and Future Directions", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 6, pp. 1089–1095, 2020. doi: 10.25046/aj0506132
- Mohamed Hedi Fourati, Soumaya Marzouk, Mohamed Jmaiel, Tom Guerout, "Docker-C2A : Cost-Aware Autoscaler of Docker Containers for Microservices-based Applications", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 6, pp. 972–980, 2020. doi: 10.25046/aj0506116
- Abdulla Obaid Al Zaabi, Chan Yeob Yeun, Ernesto Damiani, Gaemyoung, "An Enhanced Conceptual Security Model for Autonomous Vehicles", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 6, pp. 853–864, 2020. doi: 10.25046/aj0506102
- Katerina Prihodova, Miloslav Hub, "Hand-Based Biometric Recognition Technique – Survey", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 6, pp. 689–698, 2020. doi: 10.25046/aj050683
- Pearl Keitemoge, Daniel Tetteh Narh, "Effective Application of Information System for Purchase Process Optimization", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 6, pp. 594–605, 2020. doi: 10.25046/aj050673
- Naeem Ahmed Haq Nawaz, Hamid Raza Malik, Ahmed Jaber Alshaor, Kamran Abid, "A Simulation Based Proactive Approach for Smart Capacity Estimation in the Context of Dynamic Positions and Events", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 6, pp. 423–438, 2020. doi: 10.25046/aj050651
- Jim Scheibmeir, Yashwant Malaiya, "Multi-Model Security and Social Media Analytics of the Digital Twin", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 6, pp. 323–330, 2020. doi: 10.25046/aj050639
- Kofi Osei-Tutu, Yeong-Tae Song, "Enterprise Architecture Institutionalization for Health Information Exchange (HIE) Cloud Migration", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 5, pp. 680–691, 2020. doi: 10.25046/aj050584
- Gautama Wijaya, Nico Surantha, "Multi-layered Security Design and Evaluation for Cloud-based Web Application: Case Study of Human Resource Management System", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 5, pp. 674–679, 2020. doi: 10.25046/aj050583
- Mika Karjalainen, Tero Kokkonen, "Review of Pedagogical Principles of Cyber Security Exercises", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 5, pp. 592–600, 2020. doi: 10.25046/aj050572
- Liana Khamis Qabajeh, Mohammad Moustafa Qabajeh, "Detailed Security Evaluation of ARANz, ARAN and AODV Protocols", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 5, pp. 176–192, 2020. doi: 10.25046/aj050523
- Pham Minh Nam, Phu Tran Tin, "Analysis of Security-Reliability Trade-off for Multi-hop Cognitive Relaying Protocol with TAS/SC Technique", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 5, pp. 54–62, 2020. doi: 10.25046/aj050508
- Adamu Abdullahi Garba, Maheyzah Muhamad Siraj, Siti Hajar Othman, "An Explanatory Review on Cybersecurity Capability Maturity Models", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 4, pp. 762–769, 2020. doi: 10.25046/aj050490
- Vu Nguyen Hoa Hong, Luong Tuan Anh, "Development Trends of Smart Cities in the Future – Potential Security Risks and Responsive Solutions", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 4, pp. 548–556, 2020. doi: 10.25046/aj050465
- Ali Al-Rashid, "Composition of Methods to Ensure Iris Liveness and Authenticity", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 4, pp. 130–143, 2020. doi: 10.25046/aj050417
- Yulyanty Chandra, Roy Willis, Calvin Windoro, Sfenrianto, "Business Process Design for Widuri Indah School Management System with the Support of Cloud Computing", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 3, pp. 536–539, 2020. doi: 10.25046/aj050366
- Maximo Giovani Tanzado Espinoza, Joseline Roxana Neira Melendrez, Luis Antonio Neira Clemente, "A Survey and an IoT Cybersecurity Recommendation for Public and Private Hospitals in Ecuador", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 3, pp. 518–528, 2020. doi: 10.25046/aj050364
- Mainar Swari Mahardika, Achmad Nizar Hidayanto, Putu Agya Paramartha, Louis Dwysevrey Ompusunggu, Rahmatul Mahdalina, Farid Affan, "Measurement of Employee Awareness Levels for Information Security at the Center of Analysis and Information Services Judicial Commission Republic of Indonesia", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 3, pp. 501–509, 2020. doi: 10.25046/aj050362
- Suchitra Abel, Yenchih Tang, Jake Singh, Ethan Paek, "Applications of Causal Modeling in Cybersecurity: An Exploratory Approach", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 3, pp. 380–387, 2020. doi: 10.25046/aj050349
- Nicola Fabiano, "Digital Sovereignty Between “Accountability” and the Value of Personal Data", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 3, pp. 270–274, 2020. doi: 10.25046/aj050335
- A B Manju, Sumathy Subramanian, "Evolution of Privacy Preservation Models in Location-Based Services", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 3, pp. 82–92, 2020. doi: 10.25046/aj050311
- Gillala Rekha, Shaveta Malik, Amit Kumar Tyagi, Meghna Manoj Nair, "Intrusion Detection in Cyber Security: Role of Machine Learning and Data Mining in Cyber Security", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 3, pp. 72–81, 2020. doi: 10.25046/aj050310
- Segundo Moisés Toapanta Toapanta, Daniela Monserrate Moreira Gamboa, Luis Enrique Mafla Gallegos, "Analysis of the Blockchain for Adoption in Electronic Commerce Management in Ecuador", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 2, pp. 762–768, 2020. doi: 10.25046/aj050295
- Segundo Moisés Toapanta Toapanta, Andrés Aurelio García Henriquez, Luis Enrique Mafla Gallegos, "Analysis of Vulnerabilities, Risks and Threats in the Process of Quota Allocation for the State University of Ecuador", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 2, pp. 673–682, 2020. doi: 10.25046/aj050283
- Lylia Alouache, Mohamed Maachaoui, Rachid Chelouah, "Securing Hybrid SDN-based Geographic Routing Protocol using a Distributed Trust Model", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 2, pp. 567–577, 2020. doi: 10.25046/aj050271
- Yakob Utama Chandra, Bahtiar Saleh Abbas, Agung Trisetyarso, Wayan Suparta, Chul-Ho Kang, "Comparison Analysis between Mobile Banking and Mobile Payment as Determinant Factors of Customer Privacy", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 2, pp. 469–475, 2020. doi: 10.25046/aj050260
- Bayan O Al-Amri, Mohammed A. AlZain, Jehad Al-Amri, Mohammed Baz, Mehedi Masud, "A Comprehensive Study of Privacy Preserving Techniques in Cloud Computing Environment", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 2, pp. 419–424, 2020. doi: 10.25046/aj050254
- Mihaela Balanescu, George Suciu, Marius-Alexandru Dobrea, Cristina Balaceanu, Radu-Ioan Ciobanu, Ciprian Dobre, Andrei-Cristian Birdici, Andreea Badicu, Iulia Oprea, Adrian Pasat, "An Algorithm to Improve Data Accuracy of PMs Concentration Measured with IoT Devices", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 2, pp. 180–187, 2020. doi: 10.25046/aj050223
- Segundo Moisés Toapanta Toapanta, José David López Cobeña, Luis Enrique Mafla Gallegos, "Analysis of Cyberattacks in Public Organizations in Latin America", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 2, pp. 116–125, 2020. doi: 10.25046/aj050215
- Karim El bouchti, Soumia Ziti, Fouzia Omary, Nassim Kharmoum, "New Solution Implementation to Protect Encryption Keys Inside the Database Management System", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 2, pp. 87–94, 2020. doi: 10.25046/aj050211
- Mimouna Alkhonaini, Hoda El-Sayed, "Performance Evaluation and Examination of Data Transfer: A Review of Parallel Migration in Cloud Storage", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 2, pp. 57–63, 2020. doi: 10.25046/aj050207
- Mohamed Saleh Al Breiki, Suiping Zhou, Yuan Roger Luo, "Design and Validation of a Meter Band Rate in OpenFlow and OpenDaylight for Optimizing QoS", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 2, pp. 35–43, 2020. doi: 10.25046/aj050205
- José Alomía-Lucero, Jorge Castro-Bedriñana, Doris Chirinos-Peinado, "Rooftop Urban Agriculture Model with Two Tomato Varieties (Lycopersicum esculentum Mill) and Toppings in the High Jungle – Peru", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 1, pp. 446–450, 2020. doi: 10.25046/aj050157
- Nour Mostafa, "Resource Selection Service Based on Neural Network in Fog Environment", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 1, pp. 408–417, 2020. doi: 10.25046/aj050152
- Amit Kumar Tyagi, A. Mohan Krishna, Shaveta Malik, Meghna Manoj Nair, Sreenath Niladhuri, "Trust and Reputation Mechanisms in Vehicular Ad-Hoc Networks: A Systematic Review", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 1, pp. 387–402, 2020. doi: 10.25046/aj050150
- Saleh Albahli, Rehan Ullah Khan, Ali Mustafa Qamar, "A Blockchain-Based Architecture for Smart Healthcare System: A Case Study of Saudi Arabia", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 1, pp. 40–47, 2020. doi: 10.25046/aj050106
- Amine Kardi, Rachid Zagrouba, "Attacks classification and security mechanisms in Wireless Sensor Networks", Advances in Science, Technology and Engineering Systems Journal, vol. 4, no. 6, pp. 229–243, 2019. doi: 10.25046/aj040630
- Evan Hurwitz, Chigozie Orji, "Multi Biometric Thermal Face Recognition Using FWT and LDA Feature Extraction Methods with RBM DBN and FFNN Classifier Algorithms", Advances in Science, Technology and Engineering Systems Journal, vol. 4, no. 6, pp. 67–90, 2019. doi: 10.25046/aj040609
- Allae Erraissi, Abdessamad Belangour, "A Big Data Security Layer Meta-Model Proposition", Advances in Science, Technology and Engineering Systems Journal, vol. 4, no. 5, pp. 409–418, 2019. doi: 10.25046/aj040553
- Shun Yamamoto, Momoyo Ito, Shin-ichi Ito, Minoru Fukumi, "Verification of the Usefulness of Personal Authentication with Aerial Input Numerals Using Leap Motion", Advances in Science, Technology and Engineering Systems Journal, vol. 4, no. 5, pp. 369–374, 2019. doi: 10.25046/aj040548
- Segundo Moisés Toapanta Toapanta, Steven Xavier Romo Sañicela, Danny Wilfrido Barona Valencia, Luis Enrique Mafla Gallegos, "Analysis of Information Security for a Voting Process for Sectional Governments in Ecuador", Advances in Science, Technology and Engineering Systems Journal, vol. 4, no. 5, pp. 352–359, 2019. doi: 10.25046/aj040546
- Alghamdi Abdullah, Mohammed Thanoon, Anwar Alsulami, "Toward a Smart Campus Using IoT: Framework for Safety and Security System on a University Campus", Advances in Science, Technology and Engineering Systems Journal, vol. 4, no. 5, pp. 97–103, 2019. doi: 10.25046/aj040512
- Segundo Moisés Toapanta Toapanta, Allan Fabricio German Diaz, Darío Fernando Huilcapi Subia, Luis Enrique Mafla Gallegos, "Proposal for a Security Model for a Popular Voting System Process in Latin America", Advances in Science, Technology and Engineering Systems Journal, vol. 4, no. 5, pp. 53–60, 2019. doi: 10.25046/aj040507
- Khalil Hariss, Maroun Chamoun, Abed Ellatif Samhat, "Fully Homomorphic Encryption Scheme Based On Complex Numbers", Advances in Science, Technology and Engineering Systems Journal, vol. 4, no. 5, pp. 30–38, 2019. doi: 10.25046/aj040504
- Puneet Bakshi, Sukumar Nandi, "Using Privacy Enhancing and Fine-Grained Access Controlled eKYC to implement Privacy Aware eSign", Advances in Science, Technology and Engineering Systems Journal, vol. 4, no. 4, pp. 347–358, 2019. doi: 10.25046/aj040443
- Segundo Moisés Toapanta Toapanta, Gabriel Enrique Valenzuela Ramos, Félix Gustavo Mendoza Quimi, Luis Enrique Mafla Gallegos, "Prototype of a Security Architecture for a System of Electronic Voting for the Ecuador", Advances in Science, Technology and Engineering Systems Journal, vol. 4, no. 4, pp. 292–299, 2019. doi: 10.25046/aj040437
- Segundo Moisés Toapanta Toapanta, Andrés Javier Bravo Jácome, Maximo Giovanny Tandazo Espinoza, Luis Enrique Mafla Gallegos, "An Immutable Algorithm Approach to Improve the Information Security of a Process for a Public Organization of Ecuador", Advances in Science, Technology and Engineering Systems Journal, vol. 4, no. 3, pp. 25–30, 2019. doi: 10.25046/aj040304
- Robert M. Beswick, "Computer Security as an Engineering Practice: A System Engineering Discussion", Advances in Science, Technology and Engineering Systems Journal, vol. 4, no. 2, pp. 357–369, 2019. doi: 10.25046/aj040245
- Isaac Odun-Ayo, Blessing Udemezue, Abiodun Kilanko, "Cloud Service Level Agreements and Resource Management", Advances in Science, Technology and Engineering Systems Journal, vol. 4, no. 2, pp. 228–236, 2019. doi: 10.25046/aj040230
- Isaac Odun-Ayo, Blessing Idoko, Temidayo Abayomi-Zannu, "Virtualization in Cloud Environment: Bandwidth Management", Advances in Science, Technology and Engineering Systems Journal, vol. 4, no. 2, pp. 221–227, 2019. doi: 10.25046/aj040229
- Isaac Odun-Ayo, Rowland Goddy-Worlu, Victor Geteloma, Emanuel Grant, "A Systematic Mapping Study of Cloud, Fog, and Edge/Mobile Devices Management, Hierarchy Models and Business Models", Advances in Science, Technology and Engineering Systems Journal, vol. 4, no. 2, pp. 91–101, 2019. doi: 10.25046/aj040212
- Imtiaz Parvez, Arif I. Sarwat, "A Spectrum Sharing based Metering Infrastructure for Smart Grid Utilizing LTE and WiFi", Advances in Science, Technology and Engineering Systems Journal, vol. 4, no. 2, pp. 70–77, 2019. doi: 10.25046/aj040209
- Lev Lafayette, Bernd Wiebelt, Dirk von Suchdoletz, Helena Rasche, Michael Janczyk, Daniel Tosello, "The Chimera and the Cyborg", Advances in Science, Technology and Engineering Systems Journal, vol. 4, no. 2, pp. 1–7, 2019. doi: 10.25046/aj040201
- Shruthi Narayanaswamy, Anitha Vijaya Kumar, "Application Layer Security Authentication Protocols for the Internet of Things: A Survey", Advances in Science, Technology and Engineering Systems Journal, vol. 4, no. 1, pp. 317–328, 2019. doi: 10.25046/aj040131
- Maryam Hezaveh, Carlisle Adams, "A Practical PIR-based Scheme for Discovering Nearby Places for Smartphone Applications", Advances in Science, Technology and Engineering Systems Journal, vol. 4, no. 1, pp. 27–39, 2019. doi: 10.25046/aj040104
