Improving customs’ border control by creating a reference database of cargo inspection X-ray images
Volume 2, Issue 3, Page No 60–66, 2017
Adv. Sci. Technol. Eng. Syst. J. 2(3), 60–66 (2017);
 DOI: 10.25046/aj020309
DOI: 10.25046/aj020309
Keywords: X-Ray, Inspection, Cargo, Database, Imaging, Security, Training
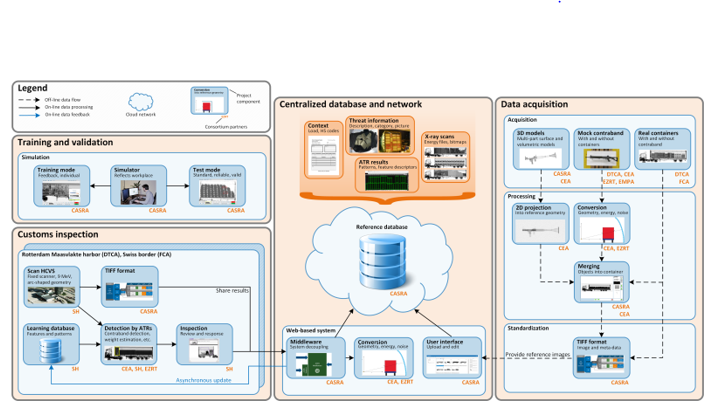
Countries’ effective and efficient border security is becoming increasingly important in today’s global world of economy and trade. To ensure these, customs organisations are responsible for the prevention of illicit goods’ transportation across borders, particularly upon entry. The predicament of the customs administrations will soon be aggravated by both the increase of global trade and the trend towards 100% screening. It is therefore a goal to advance inspection methods to enable successful cargo handling, a scope towards which this research was aimed at. This work was carried out as part of the project ACXIS “Automated Comparison of X-ray Images for cargo Scanning” a European research project within the seventh framework programme answering the call SEC-2012.3.4-1: « Research on Automated Comparison of X-ray Images for cargo Scanning », to improve the process with the largest impact to trade flow: the procedures of freight X-ray scanning. As such, this project was focused on to implementing a manufacturer independent reference database for X-ray images of illicit and non-illicit cargo, developing procedures and algorithms in order to uniform X-ray images of different cargo scanners, and developing a training simulator for inspection officers and a toolbox enclosing several assisted and automated identification techniques for potentially illicit cargo.
1. Introduction
Within the grand scheme of security, border control, and specifically the screening of border traffic cargo, has seen increasing focus in recent years. Given today’s world of trade and the threats that exist to our societies, effective and efficient border controls are increasingly essential. The fiscal integrity and security of the movements of goods across these borders are the responsibility of customs administrations. Accordingly, they are also expected to have a positive impact on the economic competitiveness of their respective nation.
Indeed, customs administrations aim at identifying cargo that is inconsistent with its declaration, contain illicit goods, or that pose threats to society. Smuggling of counterfeited and pirated goods cause harm to a nation’s wellbeing due to missed taxes that could otherwise be put to service for society. The Organization for Economic Co-operation and Development (OECD) estimates that the global international trade in counterfeits and pirated goods in 2007 may amount to USD 250 billion, which would equate to 1.95% of global trade [1]. Cigarettes lead the chart in the European Union with around 35% among all smuggled goods [2]. The increasing number of cargo transported through borders requires innovative inspection procedures. In this direction, automatic detection in cargo screening constitutes an important role.
Within the project ACXIS, cargo screening developments are made in supporting the inspection officers’ work of illicit cargo detection. More specifically, ACXIS develops automated target recognition (ATR) functions to analyse X-ray images of cargo screened at border crossing points (land, air or sea). These functions can continuously self-improve through a central reference data base. This database contains X-ray images of illicit and non-illicit cargo, and it is designed to be manufacturer independent. All these database images, particularly the ones containing threats, constitute a significant tool for the training of screening officers and also for machine learning methods in automated detection algorithms [3,4].
2. Hardware Set-Up and Optimisation
In order to image illicit cargo mock-ups, laboratory X-ray scanners were used at Empa – the Swiss Federal Laboratories for Materials Science and Technology, at CEA – the French Alternative Energies and Atomic Energy Commission, and at EZRT – the German Development Center for X-ray Technology [5]. The Dutch and Swiss customs administrations used their own commercial cargo scanners, such as Smiths Heimann, Rapiscan and Nuctech systems.
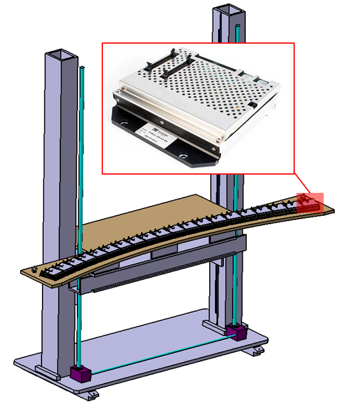
The X-ray source used for the data acquisition at Empa was a portable dual energy 4 and 6 MeV linear accelerator; with a focal spot size of 2 mm (Fig. 1). Certain modifications were made on the existing high energy CT at Empa, in order to optimise the system for this project [6-8]. First, rails were placed on the linear accelerator and the detector towers to allow changing the source-to-detector distance up to 5.4 m. Then, the CT detector were replaced by a newly designed line detector consisting of 20 modules with 32 channels each, made of 30 mm deep CdWO4 scintillators with a pitch of 4.6 mm (X-Scan LCS 4.6, from Detection Technology). A 3D CAD of the new detector is shown in Fig. 2. Careful design and work was carried out in the detector assembly in reducing X-ray scattering. Additionally, new lead and tungsten source collimators were installed to shape the beam according to the detector geometry. An X-ray filter, specially designed, was fitted between the primary and secondary source collimators to flatten the intensity of the X-ray beam over the full detectorwidth (approximately 3 m).
The laboratory scanner built at CEA consists of a linear accelerator, a line detector and a translation table (Fig. 3). The scanning geometry was chosen to match the commercial scanners, namely a horizontal translation of the object, using a vertical detector line. The linear accelerator is a Varian Linatron M9A model, delivering 5, 6 and 9 MeV with a maximal dose rate up to 30 Gy/min. The focal spot size is specified to less than 2 mm in diameter. The detector is made of 10 X-Scan LCS 4.6 modules, assembled on a straight line. A lead collimator is used in front of the active area and the backside is shielded by 5 mm of lead.


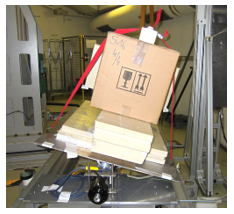
The translation table has a second plate that can be tilt with ±15°, as shown in Fig. 4. This option was used for mock-up objects for which different incident views were needed. Tilting the objects is equivalent to placing them at different heights in a full container, hence several combinations of various positions were operated more easily.
3. Reference Database: An Integration
One of ACXIS key goal is the creation of a reference database of realistic X-ray images of both non-illicit and illicit cargo. Such a database is essential for the development of training systems for customs officers and for providing assisted detection techniques of threats with the use of dedicated algorithms. To construct this database, we rely on historic images provided by customs. However, the number of threat images acquired through real detections remains limited and needs to be increased by additional threat images obtained through simulation. A very important aspect for this project is that all the pre-mentioned images must have a standard format so that images originating from different systems can be incorporated.
3.1. Creating Artificial Images of Illicit Cargo
To efficiently generate X-ray images for the database we can rely on two strategies. The first one consists in using simulation tools to generate artificial X-ray projections of illicit cargo. CEA develops the software CIVA, which integrates a module for modelling X-ray generation, interaction and detection, thus allowing the creation of realistic radiographic projections of any object that is put in the simulation scene. In this case, the shape of the object has to be described by a 3D CAD model and its material has to be specified. For multi-material objects however, each material component has to be segmented, which will result in highly complex objects in the case of a complete cargo. In practice, due to the complexity of container loadings, this approach has not been implemented. The second strategy consists in using real images of legal freights, which are widely available, and to combine these with one or several threat images. For this purpose a so-called “merging tool” has been developed and threat images have been either acquired or created by simulation.
Both approaches have advantages and disadvantages: for instance, cigarettes packs have a very specific texture that is difficult to model in the simulation software and real images have to be used in this case. On the other hand, some realistic 3D models of weapons have been collected and were used to easily generate multiple threat images with various orientations.
3.2. Threat Images
3.2.1 Acquisition from Mock-Up Scans
Based on risk analysis conducted by the customs administrations, threat objects and their locations in the container were identified. Following their recommendations, a set of mock-ups was created with real threat items and simulants, combined with common goods (Figure 5). These were scanned using laboratory systems, and some with a cargo scanner, chosen as reference.
For some illicit items the incidence of the X-ray paths through the object largely influences the produced image. Therefore mock-up X-ray scans were performed with different object tilts so that the best projection could be selected depending on the vertical position of the object in the container.

3.2.2.Generation from Simulation Software
The main objective of the mock-up scans was to enlarge the variety of threat images. For the same purpose, simulation tools were also used in order to generate X-ray images from 3D models of various types of threat items (e.g. weapons).
The acquisition geometry, source spectrum and detector parameters of the high energy scanner were defined in the simulation software. 3D models of different weapons were then loaded into the software environment and multiple projections were created (Figure 6).

The strength of the simulation approach is to create easily a large set of images of an object from different viewpoints. This variety of images of a same object is essential for training learning algorithms for detecting specific threats. Figure 7 displays simulated images of a small weapon, a larger weapon and a bottle that could represent a chemical product used for explosive devices for instance. Each threat has been rotated from side view to top view by steps of 30°.

3.3. Merging Threat Images with Historic Ones
The basic principle of X-ray imaging is the measurement of the X-ray photons which are attenuated when traversing matter. This process is modelled by the Beer-Lambert law, which can be approximated as follows:![]()
Where is the beam intensity at the detection point after traversing N different materials, is the beam intensity at the initial point, and are the linear attenuation coefficient and the thickness of each material, respectively. According to (1), the beam intensity at the detector point corresponds to the combination of the attenuation due to each material successively penetrated by the X-ray beam. It can be decomposed as:![]()
Where is the beam intensity attenuated by the background (non-illicit cargo without threat constituted of j materials) and the parameters and represent the characteristics of the threat element (constituted of N-j materials).
Then, by injecting in (2) the additional measure of the incident beam intensity attenuated by the threat it comes: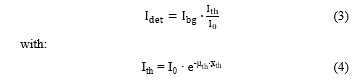
According to (3), we can combine pixel to pixel the attenuation of the threat (threat image acquired as described in earlier subsection) to the grey value of the non-illicit cargo image to create an image of illicit cargo (Figure 8).
The implemented tool allows the insertion of a same threat image multiple times at different positions in the background image and with different orientations. The major difficulty when performing the merging is in the selection of suitable and realistic spots for placing the considered threat.
A first set of illicit cargo images created artificially has been submitted to customs officers, who have assessed and validated the quality of the merging process.
3.4. Creating a Unified X-ray Image Standard
Upon visual inspection of X-ray images, the human brain can easily adapt to different systems, regardless the different parameter variations such as geometric deformations, textures, and levels of contrast or noise. This is not equally the case for automatic algorithms.
Given the large variety of X-ray scanners installed at border checkpoints, it is important that the acquired images are similar in terms of the permissioned parameters. As such, standardising these images enables an increase in the automatic detection performances. Therefore, all X-ray data can be converted into a standardised format and stored in a database, along with the results of the ATRs and useful annotations (Figure 9 centre). This standardisation enables the comparison between scans originating from different X-ray imaging systems. The database consists of set of approximately 30.000 scans as reference material, and new scans can be integrated continuously.
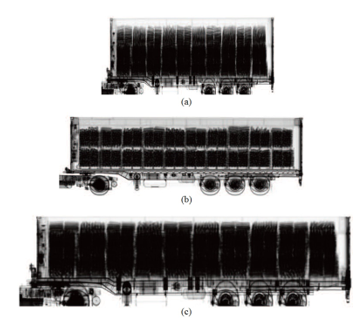
Geometric adaptation is very challenging since projecting a complex load from distant view angles and under different acquisition geometries generates different distortions in the resulting image. The chosen approach is based on the prior knowledge of the acquisition geometry of a given specific scan and of the reference system (standard image geometry). By means of image processing, the corners of the container, and with that its relative position within the X-ray beam, is estimated. In order to transform the given scan to the reference geometry, this approach makes use of the standardised container dimensions and selects the most similar ray paths through the container. We obtained satisfactory conversion results, which are shown in Figure 10. The example shows a conversion of a Euromax image (a) to a SH-HCVS image appearance (b) that looks very similar to a genuinely obtained SH-HCVS image (c). Also, the limitations of the method can be observed, as it is not possible to unambiguously reconstruct the ray paths transmitted horizontally through the container floor region in the reference geometry (c).
Similarly, scanners with very different energy spectra such as mobile systems equipped with 2.5 MeV sources and stationary ones using 9 MeV accelerators produce very different images in terms of contrast and image quality [9]. Based on this analysis, it is not relevant to convert all scanner images to a unique reference configuration but for creating a homogeneous database, we propose to standardise images acquired with systems of energy in the range 4 MeV to 9 MeV. The strategy for the adaptation of contrast is based on the use of X-ray images of step wedges of different materials, which give a unique response curve for a given system. Using these images, we express, for a given thickness of material, the attenuation value of one system as a function of another. The equation of this curve corresponds then to the contrast conversion function, which is applied after the geometric conversion.
Finally, several noise reduction algorithms were evaluated in order to select the best one, BM3D [10] to reduce the noise to the level of the reference scanner, without affecting the image quality (e.g. the texture or the sharpness).
4. Customs Officers Training
The purpose of the integrated reference database is also to be used in educational, computer-based training (CBT) programs aimed to train and qualify customs officers in X-ray image interpretation competency. Earlier studies with airport security officers (e.g. [11, 12]) and customs officers [1] have shown large increases in detection performance as a result of training. In the ACXIS project, a web-based CBT was developed that simulates the image analysis environment (Figure 11). The CBT interface features a variety of supportive functions such as zoom and image enhancement functions to mimic real-work-conditions. In addition, ATR functions are simulated by displayable frames that indicate suspect goods to guide attention and help decision making. The officers, to their discretion, can choose to take this information into consideration, or to ignore it when they believe that the ATR function has generated a false alarm. The waybill information is also provided to the officer, regarding the container contents.
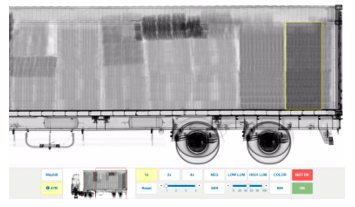
The CBT software incorporates both training and testing modes. The training mode can be used for initial and recurrent X-ray image interpretation training using the large reference database. For each container image, the CBT asks the screening officer whether and where suspect goods are present. Following each image inspection, the officer is given feedback. When a screener correctly reports that an X-ray image contains an item that does not match the waybill or is illicit, the response is counted as a hit. If an incorrect illicit item present answer has been given, the response is categorised as a false alarm. Feedback on missing illicit items and correctly reporting that a container image is harmless is also provided. When an illicit item is present in the image, the feedback includes an additional window displaying the illicit item as a photograph and as an X-ray image. The training time and further details of the simulated scenario can also be examined. Upon completion of a training session, a summary feedback on detection performance in that session is provided. The testing mode is similar to the training mode but feedback is not provided. It can be used to measure X-ray image interpretation competency of customs officers and to conduct research for example on training progress and the value of ATRs.
5. ATR Algorithms Trained on Merged Threats
In comparison with the amount of data required to train and test ATR algorithms, a small sample of images containing illicit goods is available. Building a database derived from merging techniques is therefore crucial, especially for machine learning based algorithms where hundreds of thousands of images are often needed. Thus, a single sample can easily be projected according to different orientations and scales, increasing the variability of the dataset.
Our experience has shown that some differences may appear between the results yielded on artificially generated and real testing sets. Though, while tested on real data, ATR algorithms indicate highly satisfactory performances.
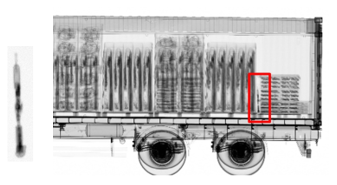
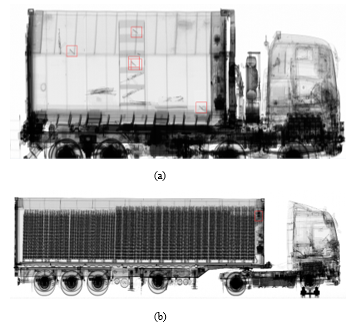
In the framework of the ACXIS project, two prominent ATR tools have been developed and trained on projected images: the Automatic Firearm Detection (Figure 12 (a)) and Reefer Unit Analysis (Figure 12 (b)) algorithms.
6. Conclusions
This work, which was part of the ACXIS project, developed a manufacturer independent reference database for X-ray images of illicit and non-illicit cargo, procedures and algorithms to uniform X-ray images of different cargo scanners and measurement parameters, and an automated identification method of potentially illicit cargo. Historic images of real detection scans, images of illicit cargo mock-ups as well as images of non-illicit cargo were integrated into the reference database. The resulting database was then used for the improved training and evaluation of customs’ officers. The developed software incorporates ATR functions, which together with the impact of the systematic computer-based training is expected to confirm the benefits through a validation study. The foreseen results of the study will confirm that this software increases the success of border controls and reduces the required time necessary for cargo inspection.
Conflict of Interest
The authors declare no conflict of interest.
Acknowledgment
Project ACXIS is supported by the European Commission through the Seventh Framework Programme (FP7).
- S. Michel, M. Mendes, J. C. de Ruiter, G. C. Koomen, and A. Schwaninger, “Increasing X-ray image interpretation competency of cargo security screeners,” Int. J. Ind. Ergon., vol. 44, no. 4, pp. 551–560, 2014.
- A. Bolfing and A. Schwaninger, “Measurement formulae for image-based factors in x-ray imagery,” VICOREG Technical Report, 2007.
- A. Bolfing, T. Halbherr, and A. Schwaninger, How image based factors and human factors contribute to threat detection performance in X-ray aviation security screening. Springer, 2008.
- S. Michel, S. M. Koller, J. C. De Ruiter, R. Moerland, M. Hogervorst, and A. Schwaninger, “Computer-based training increases efficiency in X-ray image interpretation by aviation security screeners,” in Security Technology, 2007 41st Annual IEEE International Carnahan Conference on, 2007, pp. 201–206.
- F. Sukowski, T. Fuchs, and P.-M. Keßling, “High energy X-ray CT of freight containers,” in Fraunhofer Symposium Future Security. 4th Security Research Conference 2009, 2009, pp. 277–281.
- G. Chen, P. Bjorkholm, T. R. Fox, Z. Wilson, and X. Bonsergent, “X-Ray Cargo Inspection: Status and Trends,” in Applications of Accelerators in Research and Industry: Twentieth International Conference, 2009, vol. 1099, pp. 570–573.
- E. A. Miller, J. A. Caggiano, R. C. Runkle, T. A. White, and A. M. Bevill, “Scatter in cargo radiography,” Appl. Radiat. Isot., vol. 69, no. 3, pp. 594–603, 2011.
- N. Reims, T. Schoen, M. Boehnel, F. Sukowski, and M. Firsching, “Strategies for efficient scanning and reconstruction methods on very large objects with high-energy x-ray computed tomography,” in SPIE Optical Engineering & Applications, 2014, pp. 921209–921209.
- K. Dabov, A. Foi, V. Katkovnik and K. Egiazarian, “Image denoising by sparse 3D transform-domain collaborative ltering,” IEEE Transactions on Image Processing, vol. 16, no. 8, 2007.
- S. M. Koller, D. Hardmeier, S. Michel and A. Schwaninger, “Investigating training, transfer and viewpoint effects resulting from recurrent CBT of X-Ray image interpretation,” Journal of Transportation Security, vol. 1, no. 2, pp. 81-106, 2007.
- T. Halbherr, A. Schwaninger, G. R. Budgell and A. Wales, “Airport Security Screener Competency: A Cross-Sectional and Longitudinal Analysis,” International Journal of Aviation Psychology, vol. 23, no. 2, pp. 113-129, 2013.
- Kazuki Iehira, Hiroyuki Inooue, "Detection Method and Mitigation of Server-Spoofing Attacks on SOME/IP at the Service Discovery Phase", Advances in Science, Technology and Engineering Systems Journal, vol. 11, no. 1, pp. 25–32, 2026. doi: 10.25046/aj110103
- Shaista Ashraf Farooqi, Aedah Abd Rahman, Amna Saad, "Federated Learning with Differential Privacy and Blockchain for Security and Privacy in IoMT A Theoretical Comparison and Review", Advances in Science, Technology and Engineering Systems Journal, vol. 10, no. 6, pp. 65–76, 2025. doi: 10.25046/aj100606
- Mahdi Madani, El-Bay Bourennane, Safwan El Assad, "Hardware and Secure Implementation of Enhanced ZUC Steam Cipher Based on Chaotic Dynamic S-Box", Advances in Science, Technology and Engineering Systems Journal, vol. 10, no. 1, pp. 37–47, 2025. doi: 10.25046/aj100105
- Viktor Denkovski, Irena Stojmenovska, Goce Gavrilov, Vladimir Radevski, Vladimir Trajkovik, "Exploring Current Challenges on Security and Privacy in an Operational eHealth Information System", Advances in Science, Technology and Engineering Systems Journal, vol. 9, no. 2, pp. 45–54, 2024. doi: 10.25046/aj090206
- Taiki Yamakami, Akinori Minaduki, "Analysis of Components and Effects of Chest Compression Posture using CPR Training System", Advances in Science, Technology and Engineering Systems Journal, vol. 9, no. 2, pp. 17–25, 2024. doi: 10.25046/aj090203
- Fazalur Rehman, Safwan Hashmi, "Enhancing Cloud Security: A Comprehensive Framework for Real-Time Detection, Analysis and Cyber Threat Intelligence Sharing", Advances in Science, Technology and Engineering Systems Journal, vol. 8, no. 6, pp. 107–119, 2023. doi: 10.25046/aj080612
- Samiha Fairooz, Shakila Yeasmin Miti, Zihadul Islam, Meem Tasfia Zaman, "A Secure Medical History Card Powered by Blockchain Technology", Advances in Science, Technology and Engineering Systems Journal, vol. 8, no. 6, pp. 96–106, 2023. doi: 10.25046/aj080611
- Lucksawan Yutthanakorn, Siam Charoenseang, "Augmented Reality Based Visual Programming of Robot Training for Educational Demonstration Site", Advances in Science, Technology and Engineering Systems Journal, vol. 8, no. 5, pp. 8–16, 2023. doi: 10.25046/aj080502
- Hiroki Iwanaga, "Photoluminescence Properties of Eu(III) Complexes with Two Different Phosphine Oxide Structures and Their Potential uses in Micro-LEDs, Security, and Sensing Devices: A Review", Advances in Science, Technology and Engineering Systems Journal, vol. 8, no. 3, pp. 154–160, 2023. doi: 10.25046/aj080317
- Mario Cuomo, Federica Massimi, Francesco Benedetto, "Detecting CTC Attack in IoMT Communications using Deep Learning Approach", Advances in Science, Technology and Engineering Systems Journal, vol. 8, no. 2, pp. 130–138, 2023. doi: 10.25046/aj080215
- Paulo Gustavo Quinan, Issa Traoré, Isaac Woungang, Ujwal Reddy Gondhi, Chenyang Nie, "Hybrid Intrusion Detection Using the AEN Graph Model", Advances in Science, Technology and Engineering Systems Journal, vol. 8, no. 2, pp. 44–63, 2023. doi: 10.25046/aj080206
- Richard Romero Izurieta, Segundo Moisés Toapanta Toapanta, Luis Jhony Caucha Morales, María Mercedes Baño Hifóng, Eriannys Zharayth Gómez Díaz, Oscar Marcelo Zambrano Vizuete, Luis Enrique Mafla Gallegos, José Antonio Orizaga Trejo, "Prototype to Identify the Capacity in Cybersecurity Management for a Public Organization", Advances in Science, Technology and Engineering Systems Journal, vol. 8, no. 1, pp. 108–115, 2023. doi: 10.25046/aj080113
- Jasmin Softić, Zanin Vejzović, "Operating Systems Vulnerability – An Examination of Windows 10, macOS, and Ubuntu from 2015 to 2021", Advances in Science, Technology and Engineering Systems Journal, vol. 7, no. 6, pp. 230–235, 2022. doi: 10.25046/aj070625
- Segundo Moisés Toapanta Toapanta, Rodrigo Humberto Del Pozo Durango, Luis Enrique Mafla Gallegos, Eriannys Zharayth Gómez Díaz, Yngrid Josefina Melo Quintana, Joan Noheli Miranda Jimenez, Ma. Roció Maciel Arellano, José Antonio Orizaga Trejo, "Prototype to Mitigate the Risks, Vulnerabilities and Threats of Information to Ensure Data Integrity", Advances in Science, Technology and Engineering Systems Journal, vol. 7, no. 6, pp. 139–150, 2022. doi: 10.25046/aj070614
- Tarek Nouioua, Ahmed Hafid Belbachir, "The Security of Information Systems and Image Processing Supported by the Quantum Computer: A review", Advances in Science, Technology and Engineering Systems Journal, vol. 7, no. 6, pp. 77–86, 2022. doi: 10.25046/aj070609
- Muhammad Musleh Uddin, Kazi Rafiqul Islam, Md. Monirul Kabir, "An Improved Model to Analyze the Impact of Cyber-Attacks on Power Systems", Advances in Science, Technology and Engineering Systems Journal, vol. 7, no. 5, pp. 27–34, 2022. doi: 10.25046/aj070504
- Kamil Halouzka, Ladislav Burita, Aneta Coufalikova, Pavel Kozak, Petr Františ, "A Comparison of Cyber Security Reports for 2020 of Central European Countries", Advances in Science, Technology and Engineering Systems Journal, vol. 7, no. 4, pp. 105–113, 2022. doi: 10.25046/aj070414
- Tiny du Toit, Hennie Kruger, Lynette Drevin, Nicolaas Maree, "Deep Learning Affective Computing to Elicit Sentiment Towards Information Security Policies", Advances in Science, Technology and Engineering Systems Journal, vol. 7, no. 3, pp. 152–160, 2022. doi: 10.25046/aj070317
- Afsah Sharmin, Farhat Anwar, S M A Motakabber, Aisha Hassan Abdalla Hashim, "A Secure Trust Aware ACO-Based WSN Routing Protocol for IoT", Advances in Science, Technology and Engineering Systems Journal, vol. 7, no. 3, pp. 95–105, 2022. doi: 10.25046/aj070311
- Khosro Salmani, Ken Barker, "Leakage-abuse Attacks Against Forward Private Searchable Symmetric Encryption", Advances in Science, Technology and Engineering Systems Journal, vol. 7, no. 2, pp. 156–170, 2022. doi: 10.25046/aj070216
- Mohammad Shadeed, Layth Abu Arram, Majdi Owda, "Forensic Analysis of “WhatsApp” Artifacts in Android without Root", Advances in Science, Technology and Engineering Systems Journal, vol. 7, no. 2, pp. 127–132, 2022. doi: 10.25046/aj070212
- Kartit Zaid, Diouri Ouafaa, "Taxonomy of Security Techniques for Routing Protocols in Mobile Ad-hoc Networks", Advances in Science, Technology and Engineering Systems Journal, vol. 7, no. 2, pp. 25–31, 2022. doi: 10.25046/aj070203
- Janusz Gurzynski, Lukasz Kajda, Marcin Tarasiuk, Tomasz Samotyjak, Zbigniew Stachowicz, Slawomir Kownacki, "Control and Monitoring Systems in Medium Voltage Distribution Networks in Poland – Current Status and Directions of Development", Advances in Science, Technology and Engineering Systems Journal, vol. 6, no. 6, pp. 112–118, 2021. doi: 10.25046/aj060615
- Boris Kontsevoi, Sergei Terekhov, "TETRA™ Techniques to Assess and Manage the Software Technical Debt", Advances in Science, Technology and Engineering Systems Journal, vol. 6, no. 5, pp. 303–309, 2021. doi: 10.25046/aj060534
- Osaretin Eboya, Julia Binti Juremi, "iDRP Framework: An Intelligent Malware Exploration Framework for Big Data and Internet of Things (IoT) Ecosystem", Advances in Science, Technology and Engineering Systems Journal, vol. 6, no. 5, pp. 185–202, 2021. doi: 10.25046/aj060521
- Wided Hechkel, Brahim Maaref, Néjib Hassen, "Coupled Apodization Functions Applied to Enhance Image Quality in Ultrasound Imaging using Phased Arrays", Advances in Science, Technology and Engineering Systems Journal, vol. 6, no. 5, pp. 149–157, 2021. doi: 10.25046/aj060517
- Jong-Jin Kim, Sang-Gil Lee, Cheol-Hoon Lee, "A Scheduling Algorithm with RTiK+ for MIL-STD-1553B Based on Windows for Real-Time Operation System", Advances in Science, Technology and Engineering Systems Journal, vol. 6, no. 4, pp. 385–394, 2021. doi: 10.25046/aj060443
- Jianhua Yang, Lixin Wang, Yien Wang, "Enhance Student Learning Experience in Cybersecurity Education by Designing Hands-on Labs on Stepping-stone Intrusion Detection", Advances in Science, Technology and Engineering Systems Journal, vol. 6, no. 4, pp. 355–367, 2021. doi: 10.25046/aj060440
- Kwun-Ping Lai, Jackie Chun-Sing Ho, Wai Lam, "Exploiting Domain-Aware Aspect Similarity for Multi-Source Cross-Domain Sentiment Classification", Advances in Science, Technology and Engineering Systems Journal, vol. 6, no. 4, pp. 01–12, 2021. doi: 10.25046/aj060401
- Andrej Novák, Martin Bugaj, Alena Novák Sedláčková, Branislav Kandera, Anna Stelmach, Tomasz Lusiak, "Use of Unmanned Aerial Vehicles in Aircraft Inspection", Advances in Science, Technology and Engineering Systems Journal, vol. 6, no. 3, pp. 182–188, 2021. doi: 10.25046/aj060321
- Dimas Sirin Madefanny, Suharjito, "Integration Information Systems Design of Material Planning in the Manufacturing Industry using Service Oriented Architecture", Advances in Science, Technology and Engineering Systems Journal, vol. 6, no. 3, pp. 100–106, 2021. doi: 10.25046/aj060311
- Sékou Togola, Sountongnoma Martial Anicet Kiemde, Ahmed Dooguy Kora, "Real Time and Post-Processing Flight Inspection by Drone: A Review", Advances in Science, Technology and Engineering Systems Journal, vol. 6, no. 3, pp. 92–99, 2021. doi: 10.25046/aj060310
- Anh Nguyen-Duc, Manh-Viet Do, Quan Luong-Hong, Kiem Nguyen-Khac, Hoang Truong-Anh, "On the Combination of Static Analysis for Software Security Assessment – A Case Study of an Open-Source e-Government Project", Advances in Science, Technology and Engineering Systems Journal, vol. 6, no. 2, pp. 921–932, 2021. doi: 10.25046/aj0602105
- Murtadha Arif Bin Sahbudin, Chakib Chaouch, Salvatore Serrano, Marco Scarpa, "Application-Programming Interface (API) for Song Recognition Systems", Advances in Science, Technology and Engineering Systems Journal, vol. 6, no. 2, pp. 846–859, 2021. doi: 10.25046/aj060298
- Bismark Tei Asare, Kester Quist-Aphetsi, Laurent Nana, "Node-Node Data Exchange in IoT Devices Using Twofish and DHE", Advances in Science, Technology and Engineering Systems Journal, vol. 6, no. 2, pp. 622–628, 2021. doi: 10.25046/aj060271
- Javier E. Sánchez-Galán, Fatima Rangel Barranco, Jorge Serrano Reyes, Evelyn I. Quirós-McIntire, José Ulises Jiménez, José R. Fábrega, "Using Supervised Classification Methods for the Analysis of Multi-spectral Signatures of Rice Varieties in Panama", Advances in Science, Technology and Engineering Systems Journal, vol. 6, no. 2, pp. 552–558, 2021. doi: 10.25046/aj060262
- Irina Golitsyna, Farid Eminov, Bulat Eminov, "Teaching/Learning Strategies in Context of Education 4.0", Advances in Science, Technology and Engineering Systems Journal, vol. 6, no. 2, pp. 472–479, 2021. doi: 10.25046/aj060254
- Zarina Din, Dian Indrayani Jambari, Maryati Mohd Yusof, Jamaiah Yahaya, "Challenges in IoT Technology Adoption into Information System Security Management of Smart Cities: A Review", Advances in Science, Technology and Engineering Systems Journal, vol. 6, no. 2, pp. 99–112, 2021. doi: 10.25046/aj060213
- Kamel Fahmi Bou-Hamdan, "Design and Implementation of an Ultrasonic Scanner Setup that is Controlled using MATLAB and a Microcontroller", Advances in Science, Technology and Engineering Systems Journal, vol. 6, no. 2, pp. 85–92, 2021. doi: 10.25046/aj060211
- Saliha Assoul, Anass Rabii, Ounsa Roudiès, "An Operational Responsibility and Task Monitoring Method: A Data Breach Case Study", Advances in Science, Technology and Engineering Systems Journal, vol. 6, no. 1, pp. 1157–1163, 2021. doi: 10.25046/aj0601130
- Abdulla Alsharhan, Said Salloum, Khaled Shaalan, "The Impact of eLearning as a Knowledge Management Tool in Organizational Performance", Advances in Science, Technology and Engineering Systems Journal, vol. 6, no. 1, pp. 928–936, 2021. doi: 10.25046/aj0601102
- Walter Cervera-Flores, Yenifer Choque-Garibay, Nahuel Gonzalez-Cordero, Brian Meneses-Claudio, Hernan Solis-Matta, Lourdes Matta-Zamudio, "Level of Empathy in Nursing Students Attending Clinical Practices of the Universidad de Ciencias y Humanidades", Advances in Science, Technology and Engineering Systems Journal, vol. 6, no. 1, pp. 178–183, 2021. doi: 10.25046/aj060120
- Devika K N, Ramesh Bhakthavatchalu, "Modified Blockchain based Hardware Paradigm for Data Provenance in Academia", Advances in Science, Technology and Engineering Systems Journal, vol. 6, no. 1, pp. 66–77, 2021. doi: 10.25046/aj060108
- Pranay Bhardwaj, Carla Purdy, Nawar Obeidat, "A Novel Way to Design ADS-B using UML and TLA+ with Security as a Focus", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 6, pp. 1657–1665, 2020. doi: 10.25046/aj0506197
- Hesham Aly El Zouka, Mustafa Mohamed Hosni, "Time Granularity-based Privacy Protection for Cloud Metering Systems", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 6, pp. 1278–1285, 2020. doi: 10.25046/aj0506152
- Boughanja Manale, Tomader Mazri, "5G, Vehicle to Everything Communication: Opportunities, Constraints and Future Directions", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 6, pp. 1089–1095, 2020. doi: 10.25046/aj0506132
- Abdulla Obaid Al Zaabi, Chan Yeob Yeun, Ernesto Damiani, Gaemyoung, "An Enhanced Conceptual Security Model for Autonomous Vehicles", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 6, pp. 853–864, 2020. doi: 10.25046/aj0506102
- Sheetal Jagdale, Milind Shah, "Extending the Classifier Algorithms in Machine Learning to Improve the Performance in Spoken Language Understanding Systems Under Deficient Training Data", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 6, pp. 464–471, 2020. doi: 10.25046/aj050655
- Jim Scheibmeir, Yashwant Malaiya, "Multi-Model Security and Social Media Analytics of the Digital Twin", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 6, pp. 323–330, 2020. doi: 10.25046/aj050639
- Daniel Sutopo Pamungkas, Arjon Turnip, "Electro-tactile Stimulation for Augmenting Finger Motoric Learning", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 6, pp. 143–147, 2020. doi: 10.25046/aj050616
- Hana Yousuf, Asma Qassem Al-Hamad, Said Salloum, "An Overview on CryptDb and Word2vec Approaches", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 5, pp. 1282–1287, 2020. doi: 10.25046/aj0505154
- Gautama Wijaya, Nico Surantha, "Multi-layered Security Design and Evaluation for Cloud-based Web Application: Case Study of Human Resource Management System", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 5, pp. 674–679, 2020. doi: 10.25046/aj050583
- Mika Karjalainen, Tero Kokkonen, "Review of Pedagogical Principles of Cyber Security Exercises", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 5, pp. 592–600, 2020. doi: 10.25046/aj050572
- Liana Khamis Qabajeh, Mohammad Moustafa Qabajeh, "Detailed Security Evaluation of ARANz, ARAN and AODV Protocols", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 5, pp. 176–192, 2020. doi: 10.25046/aj050523
- Hicham Moujahid, Bouchaib Cherradi, Oussama El Gannour, Lhoussain Bahatti, Oumaima Terrada, Soufiane Hamida, "Convolutional Neural Network Based Classification of Patients with Pneumonia using X-ray Lung Images", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 5, pp. 167–175, 2020. doi: 10.25046/aj050522
- Pham Minh Nam, Phu Tran Tin, "Analysis of Security-Reliability Trade-off for Multi-hop Cognitive Relaying Protocol with TAS/SC Technique", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 5, pp. 54–62, 2020. doi: 10.25046/aj050508
- Adamu Abdullahi Garba, Maheyzah Muhamad Siraj, Siti Hajar Othman, "An Explanatory Review on Cybersecurity Capability Maturity Models", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 4, pp. 762–769, 2020. doi: 10.25046/aj050490
- Soumiya Ain El Hayat, Mohamed Bahaj, "Modeling and Transformation from Temporal Object Relational Database into Mongodb: Rules", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 4, pp. 618–625, 2020. doi: 10.25046/aj050473
- Vu Nguyen Hoa Hong, Luong Tuan Anh, "Development Trends of Smart Cities in the Future – Potential Security Risks and Responsive Solutions", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 4, pp. 548–556, 2020. doi: 10.25046/aj050465
- Maximo Giovani Tanzado Espinoza, Joseline Roxana Neira Melendrez, Luis Antonio Neira Clemente, "A Survey and an IoT Cybersecurity Recommendation for Public and Private Hospitals in Ecuador", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 3, pp. 518–528, 2020. doi: 10.25046/aj050364
- Mainar Swari Mahardika, Achmad Nizar Hidayanto, Putu Agya Paramartha, Louis Dwysevrey Ompusunggu, Rahmatul Mahdalina, Farid Affan, "Measurement of Employee Awareness Levels for Information Security at the Center of Analysis and Information Services Judicial Commission Republic of Indonesia", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 3, pp. 501–509, 2020. doi: 10.25046/aj050362
- Suchitra Abel, Yenchih Tang, Jake Singh, Ethan Paek, "Applications of Causal Modeling in Cybersecurity: An Exploratory Approach", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 3, pp. 380–387, 2020. doi: 10.25046/aj050349
- Dennis Luqman, Sani Muhamad Isa, "Machine Learning Model to Identify the Optimum Database Query Execution Platform on GPU Assisted Database", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 3, pp. 214–225, 2020. doi: 10.25046/aj050328
- Gillala Rekha, Shaveta Malik, Amit Kumar Tyagi, Meghna Manoj Nair, "Intrusion Detection in Cyber Security: Role of Machine Learning and Data Mining in Cyber Security", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 3, pp. 72–81, 2020. doi: 10.25046/aj050310
- Segundo Moisés Toapanta Toapanta, Daniela Monserrate Moreira Gamboa, Luis Enrique Mafla Gallegos, "Analysis of the Blockchain for Adoption in Electronic Commerce Management in Ecuador", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 2, pp. 762–768, 2020. doi: 10.25046/aj050295
- Segundo Moisés Toapanta Toapanta, Andrés Aurelio García Henriquez, Luis Enrique Mafla Gallegos, "Analysis of Vulnerabilities, Risks and Threats in the Process of Quota Allocation for the State University of Ecuador", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 2, pp. 673–682, 2020. doi: 10.25046/aj050283
- Lylia Alouache, Mohamed Maachaoui, Rachid Chelouah, "Securing Hybrid SDN-based Geographic Routing Protocol using a Distributed Trust Model", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 2, pp. 567–577, 2020. doi: 10.25046/aj050271
- Emel Demircan, Elliot Recinos, I-Hung Khoo, Sharon Teng, Will Wu, "Understanding Human Perception of Vibrotactile Feedback in Walking and Running Tasks", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 2, pp. 537–544, 2020. doi: 10.25046/aj050267
- Segundo Moisés Toapanta Toapanta, José David López Cobeña, Luis Enrique Mafla Gallegos, "Analysis of Cyberattacks in Public Organizations in Latin America", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 2, pp. 116–125, 2020. doi: 10.25046/aj050215
- Karim El bouchti, Soumia Ziti, Fouzia Omary, Nassim Kharmoum, "New Solution Implementation to Protect Encryption Keys Inside the Database Management System", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 2, pp. 87–94, 2020. doi: 10.25046/aj050211
- José Alomía-Lucero, Jorge Castro-Bedriñana, Doris Chirinos-Peinado, "Rooftop Urban Agriculture Model with Two Tomato Varieties (Lycopersicum esculentum Mill) and Toppings in the High Jungle – Peru", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 1, pp. 446–450, 2020. doi: 10.25046/aj050157
- Amit Kumar Tyagi, A. Mohan Krishna, Shaveta Malik, Meghna Manoj Nair, Sreenath Niladhuri, "Trust and Reputation Mechanisms in Vehicular Ad-Hoc Networks: A Systematic Review", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 1, pp. 387–402, 2020. doi: 10.25046/aj050150
- Evaristus Didik Madyatmadja, Chelsea Adora, "Designing and Using a MySQL Database for Human Resource Management", Advances in Science, Technology and Engineering Systems Journal, vol. 4, no. 6, pp. 285–290, 2019. doi: 10.25046/aj040636
- Amine Kardi, Rachid Zagrouba, "Attacks classification and security mechanisms in Wireless Sensor Networks", Advances in Science, Technology and Engineering Systems Journal, vol. 4, no. 6, pp. 229–243, 2019. doi: 10.25046/aj040630
- Evan Hurwitz, Chigozie Orji, "Multi Biometric Thermal Face Recognition Using FWT and LDA Feature Extraction Methods with RBM DBN and FFNN Classifier Algorithms", Advances in Science, Technology and Engineering Systems Journal, vol. 4, no. 6, pp. 67–90, 2019. doi: 10.25046/aj040609
- Allae Erraissi, Abdessamad Belangour, "A Big Data Security Layer Meta-Model Proposition", Advances in Science, Technology and Engineering Systems Journal, vol. 4, no. 5, pp. 409–418, 2019. doi: 10.25046/aj040553
- Segundo Moisés Toapanta Toapanta, Steven Xavier Romo Sañicela, Danny Wilfrido Barona Valencia, Luis Enrique Mafla Gallegos, "Analysis of Information Security for a Voting Process for Sectional Governments in Ecuador", Advances in Science, Technology and Engineering Systems Journal, vol. 4, no. 5, pp. 352–359, 2019. doi: 10.25046/aj040546
- Gustavo Gallegos Dávalos, Pedro Freddy Huamaní Navarrete, "Application of Fractal Algorithms to Identify Cardiovascular Diseases in ECG Signals", Advances in Science, Technology and Engineering Systems Journal, vol. 4, no. 5, pp. 143–150, 2019. doi: 10.25046/aj040519
- Alghamdi Abdullah, Mohammed Thanoon, Anwar Alsulami, "Toward a Smart Campus Using IoT: Framework for Safety and Security System on a University Campus", Advances in Science, Technology and Engineering Systems Journal, vol. 4, no. 5, pp. 97–103, 2019. doi: 10.25046/aj040512
- Segundo Moisés Toapanta Toapanta, Allan Fabricio German Diaz, Darío Fernando Huilcapi Subia, Luis Enrique Mafla Gallegos, "Proposal for a Security Model for a Popular Voting System Process in Latin America", Advances in Science, Technology and Engineering Systems Journal, vol. 4, no. 5, pp. 53–60, 2019. doi: 10.25046/aj040507
- Segundo Moisés Toapanta Toapanta, Gabriel Enrique Valenzuela Ramos, Félix Gustavo Mendoza Quimi, Luis Enrique Mafla Gallegos, "Prototype of a Security Architecture for a System of Electronic Voting for the Ecuador", Advances in Science, Technology and Engineering Systems Journal, vol. 4, no. 4, pp. 292–299, 2019. doi: 10.25046/aj040437
- Segundo Moisés Toapanta Toapanta, Adrian Alberto Chávez Monteverde, Javier Gonzalo Ortiz Rojas, Luis Enrique Mafla Gallegos, "Proposal of Ledger Technology to Apply to a Public Organization in Ecuador", Advances in Science, Technology and Engineering Systems Journal, vol. 4, no. 3, pp. 251–259, 2019. doi: 10.25046/aj040333
- Sohail Akhtar, Adarsh Tandiya, Medhat Moussa, Cole Tarry, "An Efficient Automotive Paint Defect Detection System", Advances in Science, Technology and Engineering Systems Journal, vol. 4, no. 3, pp. 171–182, 2019. doi: 10.25046/aj040323
- Segundo Moisés Toapanta Toapanta, Andrés Javier Bravo Jácome, Maximo Giovanny Tandazo Espinoza, Luis Enrique Mafla Gallegos, "An Immutable Algorithm Approach to Improve the Information Security of a Process for a Public Organization of Ecuador", Advances in Science, Technology and Engineering Systems Journal, vol. 4, no. 3, pp. 25–30, 2019. doi: 10.25046/aj040304
- Zakaria Bousalem, Inssaf El Guabassi, Ilias Cherti, "Relational Databases Versus HBase: An Experimental Evaluation", Advances in Science, Technology and Engineering Systems Journal, vol. 4, no. 2, pp. 395–401, 2019. doi: 10.25046/aj040249
- Toru Tanimura, Hiroki Takada, Akihiro Sugiura, Fumiya Kinoshita, Masumi Takada, "Effects of The Low-Resolution 3D Video Clip on Cerebrum Blood Flow Dynamics", Advances in Science, Technology and Engineering Systems Journal, vol. 4, no. 2, pp. 380–386, 2019. doi: 10.25046/aj040247
- Robert M. Beswick, "Computer Security as an Engineering Practice: A System Engineering Discussion", Advances in Science, Technology and Engineering Systems Journal, vol. 4, no. 2, pp. 357–369, 2019. doi: 10.25046/aj040245
- Shruthi Narayanaswamy, Anitha Vijaya Kumar, "Application Layer Security Authentication Protocols for the Internet of Things: A Survey", Advances in Science, Technology and Engineering Systems Journal, vol. 4, no. 1, pp. 317–328, 2019. doi: 10.25046/aj040131
- Tatjana Šimović, Mislav Gazdović, "Automation System for Regulation Optimization in Power Transformer Design", Advances in Science, Technology and Engineering Systems Journal, vol. 4, no. 1, pp. 1–7, 2019. doi: 10.25046/aj040101
- Lin Dong, Akira Rinoshika, "Analysis and Methods on The Framework and Security Issues for Connected Vehicle Cloud", Advances in Science, Technology and Engineering Systems Journal, vol. 3, no. 6, pp. 105–110, 2018. doi: 10.25046/aj030611
- Yoshihiko Tagawa, Masayuki Omoto, Hiroo Matsuse, Naoto Shiba, "Simulation Strategy to Enhance Oxygen Uptake and Reaction Forces at Leg Joints and Vertebral Bodies During Ergometer Exercise Under Altered Gravity", Advances in Science, Technology and Engineering Systems Journal, vol. 3, no. 4, pp. 8–20, 2021. doi: 10.25046/aj030402
- Ola Surakhi, Mohammad Khanafseh, Yasser Jaffal, "An enhanced Biometric-based Face Recognition System using Genetic and CRO Algorithms", Advances in Science, Technology and Engineering Systems Journal, vol. 3, no. 3, pp. 116–124, 2018. doi: 10.25046/aj030316
- Abul Kalam Azad, Md. Yamin Mollah, "EAES: Extended Advanced Encryption Standard with Extended Security", Advances in Science, Technology and Engineering Systems Journal, vol. 3, no. 3, pp. 51–56, 2018. doi: 10.25046/aj030307
- Dhiman Chowdhury, Mrinmoy Sarkar, Mohammad Zakaria Haider, "A Cyber-Vigilance System for Anti-Terrorist Drives Based on an Unmanned Aerial Vehicular Networking Signal Jammer for Specific Territorial Security", Advances in Science, Technology and Engineering Systems Journal, vol. 3, no. 3, pp. 43–50, 2018. doi: 10.25046/aj030306
- Rasel Ahmmed, Md. Asadur Rahman, Md. Foisal Hossain, "An Advanced Algorithm Combining SVM and ANN Classifiers to Categorize Tumor with Position from Brain MRI Images", Advances in Science, Technology and Engineering Systems Journal, vol. 3, no. 2, pp. 40–48, 2018. doi: 10.25046/aj030205
- Nicola Fabiano, "The Internet of Things ecosystem: the blockchain and data protection issues", Advances in Science, Technology and Engineering Systems Journal, vol. 3, no. 2, pp. 1–7, 2018. doi: 10.25046/aj030201
- Asma Meddeb, Hajer Jmii, Souad Chebbi, "Security Analysis and the Contribution of UPFC for Improving Voltage Stability", Advances in Science, Technology and Engineering Systems Journal, vol. 3, no. 1, pp. 404–411, 2018. doi: 10.25046/aj030149
- Luca Dariz, Gianpiero Costantino, Massimiliano Ruggeri, Fabio Martinelli, "A Joint Safety and Security Analysis of message protection for CAN bus protocol", Advances in Science, Technology and Engineering Systems Journal, vol. 3, no. 1, pp. 384–393, 2018. doi: 10.25046/aj030147
- Anass Sedrati, Abdellatif Mezrioui, "A Survey of Security Challenges in Internet of Things", Advances in Science, Technology and Engineering Systems Journal, vol. 3, no. 1, pp. 274–280, 2018. doi: 10.25046/aj030133
- Hiroaki Anada, Seiko Arita, "Short CCA-Secure Attribute-Based Encryption", Advances in Science, Technology and Engineering Systems Journal, vol. 3, no. 1, pp. 261–273, 2018. doi: 10.25046/aj030132
