5G, Vehicle to Everything Communication: Opportunities, Constraints and Future Directions
Volume 5, Issue 6, Page No 1089–1095, 2020
Adv. Sci. Technol. Eng. Syst. J. 5(6), 1089–1095 (2020);
 DOI: 10.25046/aj0506132
DOI: 10.25046/aj0506132
Keywords: 5G, V2X, Security, Challenges
The 5G, as a new source of telecommunication infrastructure technology, has attracted many stakeholders to promote the progress of its standards and the development of its technology industry. The 5G reinforces new technologies and delivers vehicles for everything services (V2X) to drivers and passengers. It also offers several advantages. On the other hand, due to pervasive network connectivity, there are significant trust, security, and privacy issues for vehicles this affects the overall performance of 5G V2X. This paper provides a comprehensive review; and particularly; an overview of the mobile communication system and introduces the Next Generation (NG). additionally, the paper concentrates on the fifth-generation structure and its use cases. The 5G-V2X as a new field of communication requires more attention and focus, moreover, it aims to present the problems facing this new technology as well, and some future directions for research have been highlighted.
1. Introduction
Telecommunication changed radically in recent years, from traditional wired telephony oriented services to data-based services, from non-shrewd devices to smart handheld and versatile mobile computers.
Mobile ad hoc networks (MANET) formed a network without infrastructure because the mobile nodes in the network dynamically establish a path to transmit data packets. The strength of this network is its rapid development, robustness, flexibility, and mobility. With the rapid growth of this network and the massive focus on data creation through mobile phones and devices. Previous generations become unable to manipulate this data because they achieve their limits. For this purpose, a fifth-generation has been developed. The appearance of 5G has given several advantages to mobile involvement and some new technologies appear with it [1] to enhance communication between devices:
- Millimeter waves
- Small cells
- Massive multi-input multi-output (MIMO)
- Beamforming
- Full-duplex.
The 5G named also next-generation (NG), is emerging the network. Due to their capacity to handle large and diverse sets of devices, the NG is expected to bring a true wireless worldwide web (WWWW) which will have the ability to support massive data rates and a huge number of user applications and services. Moreover, it will reduce latency and will improve energy efficiency.
The 5G aims to create a networked society, where anyone can view and share information anytime from anywhere [2]. It will bring wireless connectivity for everything that is connected. Due to this fact, 5G faces some issues that can be summarized as follows:
- The number of connected devices has increased considerably;
- Traffic has increased significantly;
- Wide variety of applications with various characteristics and demands.
Our goal is to provide a detailed review where we will show the development brought to 5G and present some use cases and application of 5G, especially we will discuss the relation between 5G and V2X communication and application. This paper is an extension of an original work presented at the international conference of computer science and renewable energies (ICCSRE) [3]. In the previous article, we have shown that with the application of 5G the generation of data will increase. For that, it is essential to implement a dedicated storage method to manage this large quantity of data. In this article, we will focus more on NG itself; explain the difference between 5G and prior generation, and some applications that allow generating this data. For this reason, our paper is organized as follows: In the first section, we will present an overview of the development of mobile networks. Then, we will introduce the 5G new radio access technologies in section two. We will provide some applications for 5G in section four. Further, in section five, we will introduce the 5G V2X application, and we will present the security issues that face the 5G V2X services. To address this security issue, we present some future directions for further studies to promote greater efforts on trust, confidence, assurance, and trustworthiness in 5G V2X services. Finally, we will conclude our paper.
2. Overview
So far, four generations of cellular communication systems have already been adopted [4]. Starting with the 1G that relies on an analog FM cellular system to 4G. With the huge interest in data creation and connected devices, the past generation achieved their limits. To deal with this problem the 5G has been created to solve the problem of the frequency spectrum cutting [5]. The 5G performances will develop later on with the progressive introduction of new technologies: use of millimeter waves, small cell, massive MIMO (or smart micro antennas), beamforming, and full-duplex [6], we will briefly explain those new advances.
- Massive MIMO: the concept was created in [7]. The purpose is to permit the system to achieve higher throughput. The massive MIMO can provide multiple services to various customers simultaneously in all directions.
- Millimetric waves: mobile wireless systems have been always in the band 300MHz – 3GHz. However, the spectrum becomes congested with the huge increase in mobile data traffic and the number of connected devices and the frequency band is coming to an end, creating a signal cutoff [8]. The proposed solution was to use millimeter waves. This latter refers to the wave between 30 and 300 GHz, and their wavelength varies between 1 and 10 mm [9].
- Small cells: are considered to be low-power radio switching equipment controlled by the administrator [10]. We can describe a small cell as a little power base station that will be very nearby to the usual towers and transmit the signal without having any break of connection or attenuation of the signal bypassing all obstacles.
- Beamforming: given the number of antennas used in 5G, the signal will be transmitted from the base station to the devices in an unmonitored manner [11]. This technique permits the orientating of the signal.
- Full duplex (FD): this technique brings to the device the capability to Send and get the data on the identical frequency band. FD improves the efficiency of the network.
The figure 1 summarizes those advances.
3. 5G new radio access technology
5G wireless is conceived to provide a connected environment, where information can be accessed and shared anywhere and anytime, by anyone and deliver a wireless connection for anything. However, with this requirement, the 5G will face several challenges like the volume of traffic the large variety of applications, and so on. To overcome this difficult task, 5G wireless access demands not just new functionality, but also a much more spectrum and larger frequency bands. The millimeter waves provide a huge spectral range, wide transmission bandwidth for the 5G [12]. The figure 2 shows the frequency spectrum.

Figure 1: 5G Advances
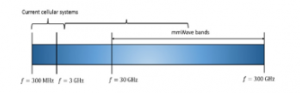
Figure 2: The frequency spectrum of the current and NG communication system
The past generations of cellular mobile systems were operating below 6 GHz frequencies, but with the implementation of the mm waves frequencies, much more spectrum is available and can deal with the huge amount of connected devices With the use of this principle in both 5G and Long Term Evolution (LTE), will have covered to have wireless access [13]. The appearance of 5G did not stop the evolution of LTE. LTE continues its evolution to meet the growing demand for 5G. This evolution is called the LTE evolution [14]. Figure 3 shows the LTE and 5G radio access.

Figure 3: 5G radio access
3.1. Spectrum for 5G
Due to the lack of spectrum in the conventional mobile wireless band regulator started to envisage alternative approaches to manage the spectrum availability. For this reason, one of the major adjustments between the past generation of mobile communication and the fifth generation is the use of a higher frequency spectrum in the millimeter-wave interval [15]. It is about technological evolution and revolution, mixed to the spectrum. This approach is made to make the spectrum more available with a higher frequency to exploit the frequency above 6 GHz and provide more bandwidth for mobile applications. The regulators have taken some measures for the proper functioning of the new generation among them:
- Spectrum sharing: technologies that will allow wireless broadband applications to operate bands assigned to multiple sites.
- Spectral efficiency: to minimize the bandwidth needed to supply a given quality of service level.
- Advanced MIMO: for higher modulation and lower signaling throughput.
- Densification: 5G communication system aims to get mobile customers closer to base stations, particularly by implementing a dense network of small cells.
All these developments reduce the amount of spectrum required for a single user, which indirectly leads to a greater spectrum availability to serve more users with an increased Quality of Services (QoS).
3.2. Use cases for 5G
5G will need to bring solutions for a variety of equipment running within a completely heterogeneous environment. The new human-centric applications include several fields: augmented reality, virtual reality, and gaming. This requires an extremely higher flow rate and reduced delay. In other words, we can differentiate two segments for machine-model communication:
- The Massive Internet of things (MIoT): which is categorized by a large number of low-cost device connections, in this case, a small amount of data supported by each device with extended battery lifetime and a wide range of coverage. This type is used more in the field of intelligent building, transport logistics, and agriculture.
- The critical internet of things (CIoT): shaped with highly dependable, extremely low-latency connectivity. For example, it can support autonomous vehicles, robotic surgery, and road safety.
Unlike previous products, 5G aims to bring improved support for a diversity of distinct services. 5G target three sets of use cases with very unique features:
- Enhanced Mobile Broadband (eMBB): This kind of use case is a direct extension of the conventional mobile broadband connection scenario based on the current mobile telecommunication standards. This set of boxes addresses broadband access everywhere, and in highly inhabited areas. This later provides the user with multiple services such as multimedia and 3D video [16].
- Large scale machine to machine communication (mMTC): with high latency and stability demands. This type of use case mainly relates machine to machine communication (MTC). It enables mobile communication with vehicles, this type requires simultaneous broadband and high mobility capacity. The problem with the mMTC that requires increased reliability and decreased latency [17].
- Ultra-Reliable Low Latency Communication (URLLC): the development of IoT is leading to a multiplication of wireless attached devices carrying TCM network traffic. It is intended that the expected number of these devices will soon surpass. The goal of mMTC is to provide the ability to connect a large set of equipment that may occasionally send a small quantity of data. mMTC devices are categorized by having long battery life and can be deployed remotely [16].
3.3. The key feature of 5G
The 5G was defined by the 3rd generation partnership project (3GPP) as a collection of key functionalities with associated parameters. In addition to the technological and protocolling environment and architecture inherited from the 4G system. We can summarize those technologies as follows:
- 3D MIMO: to ensure high performance in terms of spectral effectiveness. MIMO was firstly implemented in the LTE system was improved than the third generation [18]. The old system was composed of traditional antennas and composed of 8 to 10 elements stacked in a column, but with the evolution, restraint adjustments have been made and provide a downward tilt angle for network convergence. In this situation, the identical radio frequency (RF) pulses are delivered to everyone on the antenna. In such a manner, with the implementation of 3D MIMO, the signal will be simultaneously monitored in both the horizontal and vertical levels.
- Software-Defined Air Interface (IA): the fifth generation intended to handle various use scenarios and a broad range of the spectrum with a signal AI. For this reason, a unified framework was defined to handle different usage scenarios.
- User-Centric Network: to ensure the most suitable operator environment on the entire network, based on user requirements and the network conditions. Therefore, to provide a better user-centric experience the 5G network should handle a user context awareness where the network can serve the user more effectively when there is more information or expertise which means that the more information is loaded onto the network, the better the customer is served. Also, it should have the MEC functionality that includes traffic, security, transport isolation computing, and storage resources. Last and not least it should have a core network perspective to plan the use of the base stations.
- SDN/NFV: This technology enables the management and coordination of various network tranches on a shared physical infrastructure [19].
4. 5G applications
4.1. 5G and Mobile Ad Hoc Network
Mobile Ad Hoc Network (MANET) refers to a signal type of cellular network that contains mobile wireless nodes for communication [20]. These nodes are dynamically organized in random and volatile topologies. The utility to use the 5G for wireless communication in the field of MANET is to give more efficiency to the network. With the implementation of the NG, the MANET network achieves high levels of flexibility and intelligence. Figure 4 illustrates an example of MANET using the 5G connection.

Figure 4: An example of MANET applied in 5G
The NG allows the connection of several devices and provides communication between multiple types of equipment. This communication can be classified into two different parts the device to device communication (D2D) and the vehicle for everything communication (V2X).
D2D communication: also known as proximity service communication (ProSe). The main objective of this functionality is to allow mobile devices to explore the presence of any other close devices within a radius of 500 meters and establish direct communication with it. The basic D2D procedures consist of three main steps:
- Device detection (ProSe discovery): detects if there are other devices nearby.
- Link parameters: establish a link between the associated devices.
- Data communication (ProSe communication): send or receive data via a set of links.
Figure 5 shows the D2D communication.

Figure 5: Basic ProSe procedure
V2X communication: are the exchanges between the vehicle and any device that may impact the vehicle, and the opposite. The X can for instance be on a different vehicle (V), an area of infrastructure (A/I), a pedestrian (P), a domicile (D), or any entity that communicates with the vehicle. We can summarize the cases of use of the vehicle with X as follows:
- Vehicular internet: user experience similar to that provided by their home and network.
- Pre-collision detection and mitigation: detect impending collisions and exchange relevant data from the vehicles involved.
- Cooperative vehicles: V2V and V2I communication to safely operate vehicles such as a train of autonomous cars on a highway.
- V2V information exchange: allows the vehicle to communicate on road to avoid any congestion.
5. 5G and V2X
The 5G mobile communication system will continue to emerge to meet unprecedented requirements beyond the capabilities of the past generations. The NG will not only be used for human interaction but also will be implemented in-vehicle communication. Therefore, the 5G has to support:
- Connection density: to handle million of demands and links across the square kilometer.
- Continuous latency from end to end.
- The density of road traffic volume: several dozens of terabytes created each second per square km.
- Mobility and maximum data rate.
- Network efficiency and high network capacity.
Continuous improvement and the increase in the number of applications have led to the development of new usages, in particular, that of connected objects. Vehicular communications or V2X communications allow vehicles to communicate in real-time with their environment to enhance road control, traffic performance, and energy savings. Figure 6 illustrates the different modes of communication, grouped under the term V2X.
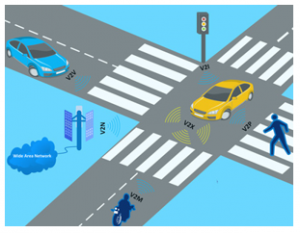
Figure 6: V2X communication modes
Embedded 5G will reform the experience of users in the transport sector (vehicles, subways, planes, trains, etc.), in particular by developing internet connectivity, which will make it possible to create an environment connected to the vehicle. V2X (Vehicle to Everything) communication technology will enable enormous changes the almost instantaneous exchange can be summarized as follows:
- Vehicle-to-vehicle (V2V): that permit inter-vehicle communication.
- Vehicle to infrastructure (V2I): it another type of communication that allows the vehicle to communicate with its surrounding like the communication between the roadside unit and the vehicle.
- Vehicle to pedestrian (V2P); that permits the exchange between the vehicles and the pedestrian into the road.
- Vehicle to motorcycle (V2M): Communication between vehicles and motorcycles to decrease the high rate of collisions and deaths in motorcycle crashes.
The concept of a connected vehicle is based on sensors that operate in line-of-sight such as radars, cameras, or laser remote sensing. The 5G will play a key role in making road transport more efficient and safe. Indeed, the automotive industry will require a more robust, stable, and low-latency network.
5.1. 5G V2X architecture
The structure of the fifth generation and vehicle to everything architecture is based on four network levels:
- 5G Access Network;
- Network Edge;
- 5G Core Network;
- Data Network.
The 5G Access Network is composed of a Next Generation Radio Access Network (NG-RAN) or/and a non 3GPP access network, which interconnects the 5G Core Network and the User Equipment (UE). Figure 6 shows the 5G V2X architecture:

Figure 7: 5G V2X architecture
5.2. Security issues in 5G V2X services: problems and risks
Even though 5G guidelines are as yet being defined it will confront a few difficulties the moment of its implementation. The new radio (NR) will require a steady improvement in security. In this specified situation, portable security and oversaw security services are one of the most escalated areas regarding advancement, to react to the difficulties in the field of digital security inborn to computerized change for the communication service providers and their clients. Moreover, 5G vows to reshape services and advance development by providing an expanded transfer speed, multitenant edge processing, and a few creative services, high-data transmission networks, and high-bandwidth connectivity to machine learning and artificial intelligence (AI). The insurance of services in 5G V2X requires ground-breaking, versatile, and coordinated security. The implementation of 5G V2X brings with it several security threats. The attack on the vehicle can lead to serious problems and can affect all sides of the security requirement
- Attacks on availability: the attacks that focus on the availability of data are the riskiest in V2X communication since they have a real impact on the basic circumstances of well-being. We can find attacks such as the jamming attack which is a radio interference attack that can be carried out across any communication based on wireless technology.
- Attack on data integrity: where the attacker intercepts the data circulated into the network. the attacker can launch attacks such as GPS spoofing or even replay attacks.
- Attack on confidentiality: as an important security requirement in V2X communication and all sent data in the V2X should be secured. An attack such as eavesdropping and location tracking are launched in the network to break through the V2X confidentiality
- Attack on authenticity: Assuring authenticity consists of the process to verify that nodes are granted access to the network according to their identities using certificates and digital signatures. Some threats that infringed this requirement are certificate replication where the nodes use replicated certificates that were added to the blacklist. Moreover, the Sybil attacks where one node (the attacker node) pretends to be many identities in the road network.
- Attack on the non-repudiation: Non-repudiation is concerned with the ID of the effective node that is performing a particular behavior.
The table below shows some attacks that impact the security requirement:
Table 1: Threats of security for 5G V2X
| Security Requirement | Attack | External | Internal |
| availability | Blackhole Grey hole | ü | × |
| Flooding | ü | × | |
| Jamming | × | × | |
| Coalition | ü | × | |
| data integrity | Messages Alteration | ü | × |
| False messages injection | ü | × | |
| Replay | ü | ü | |
| GPS Spoofing | × | × | |
| confidentiality | Eavesdropping | ü | × |
| Location tracking | × | × | |
| authenticity | Certificate replication | ü | ü |
| Sybil | ü | ü | |
| non-repudiation | Masquerading impersonation | ü | ü |
5.3. Security solutions for 5G V2X communication
Vehicular communication experiences numerous difficulties, hence, guaranteeing safe communication is viewed as a complicated process due to the lack of safety features in both empowering innovations of the vehicle to everything interchanges, an additive safety scheme is required to secure vehicle networks. The fields of security for 5G V2X was not deeply discussed. In this section, we will try to gather the mean full strategy that has been implemented to secure the 5G V2X communication. In [21], they proposed a lightweight and protected navigation system for VANET. Each vehicle implements a cryptographic and digital signature to manage the secured correspondence process from the vehicle to the roadside unit (RSU). The system dealt with the replay attack and the man-in-the-middle attack. Another solution was proposed by [22], consisting of a trusted and smart forwarding protocol using double ciphering for data packets and implemented strong verification schemes to gauge the trust of the node. In [23], they proposed a new technique depends on a one-time Identity-Based confirmed asymmetric gathering key consent to make cryptographic blend areas that oppose malicious Eavesdroppers. There are several types of research have proposed potential solutions for 5G from a machine learning (ML) perspective. In [24], the authors suggested a monitoring system employing a Support Vector Machine (SVM) learning algorithm to prevent the replay attack. Also in [25] an anti-jamming methodology for auxiliary users to choose the correspondence channel and mobility. Another researcher [26], based on deciding the arrangements of conceivable interfacing neighboring vehicles, and design the boundaries reserving the joint V2V network. In [27], they have introduced a trusted and standard secure signature solution for collecting plain text for vehicle system applications. The authors in [28], have suggested an algorithm for VANET that delivers authenticate delivered messages. He gave oversight roles to some specified nodes referred to as verification nodes. The authors in [29], suggested a model framework as an IDS based on compartmental attacks. it addressed various attacks in VANET such as the black hole, wormhole, and Sybil attacks.
6. Discussion
This article presents the state of the art on 5G technology applied to transportation to make roads safer. The security of 5G V2X communication presents a great challenge, for this reason, a security layer should be added to strengthen security, and the communication must respect the CIA principle (confidentiality, integrity, and availability):
- Confidentiality concerns the condition under which the vehicle user has the right to know what information is sent by the On-Board Unit (OBU) and for how long this information exists.
- Integrity to verify that all data has been transferred.
- Availability, to ensure that the protocols must remain operational even in the event of a failure, and remains fault-tolerant and stabilize once the failure has been eliminated.
In addition to two other aspects: privacy, this technique implies the preservation of the privacy of the driver and the vehicle. Also, the authentication which consists of ensuring that the intended recipient receives messages from a real sender.
As we have already presented, many applications and solutions have been implemented to ensure the security of 5G V2X communication to preserve and maintain the security of users. We can summarize these in three categories:
- Identity-Based Cryptography (IBC): The concept of IBC is a cryptographic scheme very suitable for devices with limited computing resources. It has been presented in many articles, to encrypt and effectively sign the messages interchanged.
- Behavior-Based: The concept is quite simple this solution is based on the behavior of the attached vehicles communicating in the network and the messages transmitted by the RSU.
- Machine Learning-Based (ML): This provides threat and attack prediction based on suspicious network activities and anomaly detection. The implementation of ML enables automation, adaptability, and enables efficient orchestration and dynamic provisioning for scaled network resources cognition and prediction of mobility
Last and not least the security of such a network can be done depending on four parameters:
- Arrangement: shows if the model is mounted on a flat or cluster network.
- Structure: specifies if the model has used structured, distributed, or hybrid.
- Purpose: specify if the goal of the system is an IDS, the implementation of a safe route, or the protection of the message content.
- Targeted attacks: specifies the attacks handled in the model.
7. Open issues and future orientations
Open issues and future perspectives were highlighted in this section. Securing the 5G V2X is a quite difficult challenge, For this reason, both security solutions and possible cures for identified and unidentified menaces rely on 5G-V2X implementation approaches. We can divide two approaches for 5G V2X. The first one the V2X is implemented with non-autonomous-5G (NA-5G), possible assaults on LTE-V2X are real and can leverage 5G-V2X capabilities. However, with the second implementation Autonomous-5G (A-5G), the attack window diminishes and safeguarding from threats can be augmented. Network deployment plays a critical factor in the 5G-V2X security policy decision. for this purpose, we have encountered the security needs at two levels in the 5G V2X field:
- Secure network caching at the network edge: Storing commonly demanded data in the cache at the edges of storage is an important and effective way to decrease the delay of V2X operations. Yet, it is difficult to maintain the privacy of stored and buffered content, from which opponents can determine which are the relevant services for a given target. To ensure network caching is secure, these key issues need to be resolved: knowing when and where to cache the desired data for a given vehicle, choosing trusted peripheral devices for data storage, and ensuring the confidentiality of buffered data when peripheral nodes are under attack. For this reason, cache placement could be well planned.
- Security-enhanced network slicing: The security and confidentiality of the grid segmentation have not yet gained a lot of attention. Therefore, it is essential to perform both authentication and authorization for a specified part of a network. For this reason, it is crucial to guarantee authentication with low latency to V2X services.
8. Conclusion and perspectives
Five generation and V2X services have expanded tremendously and have benefited our day-to-day lives. While providing a range of advantages to conductors and passengers on the road, 5G V2X’s connectivity has as well raised several concerns about security, trust, and privacy. In this article, we have presented the fifth generation and its characteristics. Besides, we have identified the key challenges that face this new generation. We also briefly outlined the main issues in securing the 5G V2X by determining its issues of reliability, safety, and privacy. Finally, we brought some open issues and future orientations in this field. This latter should have more attention in the future our perspective is to build a system that will be able of securing the communication between the vehicle and everything basing on the 5G connection.
- V. Jungnickel, K. Manolakis, W. Zirwas, B. Panzner, V. Braun, M. Lossow, M. Sternad, R. Apelfröjd, T. Svensson, “The role of small cells, coordinated multipoint, and massive MIMO in 5G,” IEEE Communications Magazine, 52(5), 44–51, 2014, doi:10.1109/MCOM.2014.6815892.
- E. Dahlman, G. Mildh, S. Parkvall, J. Peisa, J. Sachs, Y. Selén, “5G radio access,” Ericsson Review (English Edition), 91(1), 42–47, 2014.
- B. Manale, M. Tomader, “A survey of different storage methods for NGN mobile networks,” in Proceedings of 2019 International Conference of Computer Science and Renewable Energies, ICCSRE 2019, 2019, doi:10.1109/ICCSRE.2019.8807526.
- M. Iwamura, “NGMN view on 5G architecture,” IEEE Vehicular Technology Conference, 2015, 2015, doi:10.1109/VTCSpring.2015.7145953.
- T.L. Marzetta, “Noncooperative cellular wireless with unlimited numbers of base station antennas,” IEEE Transactions on Wireless Communications, 9(11), 3590–3600, 2010, doi:10.1109/TWC.2010.092810.091092.
- A. Gupta, R.K. Jha, “A Survey of 5G Network: Architecture and Emerging Technologies,” IEEE Access, 3, 1206–1232, 2015, doi:10.1109/ACCESS.2015.2461602.
- S. SEN, J. CLARK, J. TAPIADOR, Security Threats in Mobile Ad Hoc Networks, 2010, doi:10.1201/ebk1439819197-9.
- M.Á. Vázquez, L. Blanco, A. Pérez-Neira, “Sparse beamforming for mmWave spectrum sharing systems,” European Signal Processing Conference, 2018-Septe(1), 1517–1521, 2018, doi:10.23919/EUSIPCO.2018.8553148.
- E. Al Abbas, A.T. Mobashsher, A. Abbosh, “Polarization reconfigurable antenna for 5G cellular networks operating at millimeter waves,” Asia-Pacific Microwave Conference Proceedings, APMC, 772–774, 2017, doi:10.1109/APMC.2017.8251562.
- M. Tayyab, X. Gelabert, R. Jantti, “A simulation study on handover in LTE ultra-small cell deployment: A 5G challenge,” IEEE 5G World Forum, 5GWF 2019 – Conference Proceedings, 388–392, 2019, doi:10.1109/5GWF.2019.8911616.
- T. Varum, A. Ramos, J.N. Matos, “Planar microstrip series-fed array for 5G applications with beamforming capabilities,” 2018 IEEE MTT-S International Microwave Workshop Series on 5G Hardware and System Technologies, IMWS-5G 2018, 2018, doi:10.1109/IMWS-5G.2018.8484697.
- E. Dahlman, S. Parkvall, “NR – The new 5G radio-access technology,” IEEE Vehicular Technology Conference, 2018-June, 1–6, 2018, doi:10.1109/VTCSpring.2018.8417851.
- X. Lin, A. Grovlen, K. Werner, J. Li, R. Baldemair, J.F.T. Cheng, S. Parkvall, D.C. Larsson, H. Koorapaty, M. Frenne, S. Falahati, “5G New Radio: Unveiling the Essentials of the Next Generation Wireless Access Technology,” IEEE Communications Standards Magazine, 3(3), 30–37, 2019, doi:10.1109/MCOMSTD.001.1800036.
- O. Teyeb, G. Wikström, M. Stattin, T. Cheng, S. Faxér, H. Do, “Evolving LTE to Fit the 5G Future,” Ericsson Technology Review, 1–17, 2017.
- S. Parkvall, E. Dahlman, A. Furuskär, M. Frenne, “WIRELESS AND RADIO COMMUNICATION NR: The New 5G Radio Access Technology,” IEEE Communications Standards Magazine, 1(December), 24–30, 2017, doi:10.1109/MCOMSTD.2017.1700042.
- M.A. Abu-Rgheff, 5G Physical Layer Technologies, 2019, doi:10.1002/9781119525547.
- B. Badic, C. Drewes, I. Karls, M. Mueck, Rolling out 5G: Use cases, applications, and technology solutions, 2016, doi:10.1007/978-1-4842-1506-7.
- G. Liu, Y. Huang, F. Wang, J. Liu, Q. Wang, “5G features from operation perspective and fundamental performance validation by field trial,” China Communications, 15(11), 51–61, 2018, doi:10.1109/CC.2018.8543047.
- J. Ordonez-Lucena, P. Ameigeiras, Di. Lopez, J.J. Ramos-Munoz, J. Lorca, J. Folgueira, “Network Slicing for 5G with SDN/NFV: Concepts, Architectures, and Challenges,” IEEE Communications Magazine, 55(5), 80–87, 2017, doi:10.1109/MCOM.2017.1600935.
- R. Bruzgiene, L. Narbutaite, T. Adomkus, “MANET Network in Internet of Things System,” Ad Hoc Networks, (May 2017), 2017, doi:10.5772/66408.
- G. Li, M. Ma, C. Liu, Y. Shu, “A lightweight secure VANET-based navigation system,” 2015 IEEE Global Communications Conference, GLOBECOM 2015, 2015, doi:10.1109/GLOCOM.2014.7417462.
- S.K. Bhoi, P.M. Khilar, “A Road Selection Based Routing Protocol for Vehicular Ad Hoc Network,” Wireless Personal Communications, 83(4), 2463–2483, 2015, doi:10.1007/s11277-015-2540-x.
- L. Zhang, “OTIBAAGKA: A New Security Tool for Cryptographic Mix-Zone Establishment in Vehicular Ad Hoc Networks,” IEEE Transactions on Information Forensics and Security, 12(12), 2998–3010, 2017, doi:10.1109/TIFS.2017.2730479.
- Q.G. Fan, L. Wang, Y.N. Cai, Y.Q. Li, J. Chen, “VANET Routing Replay Attack Detection Research Based on SVM,” MATEC Web of Conferences, 63, 4–7, 2016, doi:10.1051/matecconf/20166305020.
- G. Han, L. Xiao, H.V. Poor, “Two-dimensional anti-jamming communication based on deep reinforcement learning,” ICASSP, IEEE International Conference on Acoustics, Speech and Signal Processing – Proceedings, 2087–2091, 2017, doi:10.1109/ICASSP.2017.7952524.
- L.T. Tan, R.Q. Hu, “Mobility-aware edge caching and computing in vehicle networks: A deep reinforcement learning,” IEEE Transactions on Vehicular Technology, 67(11), 10190–10203, 2018, doi:10.1109/TVT.2018.2867191.
- M.S.I. Mamun, A. Miyaji, H. Takada, “A multi-purpose group signature for vehicular network security,” Proceedings – 2014 International Conference on Network-Based Information Systems, NBiS 2014, 511–516, 2014, doi:10.1109/NBiS.2014.93.
- U. Khan, S. Agrawal, S. Silakari, “Detection of Malicious Nodes (DMN) in vehicular ad-hoc networks,” Procedia Computer Science, 46(Icict 2014), 965–972, 2015, doi:10.1016/j.procs.2015.01.006.
- H. Sedjelmaci, S.M. Senouci, “An accurate and efficient collaborative intrusion detection framework to secure vehicular networks,” Computers and Electrical Engineering, 43, 33–47, 2015, doi:10.1016/j.compeleceng.2015.02.018.
- Kazuki Iehira, Hiroyuki Inooue, "Detection Method and Mitigation of Server-Spoofing Attacks on SOME/IP at the Service Discovery Phase", Advances in Science, Technology and Engineering Systems Journal, vol. 11, no. 1, pp. 25–32, 2026. doi: 10.25046/aj110103
- Marlene Böhmer, Thorsten Herfet, "PerfVis+: From Timestamps to Insight through Integration of Visual and Statistical Analysis", Advances in Science, Technology and Engineering Systems Journal, vol. 10, no. 6, pp. 77–87, 2025. doi: 10.25046/aj100607
- Shaista Ashraf Farooqi, Aedah Abd Rahman, Amna Saad, "Federated Learning with Differential Privacy and Blockchain for Security and Privacy in IoMT A Theoretical Comparison and Review", Advances in Science, Technology and Engineering Systems Journal, vol. 10, no. 6, pp. 65–76, 2025. doi: 10.25046/aj100606
- Hiroshi Ito, Hideki Ohno, Hikaru Kitano, Shuichi Matsumoto, "Private 5G MIMO for Cable TV IP Broadcasting", Advances in Science, Technology and Engineering Systems Journal, vol. 10, no. 6, pp. 23–28, 2025. doi: 10.25046/aj100602
- Mahdi Madani, El-Bay Bourennane, Safwan El Assad, "Hardware and Secure Implementation of Enhanced ZUC Steam Cipher Based on Chaotic Dynamic S-Box", Advances in Science, Technology and Engineering Systems Journal, vol. 10, no. 1, pp. 37–47, 2025. doi: 10.25046/aj100105
- Viktor Denkovski, Irena Stojmenovska, Goce Gavrilov, Vladimir Radevski, Vladimir Trajkovik, "Exploring Current Challenges on Security and Privacy in an Operational eHealth Information System", Advances in Science, Technology and Engineering Systems Journal, vol. 9, no. 2, pp. 45–54, 2024. doi: 10.25046/aj090206
- Fazalur Rehman, Safwan Hashmi, "Enhancing Cloud Security: A Comprehensive Framework for Real-Time Detection, Analysis and Cyber Threat Intelligence Sharing", Advances in Science, Technology and Engineering Systems Journal, vol. 8, no. 6, pp. 107–119, 2023. doi: 10.25046/aj080612
- Sahar Fekry Abdel-Momen, Abdel Halim Abdelnaby Zekry, Ashraf Yehia Hassan, Wageeda Ibrahim Shaban, Mustafa Mohammed Shiple, "FPGA Implementation of 5G NR LDPC Codes", Advances in Science, Technology and Engineering Systems Journal, vol. 8, no. 4, pp. 91–100, 2023. doi: 10.25046/aj080411
- Abdulwahid Mohammed, Mohamed S. Elbakry, Hassan Mostafa, Abdelhady Abdelazim Ammar, "Doubling the Number of Connected Devices in Narrow-band Internet of Things while Maintaining System Performance: An STC-based Approach", Advances in Science, Technology and Engineering Systems Journal, vol. 8, no. 4, pp. 01–10, 2023. doi: 10.25046/aj080401
- Hiroki Iwanaga, "Photoluminescence Properties of Eu(III) Complexes with Two Different Phosphine Oxide Structures and Their Potential uses in Micro-LEDs, Security, and Sensing Devices: A Review", Advances in Science, Technology and Engineering Systems Journal, vol. 8, no. 3, pp. 154–160, 2023. doi: 10.25046/aj080317
- Mario Cuomo, Federica Massimi, Francesco Benedetto, "Detecting CTC Attack in IoMT Communications using Deep Learning Approach", Advances in Science, Technology and Engineering Systems Journal, vol. 8, no. 2, pp. 130–138, 2023. doi: 10.25046/aj080215
- Richard Romero Izurieta, Segundo Moisés Toapanta Toapanta, Luis Jhony Caucha Morales, María Mercedes Baño Hifóng, Eriannys Zharayth Gómez Díaz, Oscar Marcelo Zambrano Vizuete, Luis Enrique Mafla Gallegos, José Antonio Orizaga Trejo, "Prototype to Identify the Capacity in Cybersecurity Management for a Public Organization", Advances in Science, Technology and Engineering Systems Journal, vol. 8, no. 1, pp. 108–115, 2023. doi: 10.25046/aj080113
- Segundo Moisés Toapanta Toapanta, Rodrigo Humberto Del Pozo Durango, Luis Enrique Mafla Gallegos, Eriannys Zharayth Gómez Díaz, Yngrid Josefina Melo Quintana, Joan Noheli Miranda Jimenez, Ma. Roció Maciel Arellano, José Antonio Orizaga Trejo, "Prototype to Mitigate the Risks, Vulnerabilities and Threats of Information to Ensure Data Integrity", Advances in Science, Technology and Engineering Systems Journal, vol. 7, no. 6, pp. 139–150, 2022. doi: 10.25046/aj070614
- Tarek Nouioua, Ahmed Hafid Belbachir, "The Security of Information Systems and Image Processing Supported by the Quantum Computer: A review", Advances in Science, Technology and Engineering Systems Journal, vol. 7, no. 6, pp. 77–86, 2022. doi: 10.25046/aj070609
- Muhammad Musleh Uddin, Kazi Rafiqul Islam, Md. Monirul Kabir, "An Improved Model to Analyze the Impact of Cyber-Attacks on Power Systems", Advances in Science, Technology and Engineering Systems Journal, vol. 7, no. 5, pp. 27–34, 2022. doi: 10.25046/aj070504
- Kamil Halouzka, Ladislav Burita, Aneta Coufalikova, Pavel Kozak, Petr Františ, "A Comparison of Cyber Security Reports for 2020 of Central European Countries", Advances in Science, Technology and Engineering Systems Journal, vol. 7, no. 4, pp. 105–113, 2022. doi: 10.25046/aj070414
- Tiny du Toit, Hennie Kruger, Lynette Drevin, Nicolaas Maree, "Deep Learning Affective Computing to Elicit Sentiment Towards Information Security Policies", Advances in Science, Technology and Engineering Systems Journal, vol. 7, no. 3, pp. 152–160, 2022. doi: 10.25046/aj070317
- Afsah Sharmin, Farhat Anwar, S M A Motakabber, Aisha Hassan Abdalla Hashim, "A Secure Trust Aware ACO-Based WSN Routing Protocol for IoT", Advances in Science, Technology and Engineering Systems Journal, vol. 7, no. 3, pp. 95–105, 2022. doi: 10.25046/aj070311
- Khosro Salmani, Ken Barker, "Leakage-abuse Attacks Against Forward Private Searchable Symmetric Encryption", Advances in Science, Technology and Engineering Systems Journal, vol. 7, no. 2, pp. 156–170, 2022. doi: 10.25046/aj070216
- Kartit Zaid, Diouri Ouafaa, "Taxonomy of Security Techniques for Routing Protocols in Mobile Ad-hoc Networks", Advances in Science, Technology and Engineering Systems Journal, vol. 7, no. 2, pp. 25–31, 2022. doi: 10.25046/aj070203
- Janusz Gurzynski, Lukasz Kajda, Marcin Tarasiuk, Tomasz Samotyjak, Zbigniew Stachowicz, Slawomir Kownacki, "Control and Monitoring Systems in Medium Voltage Distribution Networks in Poland – Current Status and Directions of Development", Advances in Science, Technology and Engineering Systems Journal, vol. 6, no. 6, pp. 112–118, 2021. doi: 10.25046/aj060615
- Boris Kontsevoi, Sergei Terekhov, "TETRA™ Techniques to Assess and Manage the Software Technical Debt", Advances in Science, Technology and Engineering Systems Journal, vol. 6, no. 5, pp. 303–309, 2021. doi: 10.25046/aj060534
- Osaretin Eboya, Julia Binti Juremi, "iDRP Framework: An Intelligent Malware Exploration Framework for Big Data and Internet of Things (IoT) Ecosystem", Advances in Science, Technology and Engineering Systems Journal, vol. 6, no. 5, pp. 185–202, 2021. doi: 10.25046/aj060521
- Jianhua Yang, Lixin Wang, Yien Wang, "Enhance Student Learning Experience in Cybersecurity Education by Designing Hands-on Labs on Stepping-stone Intrusion Detection", Advances in Science, Technology and Engineering Systems Journal, vol. 6, no. 4, pp. 355–367, 2021. doi: 10.25046/aj060440
- Antonio Casquero Jiménez, Jorge Pérez Martínez, "Remote Patient Monitoring Systems with 5G Networks", Advances in Science, Technology and Engineering Systems Journal, vol. 6, no. 4, pp. 44–51, 2021. doi: 10.25046/aj060406
- Erika Quiroga, Karen Gutiérrez, "Smart Mobility: Opportunities and Challenges for Colombian Cities", Advances in Science, Technology and Engineering Systems Journal, vol. 6, no. 3, pp. 332–338, 2021. doi: 10.25046/aj060338
- Anh Nguyen-Duc, Manh-Viet Do, Quan Luong-Hong, Kiem Nguyen-Khac, Hoang Truong-Anh, "On the Combination of Static Analysis for Software Security Assessment – A Case Study of an Open-Source e-Government Project", Advances in Science, Technology and Engineering Systems Journal, vol. 6, no. 2, pp. 921–932, 2021. doi: 10.25046/aj0602105
- Bismark Tei Asare, Kester Quist-Aphetsi, Laurent Nana, "Node-Node Data Exchange in IoT Devices Using Twofish and DHE", Advances in Science, Technology and Engineering Systems Journal, vol. 6, no. 2, pp. 622–628, 2021. doi: 10.25046/aj060271
- Zarina Din, Dian Indrayani Jambari, Maryati Mohd Yusof, Jamaiah Yahaya, "Challenges in IoT Technology Adoption into Information System Security Management of Smart Cities: A Review", Advances in Science, Technology and Engineering Systems Journal, vol. 6, no. 2, pp. 99–112, 2021. doi: 10.25046/aj060213
- Saliha Assoul, Anass Rabii, Ounsa Roudiès, "An Operational Responsibility and Task Monitoring Method: A Data Breach Case Study", Advances in Science, Technology and Engineering Systems Journal, vol. 6, no. 1, pp. 1157–1163, 2021. doi: 10.25046/aj0601130
- Devika K N, Ramesh Bhakthavatchalu, "Modified Blockchain based Hardware Paradigm for Data Provenance in Academia", Advances in Science, Technology and Engineering Systems Journal, vol. 6, no. 1, pp. 66–77, 2021. doi: 10.25046/aj060108
- Zainatul Yushaniza Mohamed Yusoff, Mohamad Khairi Ishak, Kamal Ali Alezabi, "The Role of RFID in Green IoT: A Survey on Technologies, Challenges and a Way Forward", Advances in Science, Technology and Engineering Systems Journal, vol. 6, no. 1, pp. 17–35, 2021. doi: 10.25046/aj060103
- Pranay Bhardwaj, Carla Purdy, Nawar Obeidat, "A Novel Way to Design ADS-B using UML and TLA+ with Security as a Focus", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 6, pp. 1657–1665, 2020. doi: 10.25046/aj0506197
- Hesham Aly El Zouka, Mustafa Mohamed Hosni, "Time Granularity-based Privacy Protection for Cloud Metering Systems", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 6, pp. 1278–1285, 2020. doi: 10.25046/aj0506152
- Ala Din Trabelsi, Hend Marouane, Faouzi Zarai, "Priority-based Scheduling Algorithm for NOMA-integrated V2X", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 6, pp. 1225–1236, 2020. doi: 10.25046/aj0506146
- Mohamed Yasin Ibrahim Afifi, El-Sayed Soliman Ahmed Said, Abd El-Hady Abd El-Azim Ammar, "An Efficient Performance of OFDM-Shaped Symbol for 5G Green Communication Compared to FBMC", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 6, pp. 1163–1170, 2020. doi: 10.25046/aj0506140
- Abdulla Obaid Al Zaabi, Chan Yeob Yeun, Ernesto Damiani, Gaemyoung, "An Enhanced Conceptual Security Model for Autonomous Vehicles", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 6, pp. 853–864, 2020. doi: 10.25046/aj0506102
- Jim Scheibmeir, Yashwant Malaiya, "Multi-Model Security and Social Media Analytics of the Digital Twin", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 6, pp. 323–330, 2020. doi: 10.25046/aj050639
- Gautama Wijaya, Nico Surantha, "Multi-layered Security Design and Evaluation for Cloud-based Web Application: Case Study of Human Resource Management System", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 5, pp. 674–679, 2020. doi: 10.25046/aj050583
- Mika Karjalainen, Tero Kokkonen, "Review of Pedagogical Principles of Cyber Security Exercises", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 5, pp. 592–600, 2020. doi: 10.25046/aj050572
- Liana Khamis Qabajeh, Mohammad Moustafa Qabajeh, "Detailed Security Evaluation of ARANz, ARAN and AODV Protocols", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 5, pp. 176–192, 2020. doi: 10.25046/aj050523
- Pham Minh Nam, Phu Tran Tin, "Analysis of Security-Reliability Trade-off for Multi-hop Cognitive Relaying Protocol with TAS/SC Technique", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 5, pp. 54–62, 2020. doi: 10.25046/aj050508
- Adamu Abdullahi Garba, Maheyzah Muhamad Siraj, Siti Hajar Othman, "An Explanatory Review on Cybersecurity Capability Maturity Models", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 4, pp. 762–769, 2020. doi: 10.25046/aj050490
- Vu Nguyen Hoa Hong, Luong Tuan Anh, "Development Trends of Smart Cities in the Future – Potential Security Risks and Responsive Solutions", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 4, pp. 548–556, 2020. doi: 10.25046/aj050465
- Maximo Giovani Tanzado Espinoza, Joseline Roxana Neira Melendrez, Luis Antonio Neira Clemente, "A Survey and an IoT Cybersecurity Recommendation for Public and Private Hospitals in Ecuador", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 3, pp. 518–528, 2020. doi: 10.25046/aj050364
- Mainar Swari Mahardika, Achmad Nizar Hidayanto, Putu Agya Paramartha, Louis Dwysevrey Ompusunggu, Rahmatul Mahdalina, Farid Affan, "Measurement of Employee Awareness Levels for Information Security at the Center of Analysis and Information Services Judicial Commission Republic of Indonesia", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 3, pp. 501–509, 2020. doi: 10.25046/aj050362
- Abdelhafid Es-Saqy, Maryam Abata, Mohammed Fattah, Said Mazer, Mahmoud Mehdi, Moulhime El Bekkali, Catherine Algani, "5G mm-wave Band pHEMT VCO with Ultralow PN", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 3, pp. 487–492, 2020. doi: 10.25046/aj050360
- Suchitra Abel, Yenchih Tang, Jake Singh, Ethan Paek, "Applications of Causal Modeling in Cybersecurity: An Exploratory Approach", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 3, pp. 380–387, 2020. doi: 10.25046/aj050349
- Ayyoub El Berbri, Adil Saadi, Seddik Bri, "Design and Optimization of Dual-Band Branch-Line Coupler with Stepped-Impedance-Stub for 5G Applications", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 3, pp. 355–360, 2020. doi: 10.25046/aj050346
- A B Manju, Sumathy Subramanian, "Evolution of Privacy Preservation Models in Location-Based Services", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 3, pp. 82–92, 2020. doi: 10.25046/aj050311
- Gillala Rekha, Shaveta Malik, Amit Kumar Tyagi, Meghna Manoj Nair, "Intrusion Detection in Cyber Security: Role of Machine Learning and Data Mining in Cyber Security", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 3, pp. 72–81, 2020. doi: 10.25046/aj050310
- Segundo Moisés Toapanta Toapanta, Daniela Monserrate Moreira Gamboa, Luis Enrique Mafla Gallegos, "Analysis of the Blockchain for Adoption in Electronic Commerce Management in Ecuador", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 2, pp. 762–768, 2020. doi: 10.25046/aj050295
- Segundo Moisés Toapanta Toapanta, Andrés Aurelio García Henriquez, Luis Enrique Mafla Gallegos, "Analysis of Vulnerabilities, Risks and Threats in the Process of Quota Allocation for the State University of Ecuador", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 2, pp. 673–682, 2020. doi: 10.25046/aj050283
- Lylia Alouache, Mohamed Maachaoui, Rachid Chelouah, "Securing Hybrid SDN-based Geographic Routing Protocol using a Distributed Trust Model", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 2, pp. 567–577, 2020. doi: 10.25046/aj050271
- Segundo Moisés Toapanta Toapanta, José David López Cobeña, Luis Enrique Mafla Gallegos, "Analysis of Cyberattacks in Public Organizations in Latin America", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 2, pp. 116–125, 2020. doi: 10.25046/aj050215
- Karim El bouchti, Soumia Ziti, Fouzia Omary, Nassim Kharmoum, "New Solution Implementation to Protect Encryption Keys Inside the Database Management System", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 2, pp. 87–94, 2020. doi: 10.25046/aj050211
- José Alomía-Lucero, Jorge Castro-Bedriñana, Doris Chirinos-Peinado, "Rooftop Urban Agriculture Model with Two Tomato Varieties (Lycopersicum esculentum Mill) and Toppings in the High Jungle – Peru", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 1, pp. 446–450, 2020. doi: 10.25046/aj050157
- Amit Kumar Tyagi, A. Mohan Krishna, Shaveta Malik, Meghna Manoj Nair, Sreenath Niladhuri, "Trust and Reputation Mechanisms in Vehicular Ad-Hoc Networks: A Systematic Review", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 1, pp. 387–402, 2020. doi: 10.25046/aj050150
- Amine Kardi, Rachid Zagrouba, "Attacks classification and security mechanisms in Wireless Sensor Networks", Advances in Science, Technology and Engineering Systems Journal, vol. 4, no. 6, pp. 229–243, 2019. doi: 10.25046/aj040630
- Evan Hurwitz, Chigozie Orji, "Multi Biometric Thermal Face Recognition Using FWT and LDA Feature Extraction Methods with RBM DBN and FFNN Classifier Algorithms", Advances in Science, Technology and Engineering Systems Journal, vol. 4, no. 6, pp. 67–90, 2019. doi: 10.25046/aj040609
- Allae Erraissi, Abdessamad Belangour, "A Big Data Security Layer Meta-Model Proposition", Advances in Science, Technology and Engineering Systems Journal, vol. 4, no. 5, pp. 409–418, 2019. doi: 10.25046/aj040553
- Segundo Moisés Toapanta Toapanta, Steven Xavier Romo Sañicela, Danny Wilfrido Barona Valencia, Luis Enrique Mafla Gallegos, "Analysis of Information Security for a Voting Process for Sectional Governments in Ecuador", Advances in Science, Technology and Engineering Systems Journal, vol. 4, no. 5, pp. 352–359, 2019. doi: 10.25046/aj040546
- Alghamdi Abdullah, Mohammed Thanoon, Anwar Alsulami, "Toward a Smart Campus Using IoT: Framework for Safety and Security System on a University Campus", Advances in Science, Technology and Engineering Systems Journal, vol. 4, no. 5, pp. 97–103, 2019. doi: 10.25046/aj040512
- Segundo Moisés Toapanta Toapanta, Allan Fabricio German Diaz, Darío Fernando Huilcapi Subia, Luis Enrique Mafla Gallegos, "Proposal for a Security Model for a Popular Voting System Process in Latin America", Advances in Science, Technology and Engineering Systems Journal, vol. 4, no. 5, pp. 53–60, 2019. doi: 10.25046/aj040507
- Sanae El Hassani, Hind El Hassani, Noureddine Boutammachte, "Overview on 5G Radio Frequency Energy Harvesting", Advances in Science, Technology and Engineering Systems Journal, vol. 4, no. 4, pp. 328–346, 2019. doi: 10.25046/aj040442
- Segundo Moisés Toapanta Toapanta, Gabriel Enrique Valenzuela Ramos, Félix Gustavo Mendoza Quimi, Luis Enrique Mafla Gallegos, "Prototype of a Security Architecture for a System of Electronic Voting for the Ecuador", Advances in Science, Technology and Engineering Systems Journal, vol. 4, no. 4, pp. 292–299, 2019. doi: 10.25046/aj040437
- Jongsin Kim, Yonggil Choi, Younghoon Oh, "The Study of PSi & PSo Algorithm for Reducing Power of the Mobile Communication Network", Advances in Science, Technology and Engineering Systems Journal, vol. 4, no. 4, pp. 47–50, 2019. doi: 10.25046/aj040406
- Segundo Moisés Toapanta Toapanta, Andrés Javier Bravo Jácome, Maximo Giovanny Tandazo Espinoza, Luis Enrique Mafla Gallegos, "An Immutable Algorithm Approach to Improve the Information Security of a Process for a Public Organization of Ecuador", Advances in Science, Technology and Engineering Systems Journal, vol. 4, no. 3, pp. 25–30, 2019. doi: 10.25046/aj040304
- Robert M. Beswick, "Computer Security as an Engineering Practice: A System Engineering Discussion", Advances in Science, Technology and Engineering Systems Journal, vol. 4, no. 2, pp. 357–369, 2019. doi: 10.25046/aj040245
- Binwei Wu, Lu Ge, Jie Zeng, Xiangyun Zheng, Youxi Tang, Xin Su, "An Innovative EPC Architecture based on Not Only Stack for beyond 5G Mobile Networks", Advances in Science, Technology and Engineering Systems Journal, vol. 4, no. 2, pp. 319–332, 2019. doi: 10.25046/aj040241
- James Robert Pogge, Stephen lucien Scott, "Enabling the Edge – A method for dynamic virtualizable connections for 5G deployments", Advances in Science, Technology and Engineering Systems Journal, vol. 4, no. 2, pp. 270–279, 2019. doi: 10.25046/aj040235
- Evgenia Kapassa, Marios Touloupou, Panagiotis Stavrianos, Georgios Xylouris, Dimosthenis Kyriazis, "Managing and Optimizing Quality of Service in 5G Environments Across the Complete SLA Lifecycle", Advances in Science, Technology and Engineering Systems Journal, vol. 4, no. 1, pp. 329–342, 2019. doi: 10.25046/aj040132
- Shruthi Narayanaswamy, Anitha Vijaya Kumar, "Application Layer Security Authentication Protocols for the Internet of Things: A Survey", Advances in Science, Technology and Engineering Systems Journal, vol. 4, no. 1, pp. 317–328, 2019. doi: 10.25046/aj040131
- Lin Dong, Akira Rinoshika, "Analysis and Methods on The Framework and Security Issues for Connected Vehicle Cloud", Advances in Science, Technology and Engineering Systems Journal, vol. 3, no. 6, pp. 105–110, 2018. doi: 10.25046/aj030611
- Ola Surakhi, Mohammad Khanafseh, Yasser Jaffal, "An enhanced Biometric-based Face Recognition System using Genetic and CRO Algorithms", Advances in Science, Technology and Engineering Systems Journal, vol. 3, no. 3, pp. 116–124, 2018. doi: 10.25046/aj030316
- Abul Kalam Azad, Md. Yamin Mollah, "EAES: Extended Advanced Encryption Standard with Extended Security", Advances in Science, Technology and Engineering Systems Journal, vol. 3, no. 3, pp. 51–56, 2018. doi: 10.25046/aj030307
- Dhiman Chowdhury, Mrinmoy Sarkar, Mohammad Zakaria Haider, "A Cyber-Vigilance System for Anti-Terrorist Drives Based on an Unmanned Aerial Vehicular Networking Signal Jammer for Specific Territorial Security", Advances in Science, Technology and Engineering Systems Journal, vol. 3, no. 3, pp. 43–50, 2018. doi: 10.25046/aj030306
- Nicola Fabiano, "The Internet of Things ecosystem: the blockchain and data protection issues", Advances in Science, Technology and Engineering Systems Journal, vol. 3, no. 2, pp. 1–7, 2018. doi: 10.25046/aj030201
- Asma Meddeb, Hajer Jmii, Souad Chebbi, "Security Analysis and the Contribution of UPFC for Improving Voltage Stability", Advances in Science, Technology and Engineering Systems Journal, vol. 3, no. 1, pp. 404–411, 2018. doi: 10.25046/aj030149
- Luca Dariz, Gianpiero Costantino, Massimiliano Ruggeri, Fabio Martinelli, "A Joint Safety and Security Analysis of message protection for CAN bus protocol", Advances in Science, Technology and Engineering Systems Journal, vol. 3, no. 1, pp. 384–393, 2018. doi: 10.25046/aj030147
- Anass Sedrati, Abdellatif Mezrioui, "A Survey of Security Challenges in Internet of Things", Advances in Science, Technology and Engineering Systems Journal, vol. 3, no. 1, pp. 274–280, 2018. doi: 10.25046/aj030133
- Hiroaki Anada, Seiko Arita, "Short CCA-Secure Attribute-Based Encryption", Advances in Science, Technology and Engineering Systems Journal, vol. 3, no. 1, pp. 261–273, 2018. doi: 10.25046/aj030132
- Muhammad Usman Sheikh, Jukka Lempiainen, "Analysis of Outdoor and Indoor Propagation at 15 GHz and Millimeter Wave Frequencies in Microcellular Environment", Advances in Science, Technology and Engineering Systems Journal, vol. 3, no. 1, pp. 160–167, 2018. doi: 10.25046/aj030120
- Zeineb Zhioua, Rabea Ameur-Boulifa, Yves Roudier, "Framework for the Formal Specification and Verification of Security Guidelines", Advances in Science, Technology and Engineering Systems Journal, vol. 3, no. 1, pp. 38–48, 2018. doi: 10.25046/aj030106
- Himanshu Upadhyay, Hardik Gohel, Alexander Pons, Leo Lagos, "Virtual Memory Introspection Framework for Cyber Threat Detection in Virtual Environment", Advances in Science, Technology and Engineering Systems Journal, vol. 3, no. 1, pp. 25–29, 2018. doi: 10.25046/aj030104
- Susan Gottschlich, "A Taxonomy for Enhancing Usability, Flexibility, and Security of User Authentication", Advances in Science, Technology and Engineering Systems Journal, vol. 2, no. 6, pp. 225–235, 2017. doi: 10.25046/aj020627
- Mohamed El Beqqal, Mostafa Azizi, "Review on security issues in RFID systems", Advances in Science, Technology and Engineering Systems Journal, vol. 2, no. 6, pp. 194–202, 2017. doi: 10.25046/aj020624
- Mbunwe Muncho Josephine, "Design and Construction of a remote control switching device for household appliances application", Advances in Science, Technology and Engineering Systems Journal, vol. 2, no. 4, pp. 154–164, 2017. doi: 10.25046/aj020421
- Saleh Mohamed Alnaeli, Melissa Sarnowski, Md Sayedul Aman, Ahmed Abdelgawad, Kumar Yelamarthi, "Source Code Vulnerabilities in IoT Software Systems", Advances in Science, Technology and Engineering Systems Journal, vol. 2, no. 3, pp. 1502–1507, 2017. doi: 10.25046/aj0203188
- Ali Shuja Siddiqui, Yutian Gui, Jim Plusquellic, Fareena Saqib, "A Secure Communication Framework for ECUs", Advances in Science, Technology and Engineering Systems Journal, vol. 2, no. 3, pp. 1307–1313, 2017. doi: 10.25046/aj0203165
- Daniel Fraunholz, Marc Zimmermann, Hans Dieter Schotten, "Towards Deployment Strategies for Deception Systems", Advances in Science, Technology and Engineering Systems Journal, vol. 2, no. 3, pp. 1272–1279, 2017. doi: 10.25046/aj0203161
- Davar Pishva, "IoT: Their Conveniences, Security Challenges and Possible Solutions", Advances in Science, Technology and Engineering Systems Journal, vol. 2, no. 3, pp. 1211–1217, 2017. doi: 10.25046/aj0203153
- Sarra Alqahtani, Rose Gamble, "Verifying the Detection Results of Impersonation Attacks in Service Clouds", Advances in Science, Technology and Engineering Systems Journal, vol. 2, no. 3, pp. 449–459, 2017. doi: 10.25046/aj020358
- Shaddrack Yaw Nusenu, "Directional Antenna Modulation Technique using A Two-Element Frequency Diverse Array", Advances in Science, Technology and Engineering Systems Journal, vol. 2, no. 3, pp. 227–232, 2017. doi: 10.25046/aj020331
- Raid Khalid Hussein, Ahmed Alenezi, Hany F. Atlam, Mohammed Q Mohammed, Robert J. Walters, Gary B. Wills, "Toward Confirming a Framework for Securing the Virtual Machine Image in Cloud Computing", Advances in Science, Technology and Engineering Systems Journal, vol. 2, no. 4, pp. 44–50, 2017. doi: 10.25046/aj020406
- Fatna Elmendili, Nisrine Maqran, Younes El Bouzekri El Idrissi, Habiba Chaoui, "A security approach based on honeypots: Protecting Online Social network from malicious profiles", Advances in Science, Technology and Engineering Systems Journal, vol. 2, no. 3, pp. 198–204, 2017. doi: 10.25046/aj020326
- Fabian Bustamante, Walter Fuertes, Paul Diaz, Theofilos Toulqueridis, "Methodology for Management of Information Security in Industrial Control Systems: A Proof of Concept aligned with Enterprise Objectives.", Advances in Science, Technology and Engineering Systems Journal, vol. 2, no. 3, pp. 88–99, 2017. doi: 10.25046/aj020313
- Selina Kolokytha, Alexander Flisch, Thomas Lüthi, Mathieu Plamondon, Adrian Schwaninger, Wicher Vasser, Diana Hardmeier, Marius Costin, Caroline Vienne, Frank Sukowski, Ulf Hassler, Irène Dorion, Najib Gadi, Serge Maitrejean, Abraham Marciano, Andrea Canonica, Eric Rochat, Ger Koomen, Micha Slegt, "Improving customs’ border control by creating a reference database of cargo inspection X-ray images", Advances in Science, Technology and Engineering Systems Journal, vol. 2, no. 3, pp. 60–66, 2017. doi: 10.25046/aj020309
- Casimer DeCusatis, Piradon Liengtiraphan, Anthony Sager, "Zero Trust Cloud Networks using Transport Access Control and High Availability Optical Bypass Switching", Advances in Science, Technology and Engineering Systems Journal, vol. 2, no. 3, pp. 30–35, 2017. doi: 10.25046/aj020305
- Chien Hua Wu, Ruey Kei Chiu, "Implementation a Secure Electronic Medical Records Exchange System Based on S/MIME", Advances in Science, Technology and Engineering Systems Journal, vol. 2, no. 1, pp. 172–176, 2017. doi: 10.25046/aj020120
