TETRA™ Techniques to Assess and Manage the Software Technical Debt
Volume 6, Issue 5, Page No 303–309, 2021
Adv. Sci. Technol. Eng. Syst. J. 6(5), 303–309 (2021);
 DOI: 10.25046/aj060534
DOI: 10.25046/aj060534
Keywords: Architecture, Bug, Business Logic, Data Quality, Fixing, Metrics, Measurements, Open Source, Performance Quality, Quality Assurance, Security, Software, Source Code, Technical Debt, Test, Testing, Usability
The paper examines the company’s proprietary means for determining the quality of a software product and measuring its technical debt. The paper’s authors explain how a software product’s quality is directly correlated with the amount of varying technical debts that the end-users receive. All debts can be paid, and technical debt is no exception: one can use various parameters, techniques, and dimensions to effectively measure and optimize the quality of a software product. The authors share information about the company’s proprietary method to technical debt management, which is done via the Technical dEbT Reduction plAtform, otherwise known as TETRA™. They give details about the assessment’s major dimensions, tools, and measurement parameters.
1. Introduction
Whether you’ve been a part of the software development industry for decades or just a few years, you’ve probably had to explain software quality to your clients. Everybody talks about software quality, but it’s understood differently from person to person. Some define quality as the level of client satisfaction, while others say it’s just about meeting the customer’s requirements. And in the tech world, it’s more about the software being free of any defects. We find the latter to be more realistic; however, it can raise even more concerns. At Intetics, we decided to clear up any understandings by carrying out intensive research: we aimed to determine what the quality of a software product is and how it can be managed efficiently. Throughout our investigations, we discovered that a software product’s quality is directly correlated to the product’s amount of varying technical debts that are passed on to end-users.
Best practices within the software development industry state that technical debt is any code added now that will take more work to fix later on. This kind of code is usually added to achieve rapid gains. The source code is one of the most important aspects of software. After all, the higher the number of problems within the source code, the more redevelopment is needed [1]. That’s how the software development industry understands technical debt – and we agree. However, after dealing with technical debt for many years, we started to think about it differently. After thorough examination, we came to the conclusion that technical debt is “a combined product non-compliance with technical guidelines and business objectives that negatively impact business results.”
Technical debt can be further divided into three categories: intentional, unavoidable, and unintentional.
- Intentional tech debt: As a business strategy, this kind of debt is knowingly taken on. If intentional debt is kept at bay, it’s acceptable.
- Unavoidable tech debt: This kind compiles as a result of external factors, such as when you need to adapt your software after a third-party system upgrade.
- Unintentional tech debt: It stems from negligence. It might happen if several developers are simultaneously working on one solution and one error is layered over another.
There are also various kinds of tech debt types based on the debt’s cause. Some causes include people debt, automation test debt, documentation debt, and requirement debt, among others [2].
A growing volume of technical debt in the project is usually a consequence of cutting corners during the project’s early stages. It can stem from minor defects in the codebase, environment setup, documentation, or chosen third-party software. And as the impact of these early errors grows, refactoring is necessary – likely rewritten or adjusted to ease further development and maintenance. The development team has to work with tech debt while the software is already developed, released, and being actively used. And if the tech debt is not addressed in time, it will gradually build up, threatening to take down the whole software product.
The costs of technical debt can be quite significant; the cost of technical debt for an average application with 300,000 lines is just over $1 million, according to a report from CAST software. What’s more, the repercussions can go beyond high costs. Take, for instance, an NHS glitch in 2018 – in this case, over 10,000 patients were at risk of being given the wrong medication.
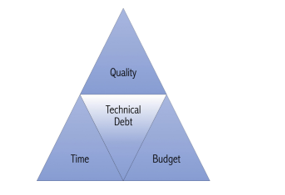
For any software product, it is natural to accumulate some amount of technical debt in the development process. Therefore, it makes academic and practical sense to manage tech debt. Various reviewed sources suggest that technical debt should be managed within the Agile Triangle, where there are three different dimensions – budget, time, and scope [3] – conflicting since it is not feasible to develop high-quality software with a low budget in a short time. So, as shown in Figure 1, if we are focused on one corner, we are going to weaken the other two.
ª Agile Triangle figure is taken from source [3].
But there are also more specific approaches that highlight the following steps:
- Identifying;
- Measuring;
- Prioritizing;
- Preventing;
- Monitoring;
- Repaying;
- Representing/Documenting;
- Communicating [4].
However, there is no commonly accepted theory of technical debt identification. Yet, technical debt is present in any real project – whether or not the developers recognize it as its own entity. That had encouraged us to propose our own different model.
While developing the model, we spent thousands of hours investigating and defining crucial aspects of software product quality that allow us to get a better perspective and measurement of technical debt. We used these dimensions to form the foundation of our platform for software quality assessment: TETRA™ (Technical dEbT Reduction plAtform). And why did we name it TETRA™? Technical debt is akin to tiny TETRA™ fish with thousands of species. That might be like small and insignificant at first glance trade-offs. Even though these “locally beautiful” quick solutions are easy to implement, they aren’t the ideal solution overall. As technical debt compiles, you’ll have to pay “interest” – in other words, more challenging maintainability, a less enjoyable user experience, worse productivity across your development team, and increased costs overall. We cram all those fish into one fishbowl: the TETRA™ platform. So, how do we decide what matters in software products? Is it possible to assess both the business and technical sides?
We measure and assess both sides using a specific set of tools and techniques, chosen based on original research from Intetics, best practice analysis, and expertise gained throughout multiple projects. The results enable us to calculate a software product’s overall technical debt and its specific parameters. To get the big picture, we use eight dimensions to assess the product; each dimension is judged on a five-point scale. This enables uniform results and allows summary assessments to be obtained – for the product itself and for each dimension. Ranges of values were set for each metric – experimental and directly calculated, which acted as a scoring system. The final product quality assessment calculation was done via a weighted parameters system. The parameters determined the roles that each dimension would play in the overall score.
The final assessment is given within a table containing numbers and indices for each metric. The most advantageous part of using the TETRA™ methodology is that indices are introduced, rather than exact numbers. Thus, further investigation can be carried out based on the analysis of the TETRA™ Index, Metric Index, and Dimension Index.
Every value was given a letter score and color. The highest letter grade is A, which means that the parameter’s component had no technical debt. The lowest, E, flagged the presence of critical problems that must be rectified before the product is worked on further.
An example of the assessment is shown in Figure 2. To see the big picture, we assess the product based on the following eight dimensions.
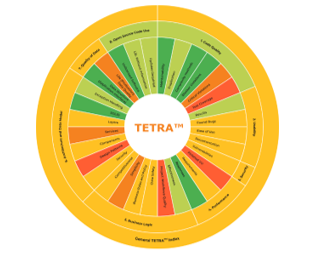 Figure 2: Example of TETRA™ assessment report.
Figure 2: Example of TETRA™ assessment report.
ª Note. Own development.
2. TETRA™ Dimensions
2.1 Dimension 1
Source code quality includes not only the completeness and correctness of the required functionality’s implementation but also the ease of support and its modification [5]. It is evaluated by these parameters:
- Cyclomatic complexityof the code is a metric on which the complexity of the code maintenance directly depends and is calculated as the number of independent paths in the code.
- Duplicationsis one of the main characteristics that reflects how easy it will be in the future (or present) to make changes to the code. The fewer duplicates there are, the easier it will be to live with this code.
- The code coverage level is read as the ratio of the number of code points covered by the unit tests to the number of all existing ones.
- Rules complianceis the set of rules for compliance and conventions that verify the basic design principles for source code that’s shared by the development team.
- Maintainability indexis a software metric that measures how it`s easy to maintain the source code.
 Figure 3: Source code quality assessment summary
Figure 3: Source code quality assessment summary
Figure 3 shows the Summary Source Code Assessment results where the most pressing issues are related to the unit test coverage and critical rules compliance violations.
2.2 Dimension 2
Usability, UI & Documentation covers the assessment of a software product’s usability, UI, and documentation, as the name suggests. This process includes a checklist and expert assessment, which address learnability, memorability, likeability, error tolerability, and efficiency metrics [6]. In order to give an accurate assessment, we use Usabilla, Browser Shots, W3C Markup Validation Service, and other tools. A usability assessment example is shown in Figure 4, where you can see that the usability quality level is good.
 Figure 4: Usability assessment summary.
Figure 4: Usability assessment summary.
2.3 Dimension 3
Security delves into product vulnerabilities related to BID, CERT, OSVDB, CVE, CWE, and OWASP [7]. We use automated and manual approaches within the security assessment, using tools like OWASP ZAP, Burp Suite, and Nessus [8, 9]. An example of the security assessment is shown in Figure 5; 8 vulnerabilities were found there, giving the software a medium security quality level.
 Figure 5: Security assessment summary
Figure 5: Security assessment summary
 Figure 6: Performance assessment summary
Figure 6: Performance assessment summary
2.4 Dimension 4
Performance assessment is the evaluation of whether the product meets the customer’s requirements. We perform the assessment through load testing and by simulating the activity of virtual users. We use tools like LoadUI Pro, WebLoad, JMeter, and LoadRunner to assess certain performance parameters, including peak and average response times, concurrent users, and a separate set of server-state assessment parameters. An example of the performance assessment is shown in Figure 6. The most impact on the final evaluation was made by the fallen virtual users.
2.5 Dimension 5
Business logic assessment determines whether software aligns with necessary business processes. This kind of assessment considers feedback from various focus groups, including customers, end-users, community, management, etc. The business logic assessment relies on six main metrics: data safety, project workflow quality, effectiveness, simplicity, business rules and policy, and competitiveness. An example of the business logic assessment is shown in Figure 7.
 Figure 7: Business logic assessment summary.
Figure 7: Business logic assessment summary.
2.6 Dimension 6
Architecture quality assessment contains an expert’s conclusion regarding the data model and core structure of the software. During the assessment’s administration, we analyze services, layers, exception handling, design patterns, infrastructure and recycling components, and more [10, 11].
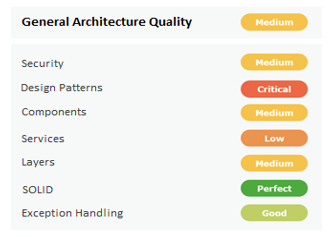 Figure 8: Architecture assessment summary.
Figure 8: Architecture assessment summary.
2.7 Dimension 7
Data quality encompasses a product’s resistance to bad data, how it handles exceptions, and its bad data preventative measures. We base the assessment on metrics like completeness, timeliness, validity, currency, accuracy, consistency, and accessibility. To ensure the assessment’s accuracy, we use manual testing and the Talend Open Studio. An example of the data quality assessment is shown in Figure 9. In this dimension, both metrics were assessed at the medium level.
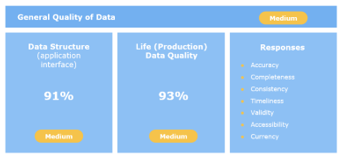 Figure 9: Data quality assessment summary.
Figure 9: Data quality assessment summary.
2.8 Dimension 8
Open-source code use assessments find any open-source components contained in the software product. We included this dimension to pinpoint any operational, legal, security, or copyright issues that could occur from using open-source components. Inside the report, we give a list of all copyrights, open-source code, and licenses used in the software product. Furthermore, we analyze the software’s open-source version. The assessment is done with Black Duck, Palamida, and other tools. See Figure 10 for an example of an assessment of open-source code. The biggest problems were caused by the inclusion of unlicensed software.
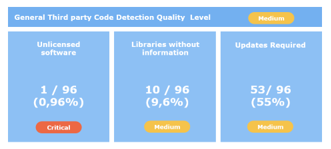 Figure 10: Open source code use assessment summary.
Figure 10: Open source code use assessment summary.
By using this method of analyzing and measuring technical debt, we create the final report that describes each weakness and determines the product’s quality.
Because these dimensions significantly impact business needs, they must be communicated to stakeholders. Each component can be checked independently, and some might not be applicable to certain products. Separating technical debt dimensions necessitates manual action and review from a personal expert to be factored into the final scoring. We consider this to be less of a problem than not estimating a software product’s technical debt.
3. Advantages of TETRA™
Using TETRA™’s framework to expand the concept of technical debt brings benefits to developers and all stakeholders. By understanding the total technical debt, the following can be achieved:
- Managers are able to observe whether project management is effective. They can identify bottlenecks that are currently hindering the project’s development or could become a problem in the future.
- Designers and developers get an unbiased third-party report on project coherence and code quality.
- Investors who are presented with the TETRA™ evaluation can use it as an additional quantifiable justification for product investment.
- Product owners can use TETRA™’s evaluation to assess the effectiveness of fund allocation to various development teams. Thus, they can place priorities within product development areas or decide to conserve until the technical debt has been removed.
4. Limitations of TETRA™
However, TETRA™ is not a one-size-fits-all solution, nor is it a miracle. While it is a highly effective evaluation tool, it does have certain limitations, namely:
- While TETRA™ allows technical debt to be identified, it does not provide answers on how to minimize said debt. There will need to be further investigation into the causes of technical debt, and the management and development team must change their established practices.
- Because technical debt goes past quantifiable technical aspects of code quality (e.g., number of vulnerabilities/ defects per code volume), the process cannot be fully automated and needs subjective, expert assessment.
- In order to minimize technical debt, TETRA™ assessments will be required on a regular basis.
5. TETRA™ Use Case: E-Learning Platform
One of our EdTech clients wanted to innovate and revamp its e-learning platform with the goal of adding to its user base and improving its market value.
The companies target audience consists of students and graduates who are studying English and trying to improve their language skills. Most of the platform’s users are tech-savvy kids, teenagers, and young adults who are comfortable with modern technologies.
To ensure the platform was a good fit for their target audience, our client needed to measure its current technical capabilities and business efficiency before introducing new features.
The project contained about 120,000 lines of code and 7 logic sections/modules. 5 developers and 2 QA developed the platform for 2+ years. A wide array of tools and technologies were used, including Spring Boot, Angular, Java, MySQL, Git, Jenkins, and jQuery.
A profound platform assessment was required, so the client chose us for our extensive expertise; they requested that we carry out an unbiased analysis.
To meet the client’s needs, we applied the proprietary TETRA™ approach to their platform, analyzing all eight components outlined in Section 2. Each stage of the assessment concluded with a report about the product’s bottlenecks and pain points. The process took 2 months from start to finish.
Throughout the TETRA™ analysis, we found several areas that the client was satisfactory in, including their open-source code use and source code quality. However, there were also several areas that needed improvement: the platform had a medium security risk, as well as poor architectural, performance, and business logic elements.
See results in table the Final TETRA™ report below.
Table 1: The final TETRA™ report
| Metric | Assessment Result | Evaluation
Rank |
Score | Metric
Index |
Dimension Index | General TETRA™ Quality Index |
| TETRA™ Eight (8) Dimensions of Quality | С
|
|||||
| 1. Source Code Quality | B | |||||
| Unit Test Coverage | 0 | X < 40 | 5 | E | ||
| Critical Violations | 44 | 40 < X < 60 | 4 | D | ||
| Duplication | 4.30% | 4% < X < 5% | 2 | B | ||
| Maintainability index | 1.9% | 0 < X < 2.1 | 1 | A | ||
| Complexity Methods | 4.40% | 0 < X < 5% | 1 | A | ||
| Blocker Violations | 0 | X = 0 | 1 | A | ||
| 2. Usability, UI & Documentation | C | |||||
| Documentation | Failed: 9%, Failed weight: 15% |
Failed: 5% < X < 10% Weight: X < 20 | 3 | C | ||
| Found Bugs | Trivial: 4, Minor: 20, Major: 2 |
Major – Worst priority | 3 | C | ||
| Ease of Use | Score: 3 | X = 3 | 3 | C | ||
| UI Results | Failed: 8%, Failed weight: 10% |
Failed: 5% < X < 10% Weight: X < 20 | 2 | B | ||
| 3. Security | C | |||||
| Vulnerabilities | Trivial: 3, Medium: 4 |
Medium – Worst priority | 3 | C | ||
| 4. Performance | C | |||||
| Finished Virtual Users | 10% | < 85% | 5 | E | ||
| Customer Requirements | 85% | 80% < X < 90% | 3 | C | ||
| Responses | 100% | X = 100% | 1 | A | ||
| 5. Business Logic | C | |||||
| Project Workflows Quality | 23% | X < 25% | 5 | E | ||
| Simplicity | 30% | 25% < X < 50 % | 4 | D | ||
| Data Safety | 67% | 50% < X < 75% | 3 | C | ||
| Bussiness Rules and Policy | 57% | 50% < X < 75% | 3 | C | ||
| Competitiveness | 63% | 50% < X < 75% | 3 | C | ||
| Effectiveness | 80% | 75 % < X < 90% | 2 | B | ||
| 6. Architecture Quality | C | |||||
| Design Patterns | 25% | X < 30% | 5 | E | ||
| Services | 41% | 30% < X < 50% | 4 | D | ||
| Security | 65% | 50% < X < 70% | 3 | C | ||
| Components | 59% | 50% < X < 70% | 3 | C | ||
| Layers | 63% | 50% < X < 70% | 3 | C | ||
| Exception handling | 85% | 70% < X < 90% | 2 | B | ||
| SOLID | 98% | 95% < X | 1 | A | ||
| 7. Data Quality | C | |||||
| Real-slice (Production) Data Quality | 58 % | 50% < X < 60% | 4 | D | ||
| Requirements Data Quality | 96% | 95% < X | 1 | A | ||
| 8. Open Source Code Use | B | |||||
| Lib. Without information | 8% | 5% < X < 10% | 2 | B | ||
| Updates Required | 8% | 5% < X < 10% | 2 | B | ||
| Unlicensed software | 0% | X = 0% | 1 | A | ||
ª Note. Own development
6. Results
The final TETRA™ report is illustrated in the Table above, which demonstrates that the overall platform state was “Medium,” showing the value “C” of the TETRA™ Index. Simultaneously, a detailed results interpretation showed that functionality updates sometimes lead to software crashes.
By carrying out the analysis, we were able to give the client the bigger picture about their platform; they understood which areas needed enhancements and were able to avoid crashes resulting from future updates.
We provided the client with a detailed list of recommendations, which the client followed. As a result of the improvements, the platform’s user-base grew by 17.3%, and product redevelopment costs were cut by 22%.
7. Conclusion
TETRA™ isn’t just applicable for tech experts – it benefits everybody who works on a product. Testers and developers alike receive an unbiased assessment of their work, users get a well-performing, reliable product, and managers get a better idea of the product’s capacity. Furthermore, the processes used within the assessment encourages best practices from the team, thus increasing team proficiency – and thereby the product’s quality
TETRA™ gives proper business information to product owners and investors. Companies can get a fair analysis of their product and determine whether it’s ready to be launched. If the product already works as intended, the owners can get an estimate of its market value and efficiency. And regarding investors, TETRA™ enables them to better define the product’s market value, evaluate the state of the purchasable product, and determine potential investment risks for a transaction.
Throughout the development of TETRA™, we had the overall goal of quantitatively evaluating software product conditions and helping development teams get better results. If you don’t use comprehensive, standardized measurements, it isn’t possible to understand and manage the product’s quality. TETRA™ determines whether the needs of the investors, market, development teams, product owners, and users have been met. It allows you to efficiently take control of your project.
Conflict of Interest
The authors declare no conflict of interest.
Acknowledgment
Intetics vision of the outsourcing and custom software development industry involves heightened innovation brought to life through Intetics’ TETRA™ platform, as well as our proprietary Remote In-Sourcing® and Offshore Dedicated Team® models. Intetics is more than just software development; we aim to make an impact by sharing best practices with the global IT community and for different industries. The research was performed under the leadership of Boris Kontsevoi, President & CEO, and Sergei Terekhov, Director of Quality Assurance, based on the unique developed methodology for assessing technical debt.
- G. A. Campbell, P. P. Papapetrou, and O. Gaudin, “SonarQube in Action,” 1st Edition, Manning Publications, 392, 2013, ISBN-13: 9781617290954.
- N. S. R. Alves, L. F. Ribeiro, V. Caires, T. S. Mendes and R. O. Spínola, “Towards an Ontology of Terms on Technical Debt,” 2014 Sixth International Workshop on Managing Technical Debt, 1-7, 2014, doi: 10.1109/MTD.2014.9.
- P. Ciancarini, D. Russo, “The strategic technical debt management model: an empirical proposal,” In: V. Ivanov, A. Kruglov, S. Masyagin, A. Sillitti, G. Succi (eds) Open Source Systems, OSS 2020, IFIP Advances in Information and Communication Technology, 582, Springer, Cham, 131-140, 2020, doi: 10.1007/978-3-030-47240-5_13.
- J. Yli-Huumo, A. Maglyas, K. Smolander, “How do software development teams manage technical debt? – An empirical study,” The Journal of Systems and Software 120, 195-218, 2016, doi: 10.1016/j.jss.2016.05.018.
- A. Peixoto de Queirós, R. and A. Simões, and M. T. Pinto, “Code Generation, Analysis Tools, and Testing for Quality. Hershey,” PA: IGI Global, 288, 2019. doi: 10.4018/978-1-5225-7455-2.
- ISO/IEC 25063:2014, “Systems and software engineering — systems and software product quality requirements and evaluation (SQuaRE) — common industry format (CIF) for usability,” 1st Edition, ISO/TC 159/SC 4 Ergonomics of human-system interaction, 33, 2014.
- OWASP, “OWASP top 10 – 2017. The Ten Most Critical Web Application Security Risks,” OWASP Foundation, 25, 2017.
- CISQ, “List of Weaknesses Included in the CISQ Automated Source Code Quality Measures,” CISQ, 31, 2019.
- ISO/IEC 5055:2021, “Information technology — Software measurement — Software quality measurement — Automated source code quality measures,” 1st Edition, ISO/IEC JTC 1 Information technology, 235, 2021.
- Microsoft Patterns & Practices Team , “Microsoft Application Architecture Guide,” 2nd edition, Microsoft Press, 560, 2009, ISBN-13: 978-0735627109.
- P. C. Clements, R. Kazman, M. Klein, “Evaluating Software Architectures: Methods and Case Studies,” 1st edition, Addison-Wesley Professional, 323, 2002. ISBN: 0-201-70482-X.
- Kazuki Iehira, Hiroyuki Inooue, "Detection Method and Mitigation of Server-Spoofing Attacks on SOME/IP at the Service Discovery Phase", Advances in Science, Technology and Engineering Systems Journal, vol. 11, no. 1, pp. 25–32, 2026. doi: 10.25046/aj110103
- Shaista Ashraf Farooqi, Aedah Abd Rahman, Amna Saad, "Federated Learning with Differential Privacy and Blockchain for Security and Privacy in IoMT A Theoretical Comparison and Review", Advances in Science, Technology and Engineering Systems Journal, vol. 10, no. 6, pp. 65–76, 2025. doi: 10.25046/aj100606
- Robinson Lawrance, Nishith Kumar Reddy Gorla, "System-Level Test Case Design for Field Reliability Alignment in Complex Products", Advances in Science, Technology and Engineering Systems Journal, vol. 10, no. 6, pp. 55–64, 2025. doi: 10.25046/aj100605
- Vinton Morris, Kevin Kornegay, Joy Falaye, Sean Richardson, Marcial Tienteu, Loic Jephson Djomo Tchuenkou, "TIMeFoRCE: An Identity and Access Management Framework for IoT Devices in A Zero Trust Architecture", Advances in Science, Technology and Engineering Systems Journal, vol. 10, no. 6, pp. 1–22, 2025. doi: 10.25046/aj100601
- Mahdi Madani, El-Bay Bourennane, Safwan El Assad, "Hardware and Secure Implementation of Enhanced ZUC Steam Cipher Based on Chaotic Dynamic S-Box", Advances in Science, Technology and Engineering Systems Journal, vol. 10, no. 1, pp. 37–47, 2025. doi: 10.25046/aj100105
- Diego Costa, Gabriel Matos, Anderson Lins, Leon Barroso, Carlos Aguiar, Erick Bezerra, "Web Application Interface Data Collector for Issue Reporting", Advances in Science, Technology and Engineering Systems Journal, vol. 9, no. 5, pp. 01–08, 2024. doi: 10.25046/aj090501
- Viktor Denkovski, Irena Stojmenovska, Goce Gavrilov, Vladimir Radevski, Vladimir Trajkovik, "Exploring Current Challenges on Security and Privacy in an Operational eHealth Information System", Advances in Science, Technology and Engineering Systems Journal, vol. 9, no. 2, pp. 45–54, 2024. doi: 10.25046/aj090206
- Giwa Abdulgafar Babatunde, Ewetumo Theophilus, Ojo Joseph. Sunday, Adedayo Kayode David, Owolabi Gbenga Ayodele, "Development of a GSM-RC Automated Device for Measuring Mobile Communication Signal Strength and Meteorological Parameters", Advances in Science, Technology and Engineering Systems Journal, vol. 9, no. 1, pp. 149–164, 2024. doi: 10.25046/aj090115
- Gil Hyun Kang, Hwi Jin Kwon, In Soo Chung, Chul Su Kim, "Development and Usability Evaluation of Mobile Augmented Reality Contents for Railway Vehicle Maintenance Training: Air Compressor Case", Advances in Science, Technology and Engineering Systems Journal, vol. 9, no. 1, pp. 91–103, 2024. doi: 10.25046/aj090109
- Fazalur Rehman, Safwan Hashmi, "Enhancing Cloud Security: A Comprehensive Framework for Real-Time Detection, Analysis and Cyber Threat Intelligence Sharing", Advances in Science, Technology and Engineering Systems Journal, vol. 8, no. 6, pp. 107–119, 2023. doi: 10.25046/aj080612
- Hiroki Iwanaga, "Photoluminescence Properties of Eu(III) Complexes with Two Different Phosphine Oxide Structures and Their Potential uses in Micro-LEDs, Security, and Sensing Devices: A Review", Advances in Science, Technology and Engineering Systems Journal, vol. 8, no. 3, pp. 154–160, 2023. doi: 10.25046/aj080317
- Mohammed Mahfuz Hossain, Thomas Ortmeyer, Everett Hall, "Human-Centered Design, Development, and Evaluation of an Interface for a Microgrid Controller", Advances in Science, Technology and Engineering Systems Journal, vol. 8, no. 3, pp. 80–88, 2023. doi: 10.25046/aj080310
- Mario Cuomo, Federica Massimi, Francesco Benedetto, "Detecting CTC Attack in IoMT Communications using Deep Learning Approach", Advances in Science, Technology and Engineering Systems Journal, vol. 8, no. 2, pp. 130–138, 2023. doi: 10.25046/aj080215
- Víctor Manuel Bátiz Beltrán, Ramón Zatarain Cabada, María Lucía Barrón Estrada, Héctor Manuel Cárdenas López, Hugo Jair Escalante, "A Multiplatform Application for Automatic Recognition of Personality Traits in Learning Environments", Advances in Science, Technology and Engineering Systems Journal, vol. 8, no. 2, pp. 30–37, 2023. doi: 10.25046/aj080204
- Richard Romero Izurieta, Segundo Moisés Toapanta Toapanta, Luis Jhony Caucha Morales, María Mercedes Baño Hifóng, Eriannys Zharayth Gómez Díaz, Oscar Marcelo Zambrano Vizuete, Luis Enrique Mafla Gallegos, José Antonio Orizaga Trejo, "Prototype to Identify the Capacity in Cybersecurity Management for a Public Organization", Advances in Science, Technology and Engineering Systems Journal, vol. 8, no. 1, pp. 108–115, 2023. doi: 10.25046/aj080113
- Jittaboon Trichada, Traithep Wimonrut, Narongsak Tirasuntarakul, Eakkachai Pengwang, "Design of an Open Source Anthropomorphic Robotic Hand for Telepresence Robot", Advances in Science, Technology and Engineering Systems Journal, vol. 8, no. 1, pp. 17–29, 2023. doi: 10.25046/aj080103
- El Hadji Malick Ndoye, Ousmane Diallo, Nadir Hakem, Emmanuel Nicolas Cabral, "Interference-Aware Nodes Deployment of a LoRa-Based Architecture for Smart Agriculture in the Southern Region of Senegal", Advances in Science, Technology and Engineering Systems Journal, vol. 7, no. 6, pp. 248–255, 2022. doi: 10.25046/aj070628
- Segundo Moisés Toapanta Toapanta, Rodrigo Humberto Del Pozo Durango, Luis Enrique Mafla Gallegos, Eriannys Zharayth Gómez Díaz, Yngrid Josefina Melo Quintana, Joan Noheli Miranda Jimenez, Ma. Roció Maciel Arellano, José Antonio Orizaga Trejo, "Prototype to Mitigate the Risks, Vulnerabilities and Threats of Information to Ensure Data Integrity", Advances in Science, Technology and Engineering Systems Journal, vol. 7, no. 6, pp. 139–150, 2022. doi: 10.25046/aj070614
- Tarek Nouioua, Ahmed Hafid Belbachir, "The Security of Information Systems and Image Processing Supported by the Quantum Computer: A review", Advances in Science, Technology and Engineering Systems Journal, vol. 7, no. 6, pp. 77–86, 2022. doi: 10.25046/aj070609
- Muhammad Musleh Uddin, Kazi Rafiqul Islam, Md. Monirul Kabir, "An Improved Model to Analyze the Impact of Cyber-Attacks on Power Systems", Advances in Science, Technology and Engineering Systems Journal, vol. 7, no. 5, pp. 27–34, 2022. doi: 10.25046/aj070504
- Kamil Halouzka, Ladislav Burita, Aneta Coufalikova, Pavel Kozak, Petr Františ, "A Comparison of Cyber Security Reports for 2020 of Central European Countries", Advances in Science, Technology and Engineering Systems Journal, vol. 7, no. 4, pp. 105–113, 2022. doi: 10.25046/aj070414
- Ahmed Abdelaziz Elsayed, Mohamed Ahmed Abdellah, Mansour Ahmed Mohamed, Mohamed Abd Elazim Nayel, "µPMU Hardware and Software Design Consideration and Implementation for Distribution Grid Applications", Advances in Science, Technology and Engineering Systems Journal, vol. 7, no. 4, pp. 59–71, 2022. doi: 10.25046/aj070409
- Tiny du Toit, Hennie Kruger, Lynette Drevin, Nicolaas Maree, "Deep Learning Affective Computing to Elicit Sentiment Towards Information Security Policies", Advances in Science, Technology and Engineering Systems Journal, vol. 7, no. 3, pp. 152–160, 2022. doi: 10.25046/aj070317
- Afsah Sharmin, Farhat Anwar, S M A Motakabber, Aisha Hassan Abdalla Hashim, "A Secure Trust Aware ACO-Based WSN Routing Protocol for IoT", Advances in Science, Technology and Engineering Systems Journal, vol. 7, no. 3, pp. 95–105, 2022. doi: 10.25046/aj070311
- Khosro Salmani, Ken Barker, "Leakage-abuse Attacks Against Forward Private Searchable Symmetric Encryption", Advances in Science, Technology and Engineering Systems Journal, vol. 7, no. 2, pp. 156–170, 2022. doi: 10.25046/aj070216
- Kartit Zaid, Diouri Ouafaa, "Taxonomy of Security Techniques for Routing Protocols in Mobile Ad-hoc Networks", Advances in Science, Technology and Engineering Systems Journal, vol. 7, no. 2, pp. 25–31, 2022. doi: 10.25046/aj070203
- Janusz Gurzynski, Lukasz Kajda, Marcin Tarasiuk, Tomasz Samotyjak, Zbigniew Stachowicz, Slawomir Kownacki, "Control and Monitoring Systems in Medium Voltage Distribution Networks in Poland – Current Status and Directions of Development", Advances in Science, Technology and Engineering Systems Journal, vol. 6, no. 6, pp. 112–118, 2021. doi: 10.25046/aj060615
- Osaretin Eboya, Julia Binti Juremi, "iDRP Framework: An Intelligent Malware Exploration Framework for Big Data and Internet of Things (IoT) Ecosystem", Advances in Science, Technology and Engineering Systems Journal, vol. 6, no. 5, pp. 185–202, 2021. doi: 10.25046/aj060521
- Jianhua Yang, Lixin Wang, Yien Wang, "Enhance Student Learning Experience in Cybersecurity Education by Designing Hands-on Labs on Stepping-stone Intrusion Detection", Advances in Science, Technology and Engineering Systems Journal, vol. 6, no. 4, pp. 355–367, 2021. doi: 10.25046/aj060440
- Mykoniati Maria, Lambrinoudakis Costas, "Software Development Lifecycle for Survivable Mobile Telecommunication Systems", Advances in Science, Technology and Engineering Systems Journal, vol. 6, no. 4, pp. 259–277, 2021. doi: 10.25046/aj060430
- Abdulkarim Saleh Masoud Ali, Rozmie Razif Othman, Yasmin Mohd Yacob, Haitham Saleh Ali Ben Abdelmula, "An Efficient Combinatorial Input Output-Based Using Adaptive Firefly Algorithm with Elitism Relations Testing", Advances in Science, Technology and Engineering Systems Journal, vol. 6, no. 4, pp. 223–232, 2021. doi: 10.25046/aj060426
- Valerii Dmitrienko, Serhii Leonov, Aleksandr Zakovorotniy, "New Neural Networks for the Affinity Functions of Binary Images with Binary and Bipolar Components Determining", Advances in Science, Technology and Engineering Systems Journal, vol. 6, no. 4, pp. 91–99, 2021. doi: 10.25046/aj060411
- Rotimi Adediran Ibitomi, Tefo Gordan Sekgweleo, Tiko Iyamu, "Decision Support System for Testing and Evaluating Software in Organizations", Advances in Science, Technology and Engineering Systems Journal, vol. 6, no. 3, pp. 303–310, 2021. doi: 10.25046/aj060334
- Yanshuo Wang, Jim (Jinming) Yang, Ngandu M. Mbiye, "Effectiveness and Suitability of the Automotive EHPS Software Reliability and Testing", Advances in Science, Technology and Engineering Systems Journal, vol. 6, no. 3, pp. 205–212, 2021. doi: 10.25046/aj060323
- Md Mahmudul Hasan, Nafiul Hasan, Dil Afroz, Ferdaus Anam Jibon, Md. Arman Hossen, Md. Shahrier Parvage, Jakaria Sulaiman Aongkon, "Electroencephalogram Based Medical Biometrics using Machine Learning: Assessment of Different Color Stimuli", Advances in Science, Technology and Engineering Systems Journal, vol. 6, no. 3, pp. 27–34, 2021. doi: 10.25046/aj060304
- Anh Nguyen-Duc, Manh-Viet Do, Quan Luong-Hong, Kiem Nguyen-Khac, Hoang Truong-Anh, "On the Combination of Static Analysis for Software Security Assessment – A Case Study of an Open-Source e-Government Project", Advances in Science, Technology and Engineering Systems Journal, vol. 6, no. 2, pp. 921–932, 2021. doi: 10.25046/aj0602105
- Ahmad AA Alkhatib, Abeer Alsabbagh, Randa Maraqa, Shadi Alzubi, "Load Balancing Techniques in Cloud Computing: Extensive Review", Advances in Science, Technology and Engineering Systems Journal, vol. 6, no. 2, pp. 860–870, 2021. doi: 10.25046/aj060299
- Bismark Tei Asare, Kester Quist-Aphetsi, Laurent Nana, "Node-Node Data Exchange in IoT Devices Using Twofish and DHE", Advances in Science, Technology and Engineering Systems Journal, vol. 6, no. 2, pp. 622–628, 2021. doi: 10.25046/aj060271
- Javier E. Sánchez-Galán, Fatima Rangel Barranco, Jorge Serrano Reyes, Evelyn I. Quirós-McIntire, José Ulises Jiménez, José R. Fábrega, "Using Supervised Classification Methods for the Analysis of Multi-spectral Signatures of Rice Varieties in Panama", Advances in Science, Technology and Engineering Systems Journal, vol. 6, no. 2, pp. 552–558, 2021. doi: 10.25046/aj060262
- Celia Chen, Michael Shoga, "A Large Empirical Study on Automatically Classifying Software Maintainability Concerns from Issue Summaries", Advances in Science, Technology and Engineering Systems Journal, vol. 6, no. 2, pp. 161–174, 2021. doi: 10.25046/aj060219
- Ali Alzaed, "Application of a Reusability Approach in Simulation of Heritage Buildings Performance, Taif- Saudi Arabia", Advances in Science, Technology and Engineering Systems Journal, vol. 6, no. 2, pp. 132–138, 2021. doi: 10.25046/aj060216
- Zarina Din, Dian Indrayani Jambari, Maryati Mohd Yusof, Jamaiah Yahaya, "Challenges in IoT Technology Adoption into Information System Security Management of Smart Cities: A Review", Advances in Science, Technology and Engineering Systems Journal, vol. 6, no. 2, pp. 99–112, 2021. doi: 10.25046/aj060213
- Hyeongjoo Kim, Sunyong Byun, "Designing and Applying a Moral Turing Test", Advances in Science, Technology and Engineering Systems Journal, vol. 6, no. 2, pp. 93–98, 2021. doi: 10.25046/aj060212
- Isman Khazi, Andras Kovacs, Ulrich Mescheder, Ali Zahedi, Bahman Azarhoushang, "Fusion of Optical and Microfabricated Eddy-Current Sensors for the Non-Destructive Detection of Grinding Burn", Advances in Science, Technology and Engineering Systems Journal, vol. 6, no. 1, pp. 1414–1421, 2021. doi: 10.25046/aj0601160
- Akram Ajouli, "SEA: An UML Profile for Software Evolution Analysis in Design Phase", Advances in Science, Technology and Engineering Systems Journal, vol. 6, no. 1, pp. 1334–1342, 2021. doi: 10.25046/aj0601153
- Rosula Reyes, Justine Cris Borromeo, Derrick Sze, "Performance Evaluation of a Gamified Physical Rehabilitation Balance Platform through System Usability and Intrinsic Motivation Metrics", Advances in Science, Technology and Engineering Systems Journal, vol. 6, no. 1, pp. 1164–1170, 2021. doi: 10.25046/aj0601131
- Saliha Assoul, Anass Rabii, Ounsa Roudiès, "An Operational Responsibility and Task Monitoring Method: A Data Breach Case Study", Advances in Science, Technology and Engineering Systems Journal, vol. 6, no. 1, pp. 1157–1163, 2021. doi: 10.25046/aj0601130
- Lesia Marushchak, Olha Pavlykivska, Galyna Liakhovych, Oksana Vakun, Nataliia Shveda, "Accounting Software in Modern Business", Advances in Science, Technology and Engineering Systems Journal, vol. 6, no. 1, pp. 862–870, 2021. doi: 10.25046/aj060195
- Amin S. Ibrahim, Khaled Y Youssef, Mohamed Abouelatta, "Traffic Aggregation Techniques for Optimizing IoT Networks", Advances in Science, Technology and Engineering Systems Journal, vol. 6, no. 1, pp. 509–518, 2021. doi: 10.25046/aj060156
- Arman Mirmanov, Aidar Alimbayev, Sanat Baiguanysh, Nabi Nabiev, Askar Sharipov, Azamat Kokcholokov, Diego Caratelli, "Development of an IoT Platform for Stress-Free Monitoring of Cattle Productivity in Precision Animal Husbandry", Advances in Science, Technology and Engineering Systems Journal, vol. 6, no. 1, pp. 501–508, 2021. doi: 10.25046/aj060155
- Devika K N, Ramesh Bhakthavatchalu, "Modified Blockchain based Hardware Paradigm for Data Provenance in Academia", Advances in Science, Technology and Engineering Systems Journal, vol. 6, no. 1, pp. 66–77, 2021. doi: 10.25046/aj060108
- Pranay Bhardwaj, Carla Purdy, Nawar Obeidat, "A Novel Way to Design ADS-B using UML and TLA+ with Security as a Focus", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 6, pp. 1657–1665, 2020. doi: 10.25046/aj0506197
- Wooyoung Kim, Yi-Hsin Hsu, Zican Li, Preston Mar, Yangxiao Wang, "NemoSuite: Web-based Network Motif Analytic Suite", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 6, pp. 1545–1553, 2020. doi: 10.25046/aj0506185
- Bilal Babayigit, Eda Nur Hascokadar, "A Software-Defined Network Approach for The Best Hospital Localization Against Coronavirus (COVID-19)", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 6, pp. 1537–1544, 2020. doi: 10.25046/aj0506184
- Omar Khaled Barakat, Ahmed El-Biomey Mansour, Mahmoud Mohamed Abd Elrazik, Ashraf Aboshosha, Amir Yassin Hassan, "Simulation Based Energy Consumption Optimization for Buildings by Using Various Energy Saving Methods", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 6, pp. 1480–1487, 2020. doi: 10.25046/aj0506178
- Hesham Aly El Zouka, Mustafa Mohamed Hosni, "Time Granularity-based Privacy Protection for Cloud Metering Systems", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 6, pp. 1278–1285, 2020. doi: 10.25046/aj0506152
- Jong-Wouk Kim, Jiwon Bang, Mi-Jung Choi, "Defeating Anti-Debugging Techniques for Malware Analysis Using a Debugger", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 6, pp. 1178–1189, 2020. doi: 10.25046/aj0506142
- Boughanja Manale, Tomader Mazri, "5G, Vehicle to Everything Communication: Opportunities, Constraints and Future Directions", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 6, pp. 1089–1095, 2020. doi: 10.25046/aj0506132
- Issam Jebreen, "An Analysts’ Skills: Bespoke Software vs Packaged Software at Small Software Vendors", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 6, pp. 1021–1026, 2020. doi: 10.25046/aj0506123
- Seth Alornyo, Mustapha Adamu Mohammed, Francis Botchey, Collinson Colin M. Agbesi, "Mobile Money Wallet Attack Resistance using ID-based Signcryption Cryptosystem with Equality Test", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 6, pp. 988–994, 2020. doi: 10.25046/aj0506118
- Nagaraj Vannal, Saroja V Siddamal, "Design and Implementation of DFT Technique to Verify LBIST at RTL Level", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 6, pp. 937–943, 2020. doi: 10.25046/aj0506111
- Abdulla Obaid Al Zaabi, Chan Yeob Yeun, Ernesto Damiani, Gaemyoung, "An Enhanced Conceptual Security Model for Autonomous Vehicles", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 6, pp. 853–864, 2020. doi: 10.25046/aj0506102
- Nelson Russo, Leonilde Reis, "Updated Analysis of Business Continuity Issues Underlying the Certification of Invoicing Software, Considering a Pandemic Scenario", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 6, pp. 845–852, 2020. doi: 10.25046/aj0506101
- Ismail Ktata, Naoufel Kharroubi, "A Model-Driven Approach for Reconfigurable Systems Development", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 6, pp. 801–810, 2020. doi: 10.25046/aj050695
- Arooba Shahoor, Rida Shaukat, Sumaira Sultan Minhas, Hina Awan, Kashif Saghar, "SharpniZer: A C# Static Code Analysis Tool for Mission Critical Systems", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 6, pp. 561–570, 2020. doi: 10.25046/aj050668
- Andre Figliuolo da Cruz, Cristiano Pereira Godoy, Lanier Menezes dos Santos, Lucas Frota Marinho, Marco Santarelle Jardim, Elisangela Paiva da Silva, C ́ıcero Augusto Pahins, Paulo Fonseca, Felipe Taliar Giuntini, "Blueprint Model: An Agile-Oriented Methodology for Tackling Global Software Development Challenges", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 6, pp. 353–362, 2020. doi: 10.25046/aj050643
- Jim Scheibmeir, Yashwant Malaiya, "Multi-Model Security and Social Media Analytics of the Digital Twin", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 6, pp. 323–330, 2020. doi: 10.25046/aj050639
- Oswaldo René Banda-Sayco, "Infrared Uplink Implementation for Software Defined Visible Light Communication Systems", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 6, pp. 127–132, 2020. doi: 10.25046/aj050614
- Sergiy Kostrikov, Rostyslav Pudlo, Dmytro Bubnov, Vladimir Vasiliev, Yury Fedyay, "Automated Extraction of Heavyweight and Lightweight Models of Urban Features from LiDAR Point Clouds by Specialized Web-Software", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 6, pp. 72–95, 2020. doi: 10.25046/aj050609
- Ihsan Mizher Baht, Petre Marian Nicolae, Ileana Diana, Nameer Baht, "Analysis of Green Building Effect on Micro grid Based on Potential Energy Savings and BIM", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 6, pp. 30–35, 2020. doi: 10.25046/aj050604
- Marika Fanesi, David Scaradozzi, "Advanced Control Strategies on Nonlinear Testbench Dynamometer System for Simulating the Fuel Consumption", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 5, pp. 1172–1183, 2020. doi: 10.25046/aj0505142
- Yanfi Yanfi, Yogi Udjaja, Azani Cempaka Sari, "User’s Demographic Characteristic on the Evaluation of Gamification Interactive Typing for Primary School Visually Impaired with System Usability Scale", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 5, pp. 876–881, 2020. doi: 10.25046/aj0505107
- Sattar Othman Hasan, Sevan Siyyah Abdullah, "Path Loss Estimation for Some Korek-Telecom Sites Operating at (1.8) GHz and (2.1) GHz for Urban and Suburban Area in Erbil City", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 5, pp. 869–875, 2020. doi: 10.25046/aj0505106
- Basavaraj Rabakavi, Saroja V Siddamal, "Design and Implementation of Quad-Site Testing on FPGA Platform", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 5, pp. 789–798, 2020. doi: 10.25046/aj050596
- Kofi Osei-Tutu, Yeong-Tae Song, "Enterprise Architecture Institutionalization for Health Information Exchange (HIE) Cloud Migration", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 5, pp. 680–691, 2020. doi: 10.25046/aj050584
- Gautama Wijaya, Nico Surantha, "Multi-layered Security Design and Evaluation for Cloud-based Web Application: Case Study of Human Resource Management System", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 5, pp. 674–679, 2020. doi: 10.25046/aj050583
- Mika Karjalainen, Tero Kokkonen, "Review of Pedagogical Principles of Cyber Security Exercises", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 5, pp. 592–600, 2020. doi: 10.25046/aj050572
- Lambe Mutalub Adesina, Ademola Abdulkareem, James Katende, Olaosebikan Fakolujo, "Newton-Raphson Algorithm as a Power Utility Tool for Network Stability", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 5, pp. 444–451, 2020. doi: 10.25046/aj050555
- Liana Khamis Qabajeh, Mohammad Moustafa Qabajeh, "Detailed Security Evaluation of ARANz, ARAN and AODV Protocols", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 5, pp. 176–192, 2020. doi: 10.25046/aj050523
- Pham Minh Nam, Phu Tran Tin, "Analysis of Security-Reliability Trade-off for Multi-hop Cognitive Relaying Protocol with TAS/SC Technique", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 5, pp. 54–62, 2020. doi: 10.25046/aj050508
- Adamu Abdullahi Garba, Maheyzah Muhamad Siraj, Siti Hajar Othman, "An Explanatory Review on Cybersecurity Capability Maturity Models", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 4, pp. 762–769, 2020. doi: 10.25046/aj050490
- Matthew Oluwole Arowolo, Adefemi Adeyemi Adekunle, Martins Oluwaseun Opeyemi, "Design and Implementation of a PLC Trainer Workstation", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 4, pp. 755–761, 2020. doi: 10.25046/aj050489
- Vu Nguyen Hoa Hong, Luong Tuan Anh, "Development Trends of Smart Cities in the Future – Potential Security Risks and Responsive Solutions", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 4, pp. 548–556, 2020. doi: 10.25046/aj050465
- Marco Bindi, Igor Aizenberg, Riccardo Belardi, Francesco Grasso, Antonio Luchetta, Stefano Manetti, Maria Cristina Piccirilli, "Neural Network-Based Fault Diagnosis of Joints in High Voltage Electrical Lines", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 4, pp. 488–498, 2020. doi: 10.25046/aj050458
- Yogi Udjaja, "Entertainment Technology: Dynamic Game Production", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 4, pp. 203–206, 2020. doi: 10.25046/aj050425
- Jim Scheibmeir, Yashwant Malaiya, "Contextualization of the Augmented Reality Quality Model through Social Media Analytics", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 4, pp. 184–191, 2020. doi: 10.25046/aj050422
- Maximo Giovani Tanzado Espinoza, Joseline Roxana Neira Melendrez, Luis Antonio Neira Clemente, "A Survey and an IoT Cybersecurity Recommendation for Public and Private Hospitals in Ecuador", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 3, pp. 518–528, 2020. doi: 10.25046/aj050364
- Mainar Swari Mahardika, Achmad Nizar Hidayanto, Putu Agya Paramartha, Louis Dwysevrey Ompusunggu, Rahmatul Mahdalina, Farid Affan, "Measurement of Employee Awareness Levels for Information Security at the Center of Analysis and Information Services Judicial Commission Republic of Indonesia", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 3, pp. 501–509, 2020. doi: 10.25046/aj050362
- Suchitra Abel, Yenchih Tang, Jake Singh, Ethan Paek, "Applications of Causal Modeling in Cybersecurity: An Exploratory Approach", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 3, pp. 380–387, 2020. doi: 10.25046/aj050349
- Kartono Kartono, Purwanto Purwanto, Suripin Suripin, "Analysis of Local Rainfall Characteristics as a Mitigation Strategy for Hydrometeorology Disaster in Rain-fed Reservoirs Area", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 3, pp. 299–305, 2020. doi: 10.25046/aj050339
- Gillala Rekha, Shaveta Malik, Amit Kumar Tyagi, Meghna Manoj Nair, "Intrusion Detection in Cyber Security: Role of Machine Learning and Data Mining in Cyber Security", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 3, pp. 72–81, 2020. doi: 10.25046/aj050310
- Bambang Leo Handoko, Nada Ayuanda, Ari Tihar Marpaung, "Organizational, Social and Individual Aspect on Acceptance of Computerized Audit in Financial Audit Work", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 3, pp. 55–61, 2020. doi: 10.25046/aj050308
- Segundo Moisés Toapanta Toapanta, Daniela Monserrate Moreira Gamboa, Luis Enrique Mafla Gallegos, "Analysis of the Blockchain for Adoption in Electronic Commerce Management in Ecuador", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 2, pp. 762–768, 2020. doi: 10.25046/aj050295
- Farirai Chitsa, Tiko Iyamu, "Towards Enterprise Technical Architecture for the Implementation of the South African NHI", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 2, pp. 724–729, 2020. doi: 10.25046/aj050290
- Segundo Moisés Toapanta Toapanta, Andrés Aurelio García Henriquez, Luis Enrique Mafla Gallegos, "Analysis of Vulnerabilities, Risks and Threats in the Process of Quota Allocation for the State University of Ecuador", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 2, pp. 673–682, 2020. doi: 10.25046/aj050283
- Ishaq Sider, Khaled Sider, "Evaluation of Vapor Jet Refrigeration Cycle Driven by Solar Thermal Energy for Air Conditioning Applications: Case Study", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 2, pp. 646–652, 2020. doi: 10.25046/aj050280
- Emmanuel Peters, George Kwamina Aggrey, "An ISO 25010 Based Quality Model for ERP Systems", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 2, pp. 578–583, 2020. doi: 10.25046/aj050272
- Lylia Alouache, Mohamed Maachaoui, Rachid Chelouah, "Securing Hybrid SDN-based Geographic Routing Protocol using a Distributed Trust Model", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 2, pp. 567–577, 2020. doi: 10.25046/aj050271
- Arthur James Swart, Pierre Eduard Hertzog, "Promoting Continuous Professional Development Among Academics from A Vocational College by Using A Practical Workshop Based on Arduino Technology", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 2, pp. 452–459, 2020. doi: 10.25046/aj050258
- Diego Iquira-Becerra, Michael Flores-Conislla, Juan Deyby Carlos-Chullo, Briseida Sotelo-Castro, Claudia Payalich-Quispe, Carlo Corrales-Delgado, "A Critical Analysis of Usability and Learning Methods on an Augmented Reality Application for Zoology Education", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 2, pp. 384–392, 2020. doi: 10.25046/aj050250